220-1102 Exam Details
-
Exam Code
:220-1102 -
Exam Name
:CompTIA A+ Certification: Core 2 -
Certification
:CompTIA Certifications -
Vendor
:CompTIA -
Total Questions
:916 Q&As -
Last Updated
:Jan 27, 2026
CompTIA 220-1102 Online Questions & Answers
-
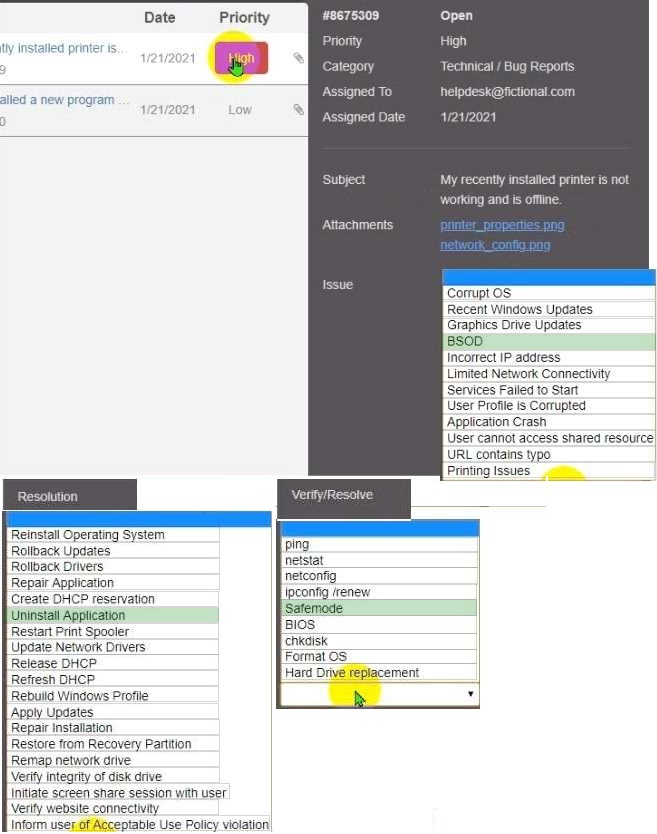
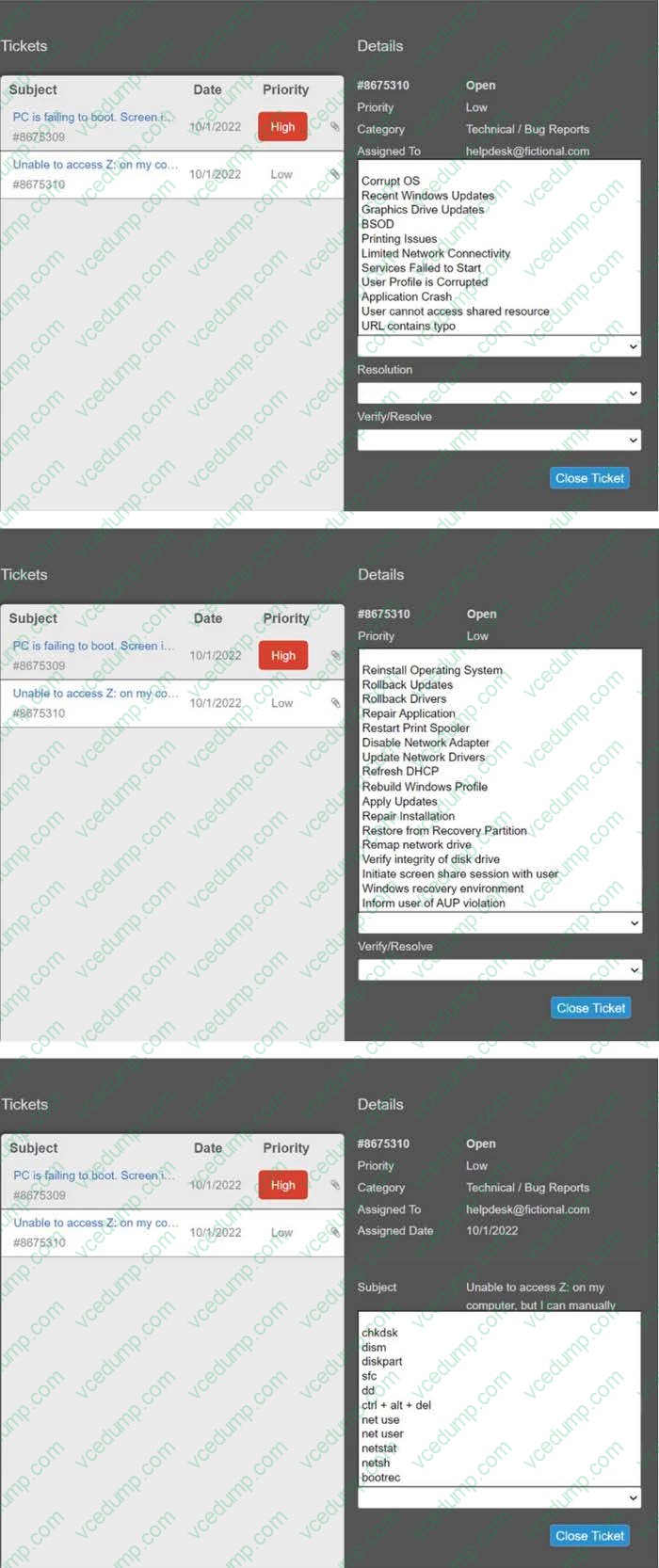
Question 1:
HOTSPOT
Welcome to your first day as a Fictional Company. LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
Click on individual tickers to see the ticket details. View attachments to determine the problem. Select the appropriate issue from the 'issue' drop-down menu. Then, select the MOST efficient resolution from the 'Resolution' drop-down menu.
