312-50V7 Exam Details
-
Exam Code
:312-50V7 -
Exam Name
:Ethical Hacking and Countermeasures (CEHv7) -
Certification
:EC-COUNCIL Certifications -
Vendor
:EC-COUNCIL -
Total Questions
:514 Q&As -
Last Updated
:May 31, 2026
EC-COUNCIL 312-50V7 Online Questions & Answers
-
Question 411:
What is the main disadvantage of the scripting languages as opposed to compiled programming languages?
A. Scripting languages are hard to learn.
B. Scripting languages are not object-oriented.
C. Scripting languages cannot be used to create graphical user interfaces.
D. Scripting languages are slower because they require an interpreter to run the code. -
Question 412:
An IT security engineer notices that the company's web server is currently being hacked. What should the engineer do next?
A. Unplug the network connection on the company's web server.
B. Determine the origin of the attack and launch a counterattack.
C. Record as much information as possible from the attack.
D. Perform a system restart on the company's web server. -
Question 413:
Oregon Corp is fighting a litigation suit with Scamster Inc. Oregon has assigned a private investigative agency to go through garbage, recycled paper, and other rubbish at Scamster's office site in order to find relevant information. What would you call this kind of activity?
A. CI Gathering
B. Scanning
C. Dumpster Diving
D. Garbage Scooping -
Question 414:
The use of alert thresholding in an IDS can reduce the volume of repeated alerts, but introduces which of the following vulnerabilities?
A. An attacker, working slowly enough, can evade detection by the IDS.
B. Network packets are dropped if the volume exceeds the threshold.
C. Thresholding interferes with the IDS' ability to reassemble fragmented packets.
D. The IDS will not distinguish among packets originating from different sources. -
Question 415:
Which of the statements concerning proxy firewalls is correct?
A. Proxy firewalls increase the speed and functionality of a network.
B. Firewall proxy servers decentralize all activity for an application.
C. Proxy firewalls block network packets from passing to and from a protected network.
D. Computers establish a connection with a proxy firewall which initiates a new network connection for the client. -
Question 416:
In order to show improvement of security over time, what must be developed?
A. Reports
B. Testing tools
C. Metrics
D. Taxonomy of vulnerabilities -
Question 417:
The use of technologies like IPSec can help guarantee the followinG. authenticity, integrity, confidentiality and
A. non-repudiation.
B. operability.
C. security.
D. usability. -
Question 418:
John is the network administrator of XSECURITY systems. His network was recently compromised. He analyzes the log files to investigate the attack. Take a look at the following Linux log file snippet. The hacker compromised and "owned" a Linux machine. What is the hacker trying to accomplish here?
A. The hacker is attempting to compromise more machines on the network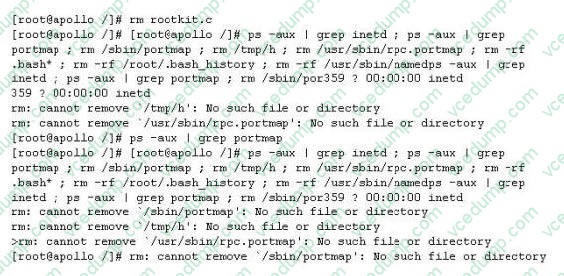
B. The hacker is planting a rootkit
C. The hacker is running a buffer overflow exploit to lock down the system
D. The hacker is trying to cover his tracks -
Question 419:
Which results will be returned with the following Google search query? site:target.com -site:Marketing.target.com accounting
A. Results matching all words in the query
B. Results matching "accounting" in domain target.com but not on the site Marketing.target.com
C. Results from matches on the site marketing.target.com that are in the domain target.com but do not include the word accounting
D. Results for matches on target.com and Marketing.target.com that include the word "accounting" -
Question 420:
Google uses a unique cookie for each browser used by an individual user on a computer. This cookie contains information that allows Google to identify records about that user on its database. This cookie is submitted every time a user launches a Google search, visits a site using AdSense etc. The information stored in Google's database, identified by the cookie, includes How would you prevent Google from storing your search keywords?
A. Block Google Cookie by applying Privacy and Security settings in your web browser
B. Disable the Google cookie using Google Advanced Search settings on Google Search page
C. Do not use Google but use another search engine Bing which will not collect and store your search keywords
D. Use MAC OS X instead of Windows 7. Mac OS has higher level of privacy controls by default.
Related Exams:
-
112-51
EC-Council Certified Network Defense Essentials (NDE) -
212-055
Sun Certified Programmer for the Java 2 Platform.SE 5.0 -
212-77
EC-Council Certified Linux Security -
212-81
EC-Council Certified Encryption Specialist (ECES) -
212-82
EC-Council Certified Cybersecurity Technician (C|CT) -
212-89
EC Council Certified Incident Handler (ECIH v3) -
312-38
EC-Council Certified Network Defender (CND) -
312-39
EC-Council Certified SOC Analyst (CSA) -
312-40
EC-Council Certified Cloud Security Engineer (CCSE) -
312-49
ECCouncil Computer Hacking Forensic Investigator (V9)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 312-50V7 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.