312-50V7 Exam Details
-
Exam Code
:312-50V7 -
Exam Name
:Ethical Hacking and Countermeasures (CEHv7) -
Certification
:EC-COUNCIL Certifications -
Vendor
:EC-COUNCIL -
Total Questions
:514 Q&As -
Last Updated
:May 31, 2026
EC-COUNCIL 312-50V7 Online Questions & Answers
-
Question 391:
In Trojan terminology, what is a covert channel?
A. A channel that transfers information within a computer system or network in a way that violates the security policy
B. A legitimate communication path within a computer system or network for transfer of data
C. It is a kernel operation that hides boot processes and services to mask detection
D. It is Reverse tunneling technique that uses HTTPS protocol instead of HTTP protocol to establish connections -
Question 392:
A Security Engineer at a medium-sized accounting firm has been tasked with discovering how much information can be obtained from the firm's public facing web servers. The engineer decides to start by using netcat to port 80. The engineer receives this output:
HTTP/1.1 200 OK Server: Microsoft-IIS/6 Expires: Tue, 17 Jan 2011 01:41:33 GMT DatE. Mon, 16 Jan 2011 01:41:33 GMT Content-TypE. text/html Accept-Ranges: bytes Last-ModifieD. Wed, 28 Dec 2010 15:32:21 GMT ETaG. "b0aac0542e25c31:89d" Content-Length: 7369
Which of the following is an example of what the engineer performed?
A. Cross-site scripting
B. Banner grabbing
C. SQL injection
D. Whois database query -
Question 393:
A penetration tester is attempting to scan an internal corporate network from the internet without alerting the border sensor. Which is the most efficient technique should the tester consider using?
A. Spoofing an IP address
B. Tunneling scan over SSH
C. Tunneling over high port numbers
D. Scanning using fragmented IP packets -
Question 394:
During a penetration test, the tester conducts an ACK scan using NMAP against the external interface of the DMZ firewall. NMAP reports that port 80 is unfiltered. Based on this response, which type of packet inspection is the firewall conducting?
A. Host
B. Stateful
C. Stateless
D. Application -
Question 395:
A security engineer is attempting to map a company's internal network. The engineer enters in the following NMAP commanD.
NMAP n sS P0 p 80 ***.***.**.**
What type of scan is this?
A. Quick scan
B. Intense scan
C. Stealth scan
D. Comprehensive scan -
Question 396:

An attacker finds a web page for a target organization that supplies contact information for the company. Using available details to make the message seem authentic, the attacker drafts e-mail to an employee on the contact page that
appears to come from an individual who might reasonably request confidential information, such as a network administrator.
The email asks the employee to log into a bogus page that requests the employee's user name and password or click on a link that will download spyware or other malicious programming.
Google's Gmail was hacked using this technique and attackers stole source code and sensitive data from Google servers. This is highly sophisticated attack using zero-day exploit vectors, social engineering and malware websites that
focused on targeted individuals working for the company.
What is this deadly attack called?
A. Spear phishing attack
B. Trojan server attack
C. Javelin attack
D. Social networking attack -
Question 397:
A hacker was able to sniff packets on a company's wireless network. The following information was discovereD.
The Key 10110010 01001011 The Cyphertext 01100101 01011010 Using the Exlcusive OR, what was the original message?
A. 00101000 11101110
B. 11010111 00010001
C. 00001101 10100100
D. 11110010 01011011 -
Question 398:
Which of the following is a primary service of the U.S. Computer Security Incident Response Team (CSIRT)?
A. CSIRT provides an incident response service to enable a reliable and trusted single point of contact for reporting computer security incidents worldwide.
B. CSIRT provides a computer security surveillance service to supply a government with important intelligence information on individuals travelling abroad.
C. CSIRT provides a penetration testing service to support exception reporting on incidents worldwide by individuals and multi-national corporations.
D. CSIRT provides a vulnerability assessment service to assist law enforcement agencies with profiling an individual's property or company's asset. -
Question 399:
Bank of Timbuktu is a medium-sized, regional financial institution in Timbuktu. The bank has deployed a new Internet-accessible Web application recently. Customers can access their account balances, transfer money between accounts, pay bills and conduct online financial business using a Web browser.
John Stevens is in charge of information security at Bank of Timbuktu. After one month in production, several customers have complained about the Internet enabled banking application. Strangely, the account balances of many of the bank's customers had been changed! However, money hasn't been removed from the bank; instead, money was transferred between accounts. Given this attack profile, John Stevens reviewed the Web application's logs and found the following entries:
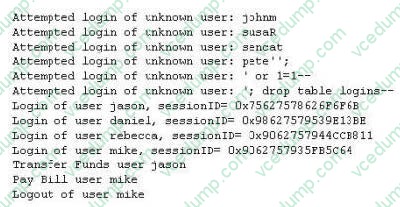
What kind of attack did the Hacker attempt to carry out at the bank?
A. Brute force attack in which the Hacker attempted guessing login ID and password from password cracking tools.
B. The Hacker attempted Session hijacking, in which the Hacker opened an account with the bank, then logged in to receive a session ID, guessed the next ID and took over Jason's session.
C. The Hacker used a generator module to pass results to the Web server and exploited Web application CGI vulnerability.
D. The Hacker first attempted logins with suspected user names, then used SQL Injection to gain access to valid bank login IDs. -
Question 400:
You generate MD5 128-bit hash on all files and folders on your computer to keep a baseline check for security reasons?
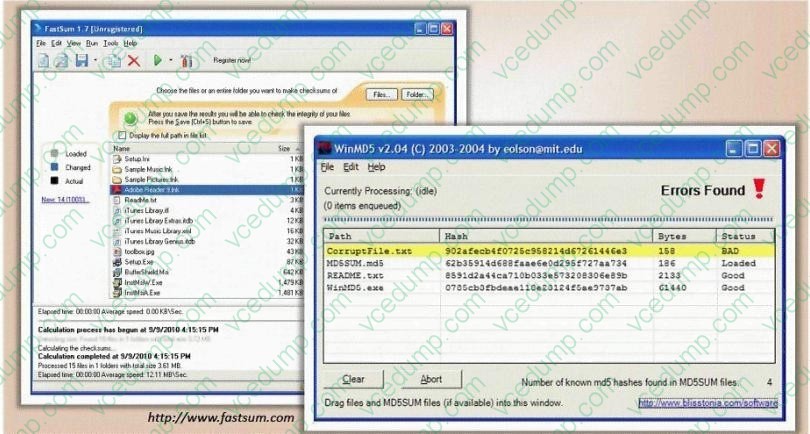
What is the length of the MD5 hash?
A. 32 character
B. 64 byte
C. 48 char
D. 128 kb
Related Exams:
-
112-51
EC-Council Certified Network Defense Essentials (NDE) -
212-055
Sun Certified Programmer for the Java 2 Platform.SE 5.0 -
212-77
EC-Council Certified Linux Security -
212-81
EC-Council Certified Encryption Specialist (ECES) -
212-82
EC-Council Certified Cybersecurity Technician (C|CT) -
212-89
EC Council Certified Incident Handler (ECIH v3) -
312-38
EC-Council Certified Network Defender (CND) -
312-39
EC-Council Certified SOC Analyst (CSA) -
312-40
EC-Council Certified Cloud Security Engineer (CCSE) -
312-49
ECCouncil Computer Hacking Forensic Investigator (V9)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 312-50V7 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.