Finally, select the proper command or verification to remediate or confirm your fix of the issue from the Verify Resolve drop-down menu.
-
Question 2:
DRAG DROP
A customer recently experienced a power outage at a SOHO.
The customer does not think the components are connected properly.
A print job continued running for several minutes after the power failed, but the customer was not able to interact with the computer.
Once the UPS stopped beeping, all functioning devices also turned off.
In case of a future power failure, the customer wants to have the most time available to save cloud documents and shut down the computer without losing any data.
Select and Place:

-
Question 3:
DRAG DROP
A technician has verified that Joe, a user, has a malware infection on his desktop. Drag and drop the following malware remediation techniques in the correct order Joe should follow to alleviate this issue.
Select and Place:

-
Question 4:
SIMULATION
You have been contacted through the help desk chat application. A user is setting up a replacement SOHO router. Assist the user with setting up the router.
INSTRUCTIONS
Select the most appropriate statement for each response. Click the SEND button after each response to continue the chat. If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
-
Question 5:
SIMULATION
Multiple users are reporting audio issues as well as performance issues after downloading unauthorized software. You have been dispatched to identify and resolve any issues on the network using best practice procedures.
INSTRUCTIONS
Quarantine and configure the appropriate device(s) so that the users' audio issues are
resolved using best practice procedures.
Multiple devices may be selected for quarantine.
Click on a host or server to configure services.

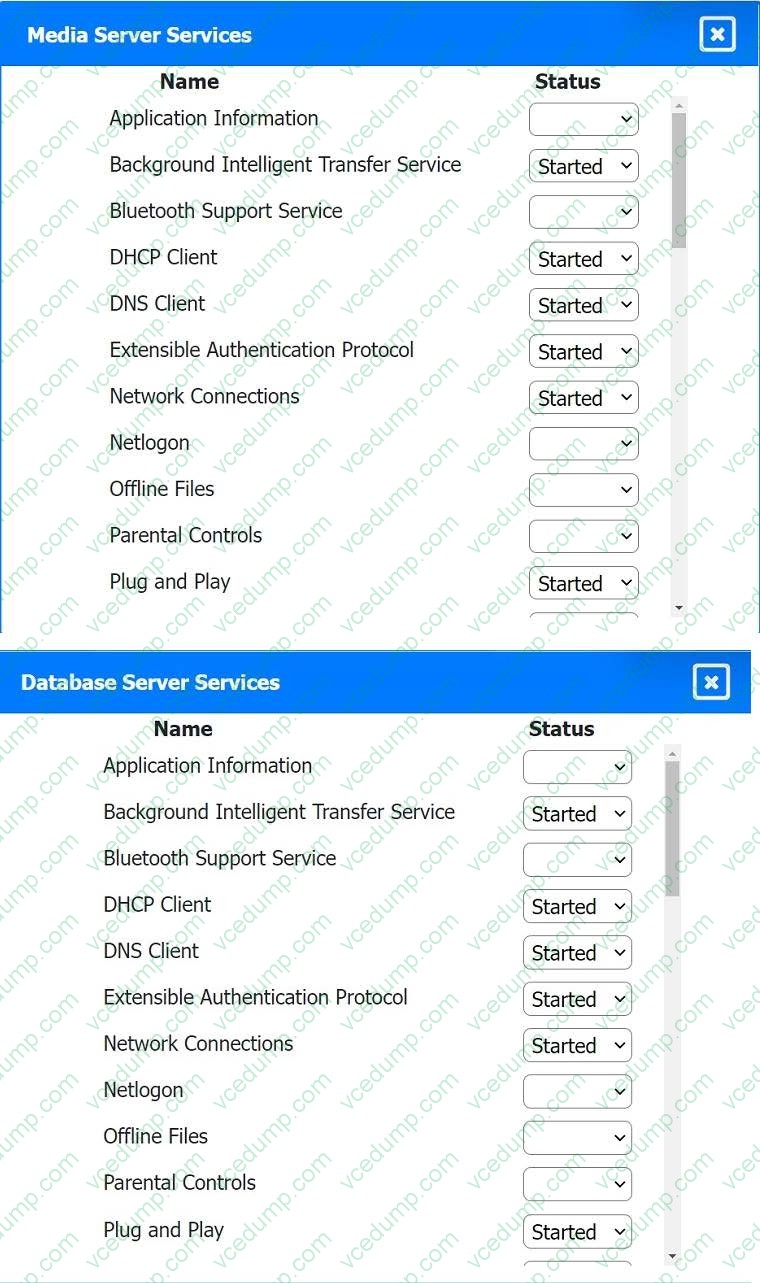
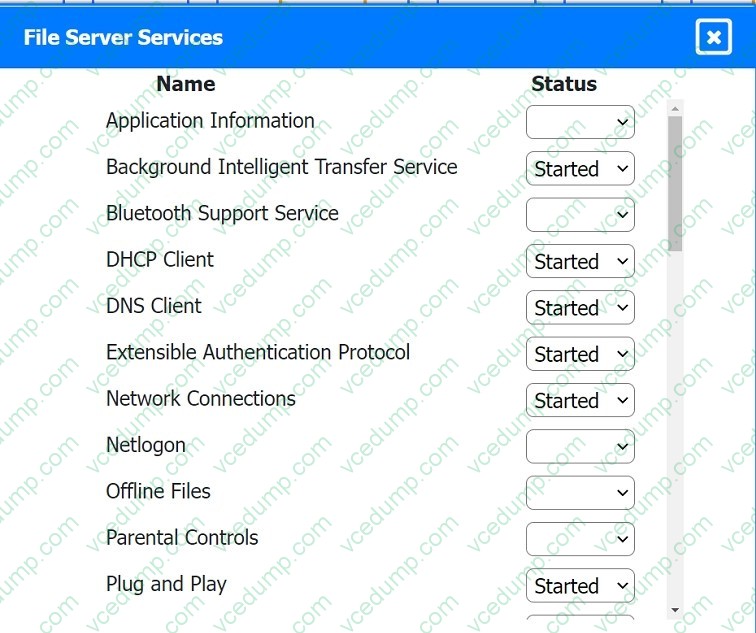
-
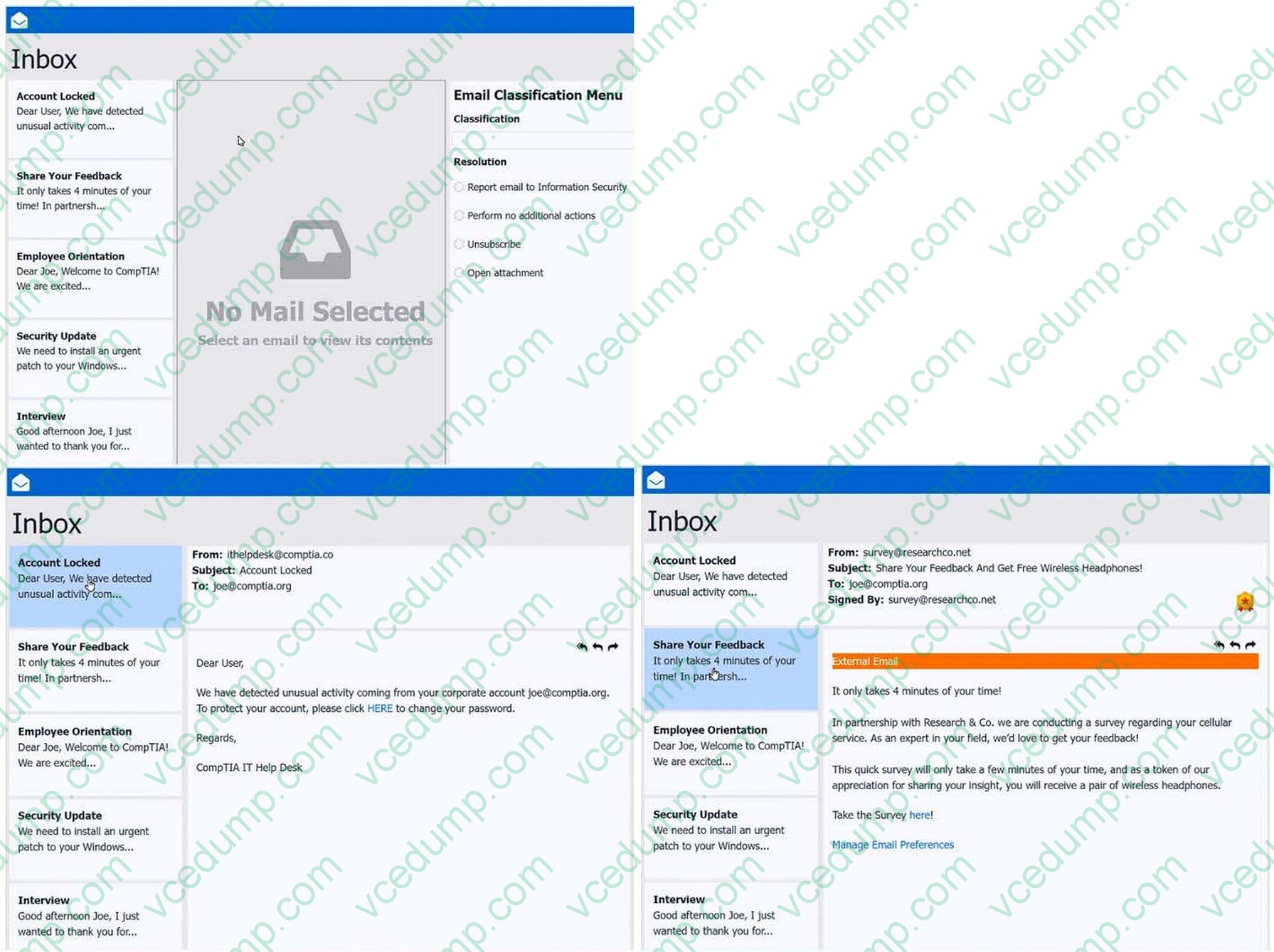
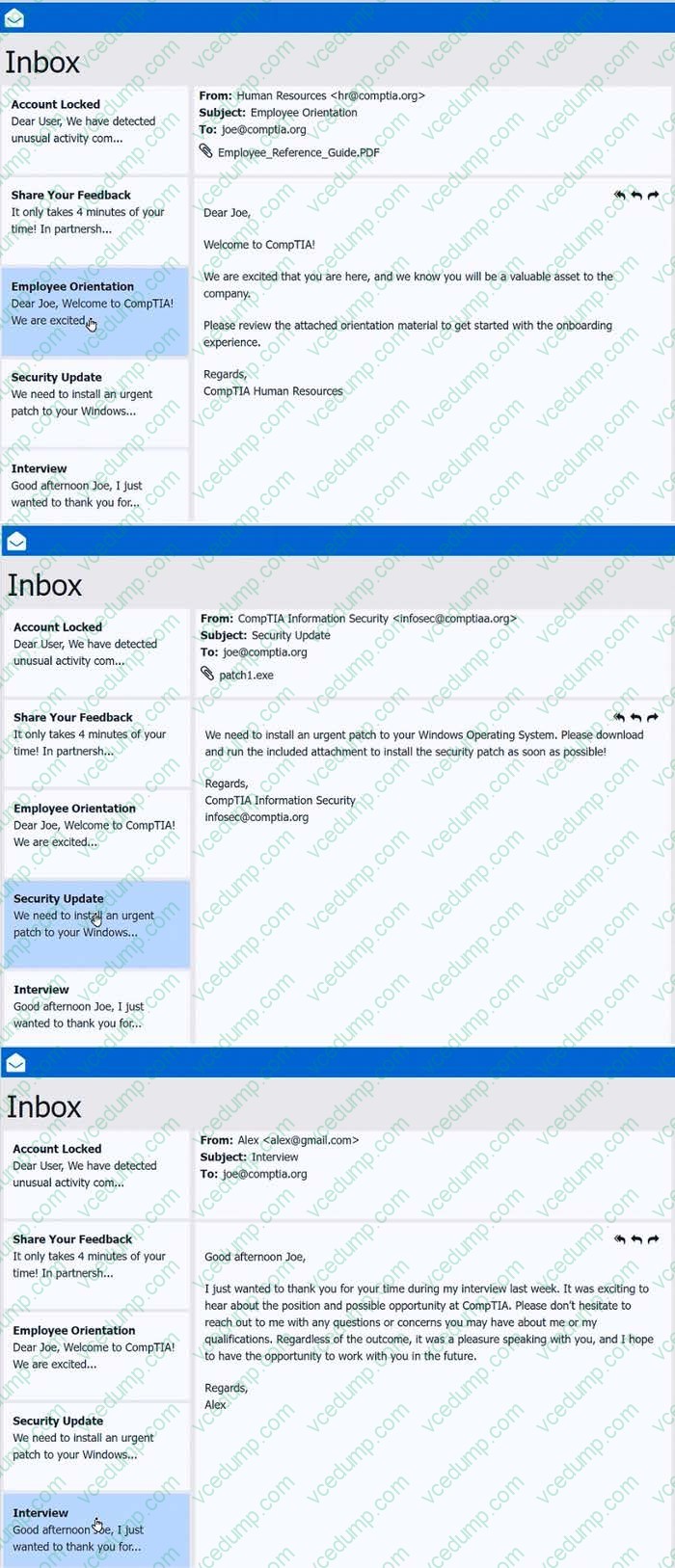
Question 6:
SIMULATION
As a corporate technician, you are asked to evaluate several suspect email messages on a client's computer. Corporate policy requires the following:
1. All phishing attempts must be reported.
2. Future spam emails to users must be prevented.
INSTRUCTIONS
Review each email and perform the following within the email:
