CEH-001 Exam Details
-
Exam Code
:CEH-001 -
Exam Name
:Certified Ethical Hacker (CEH) -
Certification
:GAQM Certifications -
Vendor
:GAQM -
Total Questions
:878 Q&As -
Last Updated
:May 30, 2026
GAQM CEH-001 Online Questions & Answers
-
Question 731:
Which one of the following attacks will pass through a network layer intrusion detection system undetected?
A. A teardrop attack
B. A SYN flood attack
C. A DNS spoofing attack
D. A test.cgi attack -
Question 732:
Which of the following resources does NMAP need to be used as a basic vulnerability scanner covering several vectors like SMB, HTTP and FTP?
A. Metasploit scripting engine
B. Nessus scripting engine
C. NMAP scripting engine
D. SAINT scripting engine -
Question 733:
Which of the following levels of algorithms does Public Key Infrastructure (PKI) use?
A. RSA 1024 bit strength
B. AES 1024 bit strength
C. RSA 512 bit strength
D. AES 512 bit strength -
Question 734:
Scanning for services is an easy job for Bob as there are so many tools available from the Internet. In order for him to check the vulnerability of XYZ, he went through a few scanners that are currently available. Here are the scanners that he uses:
1.
Axent's NetRecon (http://www.axent.com)
2.
SARA, by Advanced Research Organization (http://www-arc.com/sara)
3.
VLAD the Scanner, by Razor (http://razor.bindview.com/tools/)
However, there are many other alternative ways to make sure that the services that have been scanned will be more accurate and detailed for Bob.
What would be the best method to accurately identify the services running on a victim host?
A. Using Cheops-ng to identify the devices of XYZ.
B. Using the manual method of telnet to each of the open ports of XYZ.
C. Using a vulnerability scanner to try to probe each port to verify or figure out which service is running for XYZ.
D. Using the default port and OS to make a best guess of what services are running on each port for XYZ. -
Question 735:
This is an example of whois record.
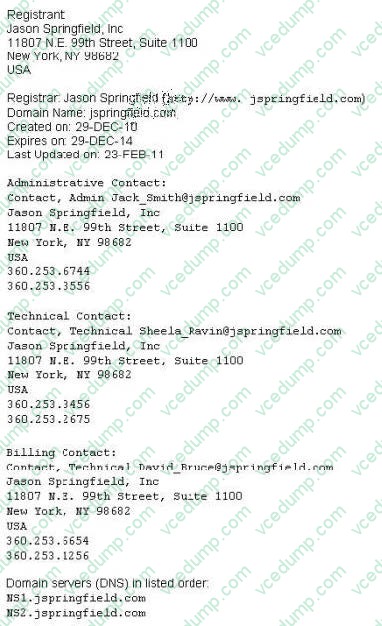
Sometimes a company shares a little too much information on their organization through public domain records. Based on the above whois record, what can an attacker do? (Select 2 answers)
A. Search engines like Google, Bing will expose information listed on the WHOIS record
B. An attacker can attempt phishing and social engineering on targeted individuals using the information from WHOIS record
C. Spammers can send unsolicited e-mails to addresses listed in the WHOIS record
D. IRS Agents will use this information to track individuals using the WHOIS record information -
Question 736:
Which of the following guidelines or standards is associated with the credit card industry?
A. Control Objectives for Information and Related Technology (COBIT)
B. Sarbanes-Oxley Act (SOX)
C. Health Insurance Portability and Accountability Act (HIPAA)
D. Payment Card Industry Data Security Standards (PCI DSS) -
Question 737:
Virus Scrubbers and other malware detection program can only detect items that they are aware of. Which of the following tools would allow you to detect unauthorized changes or modifications of binary files on your system by unknown malware?
A. System integrity verification tools
B. Anti-Virus Software
C. A properly configured gateway
D. There is no way of finding out until a new updated signature file is released -
Question 738:
Which of the following is used to indicate a single-line comment in structured query language (SQL)?
A. -
B. ||
C. %%
D. '' -
Question 739:
Which of the following processes of PKI (Public Key Infrastructure) ensures that a trust relationship exists and that a certificate is still valid for specific operations?
A. Certificate issuance
B. Certificate validation
C. Certificate cryptography
D. Certificate revocation -
Question 740:
You want to know whether a packet filter is in front of 192.168.1.10. Pings to 192.168.1.10 don't get answered. A basic nmap scan of 192.168.1.10 seems to hang without returning any information. What should you do next?
A. Run NULL TCP hping2 against 192.168.1.10
B. Run nmap XMAS scan against 192.168.1.10
C. The firewall is blocking all the scans to 192.168.1.10
D. Use NetScan Tools Pro to conduct the scan
Related Exams:
-
APM-001
Certified Associate in Project Management (APM) -
BMP-001
Certified Business Management Professional (BMP) -
BPM-001
Certified Business Process Manager (BPM) -
CAMT-001
IMTQN Certified Advanced Mobile Tester (CAMT) -
CBAF-001
Certified Business Analyst - Foundation -
CBCP-002
Certified Business Continuity Professional (CBCP) -
CCCP-001
Certified Cloud Computing Professional (CCCP) -
CDCP-001
Certified Data Centre Professional (CDCP) -
CEH-001
Certified Ethical Hacker (CEH) -
CFA-001
Certified Forensic Analyst (CFA)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only GAQM exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CEH-001 exam preparations and GAQM certification application, do not hesitate to visit our Vcedump.com to find your solutions here.