Exam Details
Exam Code
:PCNSCExam Name
:Palo Alto Networks Certified Network Security Consultant (PCNSC)Certification
:Palo Alto Networks CertificationsVendor
:Palo Alto NetworksTotal Questions
:141 Q&AsLast Updated
:Aug 13, 2025
Palo Alto Networks Palo Alto Networks Certifications PCNSC Questions & Answers
-
Question 21:
During the packet flow process, which two processes are performed in application identification? (Choose two.)
A. Application changed from content inspection
B. session application identified
C. pattern based application identification
D. application override policy match
-
Question 22:
Which prerequisite must be satisfied before creating an SSH proxy Decryption policy?
A. No prerequisites are required
B. SSH keys must be manually generated
C. Both SSH keys and SSL certificates must be generated
D. SSL certificates must be generated
-
Question 23:
What are two benefits of nested device groups in panorama? (Choose two )
A. overwrites local firewall configuration
B. requires configuration both function and location for every device
C. all device groups inherit setting from the Shared group
D. reuse of the existing Security policy rules and objects
-
Question 24:
VPN traffic intended for an administrator's Palo Alto Networks NGfW is being maliciously intercepted and retransmitted by the interceptor. When Creating a VPN tunnel, which protection profile cm be enabled to prevent this malicious behavior?
A. zone Protection
B. Web Application
C. DoS Protection
D. Replay
-
Question 25:
What will be the egress interface if the traffic's ingress interface is Ethernet 1/6 sourcing form 192.168.11.3 and to the destination 10.46.41.113.during the.
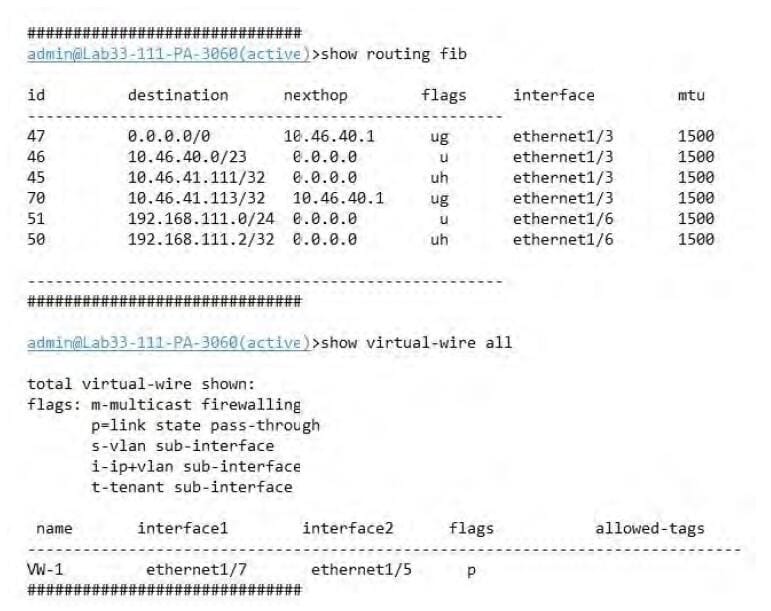
A. ethernet 1/6
B. ethernet 1/5
C. ethernet 1/3
D. ethernet 1/7
-
Question 26:
Which option would an administration choose to define the certificate and protect that Panorama and its managed devices uses for SSL/ITS services?
A. Set Up SSL/TLS under Policies > Service/URL Category > Service.
B. Configure on SSL/TLS Profile.
C. Configure a Decryption Profile and select SSL/TLS services.
D. Set up Security policy rule to allow SSL communication.
-
Question 27:
A user's traffic traversing a Palo Alto Networks NGFW sometime can reach http//www company com At the session times out. The NGFW has been configured with a PBF rule that the user's traffic matches when it goes to http //www company com.
How con the firewall be configured to automatically disable the PBF rule if the next hop goes down?
A. Configure path monitoring for tine next hop gateway on the default route in tin- virtual router.
B. Enable and configure a Link Monitoring Profile for the external interface of the firewall.
C. Create and add a Monitor Profile with an action of Wait Recover in the PBF rule in question.
D. Create and add a Monitor Profile with an action of Fail Over in the PBF rule in question.
-
Question 28:
A Company needs to preconfigured firewalls to be sent to remote sites with the least amount of preconfiguration. Once deployed, each firewall must establish secure tunnels back to multiple regional data centers to include the future regional data centers.
Which VPN configuration would adapt to changes when deployed to Hie future site?
A. preconfigured GlobalProtcet satellite
B. preconfigured GlobalProtcet client
C. preconfigured iPsec tunnels
D. preconfigured PPTP Tunnels
-
Question 29:
Which feature can be configured on VM-Series firewalls'?
A. aggregate interlaces
B. multiple virtual systems
C. Globallprotect
D. machine learning
-
Question 30:
When is the content inspection performed in the packet flow process?
A. after the SSL Proxy re-encrypts the packet
B. before the packet forwarding process
C. after the application has been identified
D. before session lookup
Related Exams:
PAN-NGFE
Palo Alto Networks Network Next-Generation Firewall EngineerPAN-NSG
Palo Alto Networks Network Security GeneralistPAN-NSP
Palo Alto Networks Network Security ProfessionalPAN-SSEE
Palo Alto Networks Security Service Edge EngineerPAN-XDRE
Palo Alto Networks XDR EngineerPCCET
Palo Alto Networks Certified Cybersecurity Entry-level Technician (PCCET)PCCSA
Palo Alto Networks Certified Cybersecurity Associate (PCCSA)PCCSE
Prisma Certified Cloud Security Engineer (PCCSE)PCDRA
Palo Alto Networks Certified Detection and Remediation Analyst (PCDRA)PCNSA
Palo Alto Networks Certified Network Security Administrator (PCNSA)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Palo Alto Networks exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your PCNSC exam preparations and Palo Alto Networks certification application, do not hesitate to visit our Vcedump.com to find your solutions here.