1. Classify the emails
2. Identify suspicious items, if applicable, in each email
3. Select the appropriate resolution
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
-
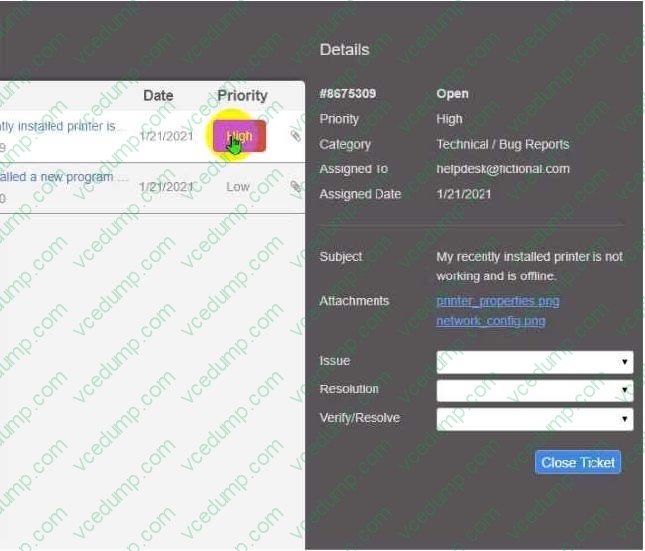
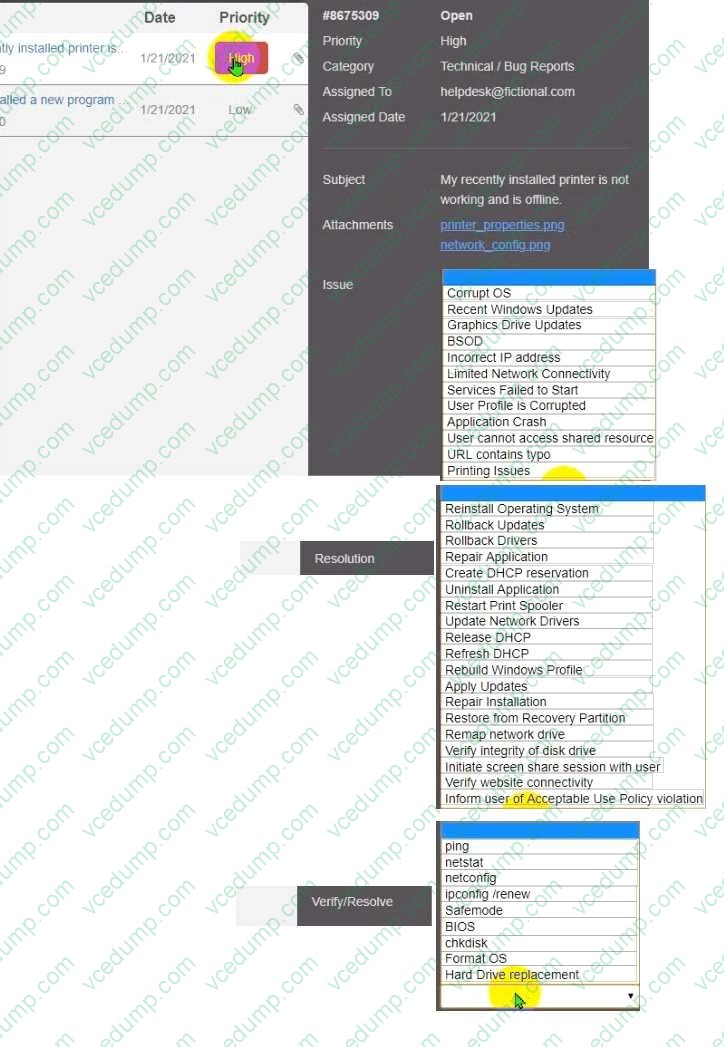
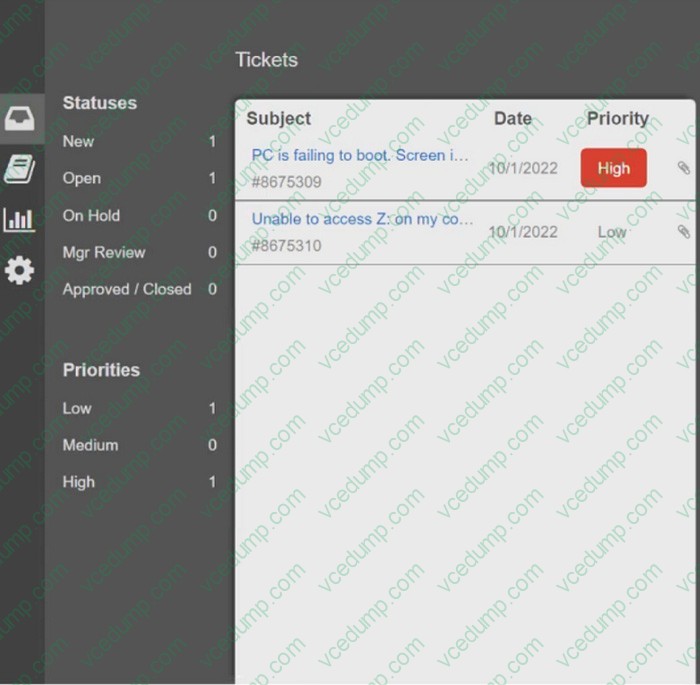
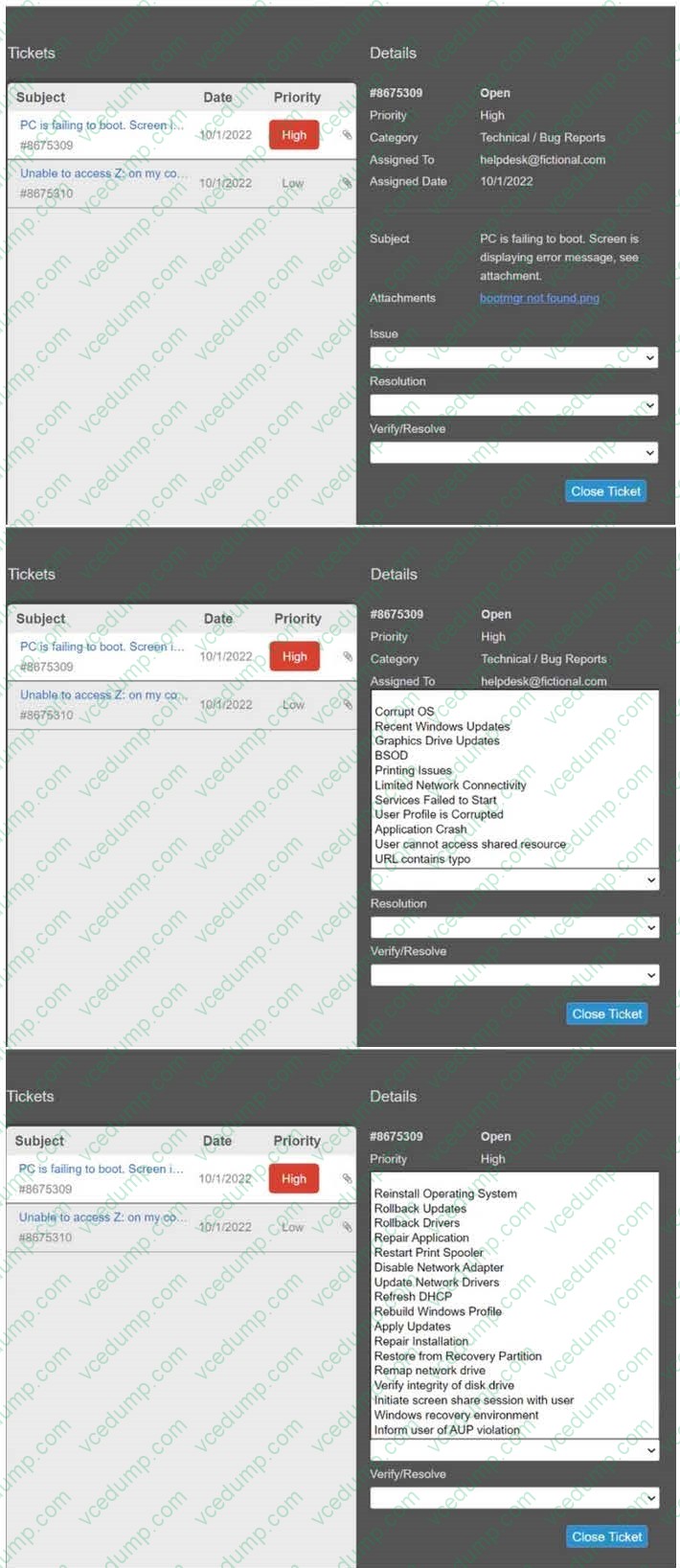
Question 7:
SIMULATION
Welcome to your first day as a Fictional Company. LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue. Click on individual tickers to see the ticket details. View attachments to determine the problem.
Select the appropriate issue from the 'issue' drop-down menu. Then, select the MOST efficient resolution from the 'Resolution' drop-down menu. Finally, select