SY0-501 Exam Details
-
Exam Code
:SY0-501 -
Exam Name
:CompTIA Security+ -
Certification
:CompTIA Certifications -
Vendor
:CompTIA -
Total Questions
:1423 Q&As -
Last Updated
:Sep 04, 2023
CompTIA SY0-501 Online Questions & Answers
-
Question 621:
A product manager is concerned about continuing operations at a facility located in a region undergoing significant political unrest. After consulting with senior management, a decision is made to suspend operations at the facility until the situation stabilizes. Which of the following risk management strategies BEST describes management's response?
A. Deterrence
B. Mitigation
C. Avoidance
D. Acceptance -
Question 622:
Which of the following provides PFS?
A. AES
B. RC4
C. DHE
D. HMAC -
Question 623:
A system's administrator has finished configuring firewall ACL to allow access to a new web server.
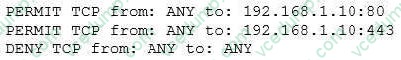
The security administrator confirms form the following packet capture that there is network traffic from the internet to the web server:
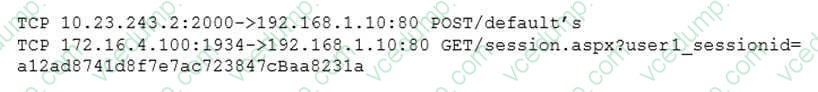
The company's internal auditor issues a security finding and requests that immediate action be taken. With which of the following is the auditor MOST concerned?
A. Misconfigured firewall
B. Clear text credentials
C. Implicit deny
D. Default configuration -
Question 624:
A network administrator needs to restrict the users of the company's WAPs to the sales department. The network administrator changes and hides the SSID and then discovers several employees had connected their personal devices to the wireless network. Which of the following would limit access to the wireless network to only organization-owned devices in the sales department?
A. Implementing MAC filtering
B. Reducing the signal strength to encompass only the sales department
C. Replacing the APs and sales department wireless cards to support 802.11b
D. Issuing a BYOD policy -
Question 625:
A company has just experienced a malware attack affecting a large number of desktop users. The antivirus solution was not able to block the malware, but the HIDS alerted to C2 calls as 'Troj.Generic'. Once the security team found a solution to remove the malware, they were able to remove the malware files successfully, and the HIDS stopped alerting. The next morning, however, the HIDS once again started alerting on the same desktops, and the security team discovered the files were back. Which of the following BEST describes the type of malware infecting this company's network?
A. Trojan
B. Spyware
C. Rootkit
D. Botnet -
Question 626:
Which of the following BEST explains "likelihood of occurrence"?
A. The chance that an event will happen regardless of how much damage it may cause
B. The overall impact to the organization once all factors have been considered
C. The potential for a system to have a weakness or flaw that might be exploited
D. The probability that a threat actor will target and attempt to exploit an organization's systems -
Question 627:
An incident involving a workstation that is potentially infected with a virus has occurred. The workstation may have sent confidential data to an unknown internet server. Which of the following should a security analyst do FIRST?
A. Make a copy of everything in memory on the workstation.
B. Turn off the workstation.
C. Consult information security policy.
D. Run a virus scan. -
Question 628:
During the penetration testing of an organization, the tester was provided with the names of a few key servers, along with their IP address. Which of the following is the organization conducting?
A. Gray box testing
B. White box testing
C. Back box testing
D. Isolated container testing
E. Vulnerability testing -
Question 629:
An office recently completed digitizing all its paper records. Joe, the data custodian, has been tasked with the disposal of the paper files, which include:
1.
Intellectual property
2.
Payroll records
3.
Financial information
4.
Drug screening results
Which of the following is the BEST way to dispose of these items?
A. Shredding
B. Pulping
C. Deidentifying
D. Recycling -
Question 630:
A penetration testing team deploys a specifically crafted payload to a web server, which results in opening a new session as the web server daemon. This session has full read/write access to the file system and the admin console. Which of the following BEST describes the attack?
A. Domain hijacking
B. Injection
C. Buffer overflow
D. Privilege escalation
Related Exams:
-
220-1001
CompTIA A+ Certification: Core 1 -
220-1002
CompTIA A+ Certification: Core 2 -
220-1101
CompTIA A+ Certification: Core 1 -
220-1102
CompTIA A+ Certification: Core 2 -
220-1201
CompTIA A+ Certification: Core 1 -
220-1202
CompTIA A+ Core 2 (2026) -
220-902
CompTIA A+ Certification -
CAS-004
CompTIA Advanced Security Practitioner (CASP+) -
CAS-005
CompTIA SecurityX -
CLO-001
CompTIA Cloud Essentials+
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your SY0-501 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.