SY0-501 Exam Details
-
Exam Code
:SY0-501 -
Exam Name
:CompTIA Security+ -
Certification
:CompTIA Certifications -
Vendor
:CompTIA -
Total Questions
:1423 Q&As -
Last Updated
:Sep 04, 2023
CompTIA SY0-501 Online Questions & Answers
-
Question 1351:
Which of the following is the purpose of an industry-standard framework?
A. To promulgate compliance requirements for sales of common IT systems
B. To provide legal relief to participating organizations in the event of a security breach
C. To promulgate security settings on a vendor-by-vendor basis
D. To provide guidance across common system implementations -
Question 1352:
A system administrator is configuring a site-to-site VPN tunnel. Which of the following should be configured on the VPN concentrator during the IKE phase?
A. RIPEMD
B. ECDHE
C. Diffie-Hellman
D. HTTPS -
Question 1353:
Upon entering an incorrect password, the logon screen displays a message informing the user that the password does not match the username provided and is not the required length of 12 characters. Which of the following secure coding techniques should a security analyst address with the application developers to follow security best practices?
A. Input validation
B. Error handling
C. Obfuscation
D. Data exposure -
Question 1354:
An employer requires that employees use a key-generating app on their smartphones to log into corporate applications. In terms of authentication of an individual, this type of access policy is BEST defined as:
A. Something you have.
B. Something you know.
C. Something you do.
D. Something you are. -
Question 1355:
When choosing a hashing algorithm for storing passwords in a web server database, which of the following is the BEST explanation for choosing HMAC-MD5 over simple MD5?
A. HMAC provides hardware acceleration thus speeding up authentication
B. HMAC adds a transport layer handshake which improves authentication
C. HMAC-MD5 can be decrypted taster speeding up performance
D. HMAC-M05 is more resistant to brute forcing -
Question 1356:
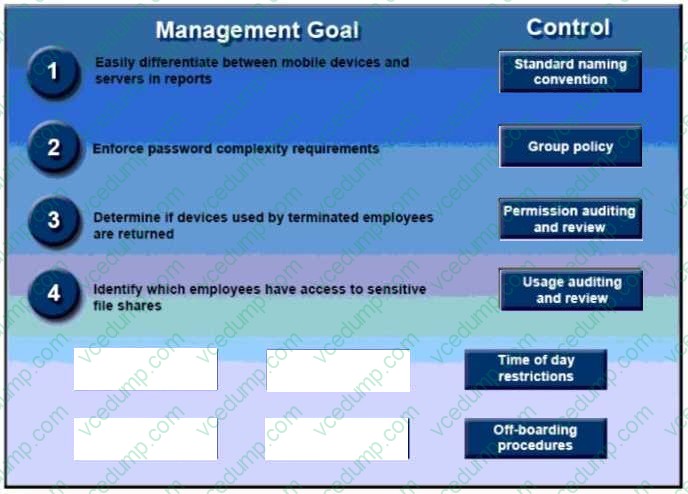
DRAG DROP
A security administrator has been tasked with implementing controls that meet management goals. Drag and drop the appropriate control used to accomplish the account management goal. Options may be used once or not at all.
Select and Place:

-
Question 1357:
Given the following output:
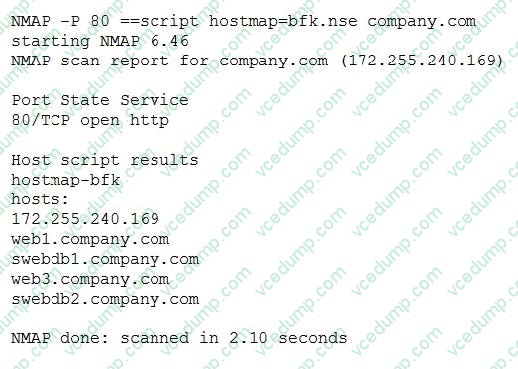
Which of the following BEST describes the scanned environment?
A. A host was identified as a web server that is hosting multiple domains
B. A host was scanned, and web-based vulnerabilities were found
C. A connection was established to a domain, and several redirect connections were identified
D. A web shell was planted in company.com's content management system -
Question 1358:
A vulnerability scanner that uses its running service's access level to better assess vulnerabilities across multiple assets within an organization is performing a:
A. Credentialed scan.
B. Non-intrusive scan.
C. Privilege escalation test.
D. Passive scan. -
Question 1359:
A highly complex password policy has made it nearly impossible to crack account passwords. Which of the following might a hacker still be able to perform?
A. Pass-the-hash attack
B. ARP poisoning attack
C. Birthday attack
D. Brute force attack -
Question 1360:
Which of the following BEST describes an important security advantage yielded by implementing vendor diversity?
A. Sustainability
B. Homogeneity
C. Resiliency
D. Configurability
Related Exams:
-
220-1001
CompTIA A+ Certification: Core 1 -
220-1002
CompTIA A+ Certification: Core 2 -
220-1101
CompTIA A+ Certification: Core 1 -
220-1102
CompTIA A+ Certification: Core 2 -
220-1201
CompTIA A+ Certification: Core 1 -
220-1202
CompTIA A+ Core 2 (2026) -
220-902
CompTIA A+ Certification -
CAS-004
CompTIA Advanced Security Practitioner (CASP+) -
CAS-005
CompTIA SecurityX -
CLO-001
CompTIA Cloud Essentials+
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your SY0-501 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.