the proper command or verification to remediate or confirm your fix of the issue from the Verify Resolve drop-down menu.
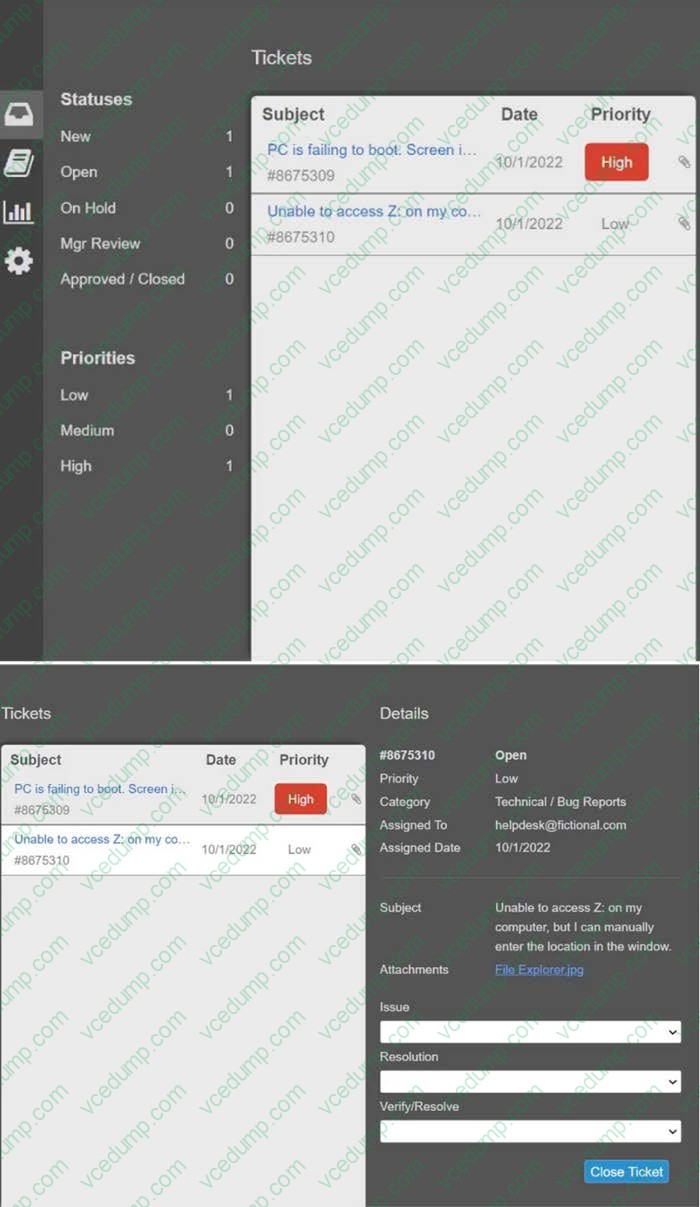
-
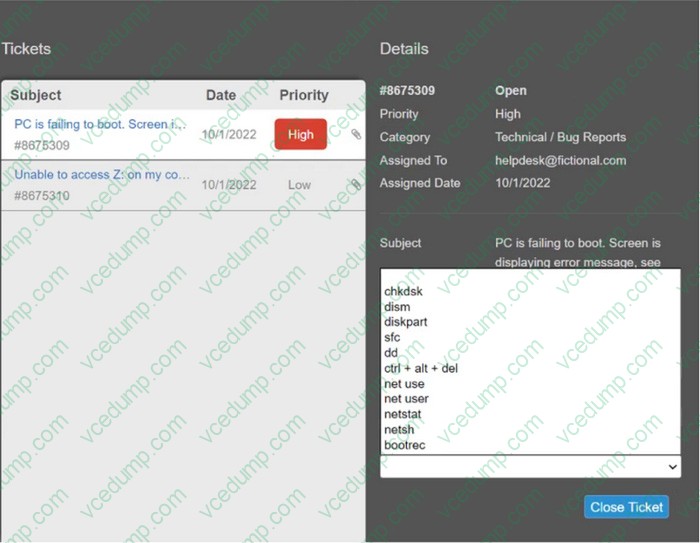
Question 8:
SIMULATION
Welcome to your first day as a Fictional Company. LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue. Click on individual tickers to see the ticket details. View attachments to determine the problem.
Select the appropriate issue from the 'issue' drop-down menu. Then, select the MOST efficient resolution from the 'Resolution' drop-down menu. Finally, select the proper command or verification to remediate or confirm your fix of the issue from the Verify Resolve drop-down menu.
-
Question 9:
SIMULATION
