SY0-501 Exam Details
-
Exam Code
:SY0-501 -
Exam Name
:CompTIA Security+ -
Certification
:CompTIA Certifications -
Vendor
:CompTIA -
Total Questions
:1423 Q&As -
Last Updated
:Sep 04, 2023
CompTIA SY0-501 Online Questions & Answers
-
Question 351:
An organization wants to deliver streaming audio and video from its home office to remote locations all over the world. It wants the stream to be delivered securely and protected from intercept and replay attacks. Which of the following protocols is BEST suited for this purpose?
A. SSH
B. SIP
C. S/MIME
D. SRTP -
Question 352:
An analyst is reviewing a simple program for potential security vulnerabilities before being deployed to a Windows server. Given the following code:
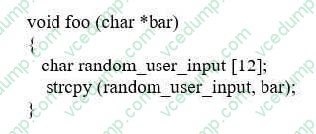
Which of the following vulnerabilities is present?
A. Bad memory pointer
B. Buffer overflow
C. Integer overflow
D. Backdoor -
Question 353:
An administrator has concerns regarding the traveling sales team who works primarily from smart phones. Given the sensitive nature of their work, which of the following would BEST prevent access to the data in case of loss or theft?
A. Enable screensaver locks when the phones are not in use to prevent unauthorized access
B. Configure the smart phones so that the stored data can be destroyed from a centralized location
C. Configure the smart phones so that all data is saved to removable media and kept separate from the device
D. Enable GPS tracking on all smart phones so that they can be quickly located and recovered -
Question 354:
Legal authorities notify a company that its network has been compromised for the second time in two years. The investigation shows the attackers were able to use the same vulnerability on different systems in both attacks. Which of the following would have allowed the security team to use historical information to protect against the second attack?
A. Key risk indicators
B. Lessons learned
C. Recovery point objectives
D. Tabletop exercise -
Question 355:
A user suspects someone has been accessing a home network without permission by spoofing the MAC address of an authorized system. While attempting to determine if an authorized user is logged
into the home network, the user reviews the wireless router, which shows the following table for systems that are currently on the home network.
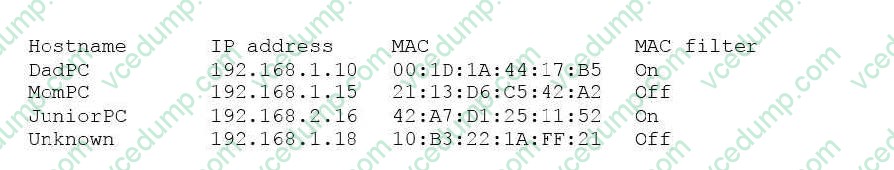
Which of the following should be the NEXT step to determine if there is an unauthorized user on the network?
A. Apply MAC filtering and see if the router drops any of the systems.
B. Physically check each of the authorized systems to determine if they are logged onto the network.
C. Deny the "unknown" host because the hostname is not known and MAC filtering is not applied to this host.
D. Conduct a ping sweep of each of the authorized systems and see if an echo response is received. -
Question 356:
Six months into development, the core team assigned to implement a new internal piece of software must convene to discuss a new requirement with the stake holders. A stakeholder identified a missing feature critical to the organization, which must be implemented. The team needs to validate the feasibility of the newly introduced requirement and ensure it does not introduce new vulnerabilities to the software and other applications that will integrate with it. Which of the following BEST describes what the company?
A. The system integration phase of the SDLC
B. The system analysis phase of SSDSLC
C. The system design phase of the SDLC
D. The system development phase of the SDLC -
Question 357:
A help desk technician is trying to determine the reason why several high-level officials' account passwords need to be reset shortly after implementing a self-service password reset process. Which of the following would BEST explain the issue?
A. The system asked for publicly available information
B. The self-service system was compromised
C. The account passwords expired
D. A spear phishing attack occurred -
Question 358:
A company is deploying a file-sharing protocol access a network and needs to select a protocol for authenticating clients. Management requests that the service be configured in the most secure way possible. The protocol must also be capable of mutual authentication, and support SSO and smart card logons. Which of the following would BEST accomplish this task?
A. Store credentials in LDAP
B. Use NTLM authentication
C. Implement Kerberos
D. Use MSCHAP authentication -
Question 359:
Which of the following implements two-factor authentication on a VPN?
A. Username, password, and source IP
B. Public and private keys
C. HOTP token and logon credentials
D. Source and destination IP addresses -
Question 360:
A security analyst is hardening a large-scale wireless network. The primary requirements are the following: Must use authentication through EAP-TLS certificates Must use an AAA server Must use the most secure encryption protocol Given these requirements, which of the following should the analyst implement and recommend? (Select TWO.)
A. 802.1X
B. 802.3
C. LDAP
D. TKIP
E. CCMP
F. WPA2-PSK
Related Exams:
-
220-1001
CompTIA A+ Certification: Core 1 -
220-1002
CompTIA A+ Certification: Core 2 -
220-1101
CompTIA A+ Certification: Core 1 -
220-1102
CompTIA A+ Certification: Core 2 -
220-1201
CompTIA A+ Certification: Core 1 -
220-1202
CompTIA A+ Core 2 (2026) -
220-902
CompTIA A+ Certification -
CAS-004
CompTIA Advanced Security Practitioner (CASP+) -
CAS-005
CompTIA SecurityX -
CLO-001
CompTIA Cloud Essentials+
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your SY0-501 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.