SY0-601 Exam Details
-
Exam Code
:SY0-601 -
Exam Name
:CompTIA Security+ -
Certification
:CompTIA Certifications -
Vendor
:CompTIA -
Total Questions
:1334 Q&As -
Last Updated
:May 26, 2026
CompTIA SY0-601 Online Questions & Answers
-
Question 751:
A network administrator has been asked to design a solution to improve a company's security posture The administrator is given the following, requirements?
1.
The solution must be inline in the network
2.
The solution must be able to block known malicious traffic
3.
The solution must be able to stop network-based attacks
Which of the following should the network administrator implement to BEST meet these requirements?
A. HIDS
B. NIDS
C. HIPS
D. NIPS -
Question 752:
A security analyst notices an unusual amount of traffic hitting the edge of the network. Upon examining the logs, the analyst identifies a source IP address and blocks that address from communicating with the network. Even though the analyst is blocking this address, the attack is still ongoing and coming from a large number of different source IP addresses. Which of the following describes this type of attack?
A. DDoS
B. Privilege escalation
C. DNS poisoning
D. Buffer overflow -
Question 753:
A spoofed identity was detected for a digital certificate. Which of the following are the type of unidentified key and the certificate that could be in use on the company domain?
A. Private key and root certificate
B. Public key and expired certificate
C. Private key and self-signed certificate
D. Public key and wildcard certificate -
Question 754:
Which of the following allow access to remote computing resources, a operating system and centrdized configuration and data?
A. Containers
B. Edge computing
C. Thin client
D. Infrastructure as a service -
Question 755:
A security administrator is trying to determine whether a server is vulnerable to a range of attacks. After using a tool, the administrator obtains the following output:
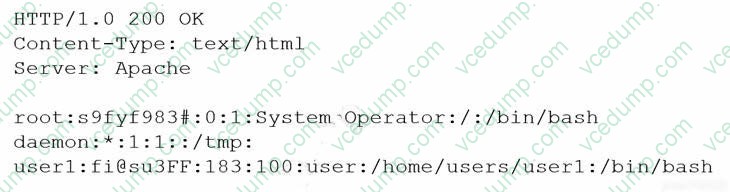
Which of the following attacks was successfully implemented based on the output?
A. Memory leak
B. Race conditions
C. SQL injection
D. Directory traversal -
Question 756:
A security analyst is evaluating the risks of authorizing multiple security solutions to collect data from the company's cloud environment Which of the following is an immediate consequence of these integrations?
A. Non-compliance with data sovereignty rules
B. Loss of the vendor's interoperability support
C. Mandatory deployment of a SIEM solution
D. Increase in the attack surface -
Question 757:
An organization recently released a software assurance policy that requires developers to run code scans each night on the repository. After the first night, the security team alerted the developers that more than 2,000 findings were reported and need to be addressed. Which of the following is the MOST likely cause for the high number of findings?
A. The vulnerability scanner was not properly configured and generated a high number of false positives
B. Third-party libraries have been loaded into the repository and should be removed from the codebase.
C. The vulnerability scanner found several memory leaks during runtime, causing duplicate reports for the same issue.
D. The vulnerability scanner was not loaded with the correct benchmarks and needs to be updated. -
Question 758:
Which of the following represents a biometric FRR?
A. Authorized users being denied access
B. Users failing to enter the correct PIN
C. The denied and authorized numbers being equal
D. The number of unauthorized users being granted access -
Question 759:
While researching a data exfiltration event, the security team discovers that a large amount of data was transferred to a file storage site on the internet. Which of the following controls would work best to reduce the risk of further exfiltration using this method?
A. Data loss prevention
B. Blocking IP traffic at the firewall
C. Containerization
D. File integrity monitoring -
Question 760:
Which of the following would provide guidelines on how to label new network devices as part of the initial configuration?
A. IP schema
B. Application baseline configuration
C. Standard naming convention policy
D. Wireless LAN and network perimeter diagram
Related Exams:
-
220-1001
CompTIA A+ Certification: Core 1 -
220-1002
CompTIA A+ Certification: Core 2 -
220-1101
CompTIA A+ Certification: Core 1 -
220-1102
CompTIA A+ Certification: Core 2 -
220-1201
CompTIA A+ Certification: Core 1 -
220-1202
CompTIA A+ Core 2 (2026) -
220-902
CompTIA A+ Certification -
CAS-004
CompTIA Advanced Security Practitioner (CASP+) -
CAS-005
CompTIA SecurityX -
CLO-001
CompTIA Cloud Essentials+
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your SY0-601 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.