200-201 Exam Details
-
Exam Code
:200-201 -
Exam Name
:Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) -
Certification
:CyberOps Associate -
Vendor
:Cisco -
Total Questions
:543 Q&As -
Last Updated
:Jun 01, 2026
Cisco 200-201 Online Questions & Answers
-
Question 311:
A company had a recent breach and lost confidential data to a competitor. An internal investigation found out that a new junior accounting specialist logged in to the accounting server with their user ID and stole confidential data. The junior accounting specialist denies the action and claims that the attempt was done by someone else. During court proceedings, the company presents logs and CCTV camera recordings that show the malicious insider in action.
Which type of evidence has the company presented?
A. indirect and corroborative
B. direct and corroborative
C. circumstantial and direct
D. corroborative and substantive -
Question 312:
An information security analyst inspects the .pcap file and observes encrypted unusual SSH traffic flow over nonstandard ports.
Which technology makes this behavior feasible?
A. NAT
B. tunneling
C. P2P
D. TOR -
Question 313:
Which classification of cross-site scripting attack executes the payload without storing it for repeated use?
A. CSRF
B. reflective
C. DOM
D. stored -
Question 314:
Refer to the exhibit.
What is occurring?
A. possible DNS amplification attack with requests that maximize data quantity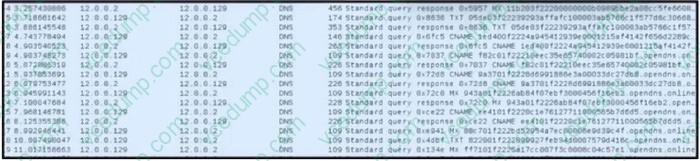
B. possible DNS tunneling with encrypted communication through CNAMEs
C. possible DNS cache poisoning with misdirects toward a fraudulent website
D. possible botnet traffic with random MX querying to generate increased traffic -
Question 315:
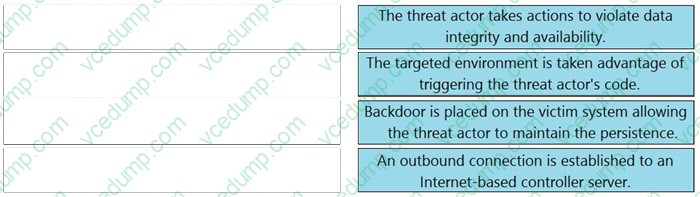
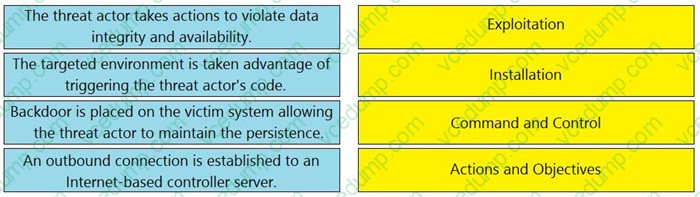
DRAG DROP
Drag and drop the definition from the left onto the phase on the right to classify intrusion events according to the Cyber Kill Chain model.
Select and Place:
-
Question 316:
Refer to the exhibit.
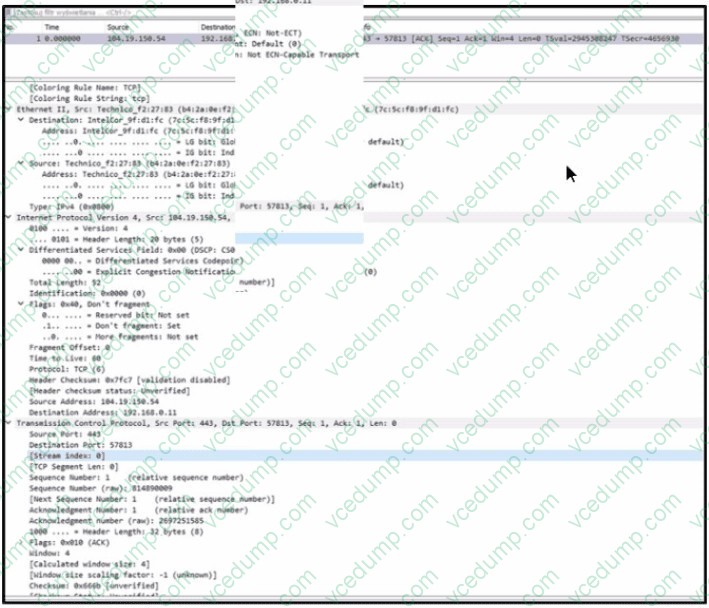
An engineer must use a 5-tuple approach to isolate a compromised host in a grouped set of logs.
Which data must the engineer use?
A. 66
B. b4:2a0ef227 83
C. 7c:5c:f8:9f:d1:fc
D. 57813 -
Question 317:
What ate two categories of DDoS attacks? (Choose two.)
A. split brain
B. scanning
C. phishing
D. reflected
E. direct -
Question 318:
How can TOR impact data visibility inside an organization?
A. no impact
B. increases security
C. increases data integrity
D. decreases visibility -
Question 319:
Which utility blocks a host portscan?
A. HIDS
B. sandboxing
C. host-based firewall
D. antimalware -
Question 320:
What are two social engineering techniques? (Choose two.)
A. privilege escalation
B. DDoS attack
C. phishing
D. man-in-the-middle
E. pharming
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Cisco exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 200-201 exam preparations and Cisco certification application, do not hesitate to visit our Vcedump.com to find your solutions here.