Two components of Genericware2.0 are causing performance issues on a Windows 7 PC. One Generic 2.0 component is currently not responding and needs to be disabled upon reboot. To prevent further performance issues ensure both
components are no longer running upon reboot, without making any other changes to the current system or without deleting registry keys or shortcuts.
Instructions: When you have completed the simulation, please select the done button to submit your answer.
-
Question 10:
SIMULATION
Every time it is rebooted, the message "BOOTMGR is missing" appears. You have previously inserted a Windows 7 installation DVD into the DVD-ROM. Please repair this failure without overwriting the customers' local user profiles.
Instructions:
1. Launch the simulation to repair the failure
2. Type Help in command line to show list of available commands
3. When you have completed the simulation, please select the done button.

Related Exams:
-
220-1001
CompTIA A+ Certification: Core 1 -
220-1002
CompTIA A+ Certification: Core 2 -
220-1101
CompTIA A+ Certification: Core 1 -
220-1102
CompTIA A+ Certification: Core 2 -
220-1201
CompTIA A+ Certification: Core 1 -
220-1202
CompTIA A+ Certification: Core 2 -
220-902
CompTIA A+ Certification -
CAS-004
CompTIA Advanced Security Practitioner (CASP+) -
CAS-005
CompTIA SecurityX -
CLO-001
CompTIA Cloud Essentials+
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 220-1102 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.