Exam Details
Exam Code
:PCNSCExam Name
:Palo Alto Networks Certified Network Security Consultant (PCNSC)Certification
:Palo Alto Networks CertificationsVendor
:Palo Alto NetworksTotal Questions
:141 Q&AsLast Updated
:Aug 13, 2025
Palo Alto Networks Palo Alto Networks Certifications PCNSC Questions & Answers
-
Question 31:
What is exchanged through the HA2 link?
A. hello heartbeats
B. User-ID in information
C. session synchronization
D. HA state information
-
Question 32:
Which Captive Portal mode must be contoured to support MFA authentication?
A. Single Sign-On
B. Redirect
C. Transparent
D. NTLM
-
Question 33:
How does Panorama prompt VMware NSX to quarantine an in6erface VM??
A. Syslog Server Profile
B. Email Server Profile
C. SNMP Server Profile
D. HTTP Server Profile
-
Question 34:
An administrator needs to optimize traffic to prefer business-critical applications over non-critical applications.
QoS natively integrates with which feature to provide service quality?
A. port inspection
B. certification revocation
C. Content-ID
D. App-ID
-
Question 35:
A Palo Alto Networks NGFW just submitted a file lo WildFire tor analysis Assume a 5-minute window for analysis. The firewall is configured to check for verdicts every 5 minutes.
How quickly will the firewall receive back a verdict?
A. 10 to 15 minutes
B. 5 to 10 minutes
C. More than 15 minutes
D. 5 minutes
-
Question 36:
Which administrative authentication method supports authorization by an external service?
A. RADIUS
B. SSH keys
C. Certification
D. LDAP
-
Question 37:
What should an administrator consider when planning to revert Panorama to a pre-PAN-OS 8.1 version?
A. When Panorama is reverted to an earlier PAN-OS release, variable used in template stacks will be removed authentically.
B. Panorama cannot be reverted to an earlier PAN-OS release if variables are used in templates or stacks.
C. An administrator must use the Expedition tool to adapt the configuration to the pre-pan-OS 8.1 state.
D. Administrators need to manually update variable characters to those to used in pre-PAN-OS 8.1.
-
Question 38:
When a malware-infected host attempts to resolve a known command-and-control server, the traffic matches a security policy with DNS sinhole enabled, generating a traffic log. What will be the destination IP Address in that log entry?
A. The IP Address of sinkhole.paloaltonetworks.com
B. The IP Address of the command-and-control server
C. The IP Address specified in the sinkhole configuration
D. The IP Address of one of the external DNS servers identified in the anti-spyware database
-
Question 39:
An administrator wants multiple web servers in the DMZ to receive connections from the internet. Traffic destined for 206.15.22.9 port 80/TCP needs to be forwarded to the server at 10 1.22 Based on the information shown in the age, which NAT rule will forward web-browsing traffic correctly?
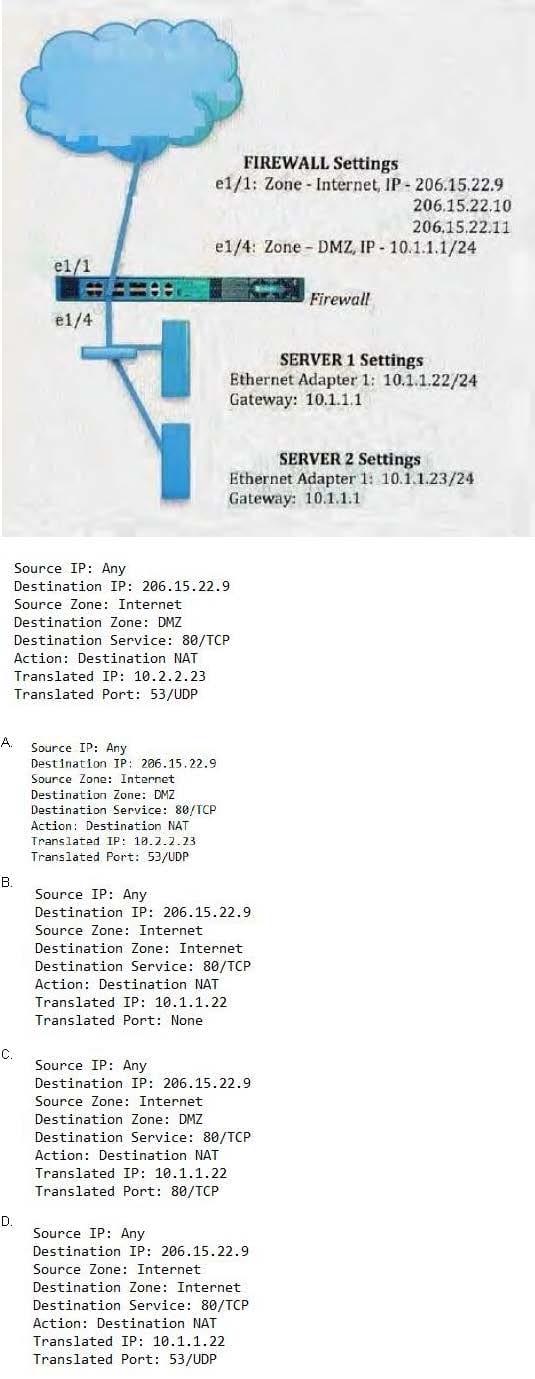
A. B. C. D.
-
Question 40:
A Security policy rule is configured with a Vulnerability Protection Profile and an action of Deny".
Which action will this configuration cause on the matched traffic?
A. The configuration is invalid it will cause the firewall to Skip this Security policy rule A warning will be displayed during a command.
B. The configuration is valid It will cause the firewall to deny the matched sessions. Any configured Security Profiles have no effect if the Security policy rule action is set to "Deny".
C. The configuration will allow the matched session unless a vulnerability signature is detected. The "Deny" action will supersede the per. defined, severity defined actions defined in the associated Vulnerability Protection Profile.
D. The configuration is invalid. The Profile Settings section will be- grayed out when the action is set to "Deny".
Related Exams:
PAN-NGFE
Palo Alto Networks Network Next-Generation Firewall EngineerPAN-NSG
Palo Alto Networks Network Security GeneralistPAN-NSP
Palo Alto Networks Network Security ProfessionalPAN-SSEE
Palo Alto Networks Security Service Edge EngineerPAN-XDRE
Palo Alto Networks XDR EngineerPCCET
Palo Alto Networks Certified Cybersecurity Entry-level Technician (PCCET)PCCSA
Palo Alto Networks Certified Cybersecurity Associate (PCCSA)PCCSE
Prisma Certified Cloud Security Engineer (PCCSE)PCDRA
Palo Alto Networks Certified Detection and Remediation Analyst (PCDRA)PCNSA
Palo Alto Networks Certified Network Security Administrator (PCNSA)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Palo Alto Networks exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your PCNSC exam preparations and Palo Alto Networks certification application, do not hesitate to visit our Vcedump.com to find your solutions here.