CEH-001 Exam Details
-
Exam Code
:CEH-001 -
Exam Name
:Certified Ethical Hacker (CEH) -
Certification
:GAQM Certifications -
Vendor
:GAQM -
Total Questions
:878 Q&As -
Last Updated
:May 30, 2026
GAQM CEH-001 Online Questions & Answers
-
Question 361:
A security policy will be more accepted by employees if it is consistent and has the support of
A. coworkers.
B. executive management.
C. the security officer.
D. a supervisor. -
Question 362:
What is a Trojan Horse?
A. A malicious program that captures your username and password
B. Malicious code masquerading as or replacing legitimate code
C. An unauthorized user who gains access to your user database and adds themselves as a user
D. A server that is to be sacrificed to all hacking attempts in order to log and monitor the hacking activity -
Question 363:
Which of the following does proper basic configuration of snort as a network intrusion detection system require?
A. Limit the packets captured to the snort configuration file.
B. Capture every packet on the network segment.
C. Limit the packets captured to a single segment.
D. Limit the packets captured to the /var/log/snort directory. -
Question 364:
Which of the following identifies the three modes in which Snort can be configured to run?
A. Sniffer, Packet Logger, and Network Intrusion Detection System
B. Sniffer, Network Intrusion Detection System, and Host Intrusion Detection System
C. Sniffer, Host Intrusion Prevention System, and Network Intrusion Prevention System
D. Sniffer, Packet Logger, and Host Intrusion Prevention System -
Question 365:
Here is the ASCII Sheet.
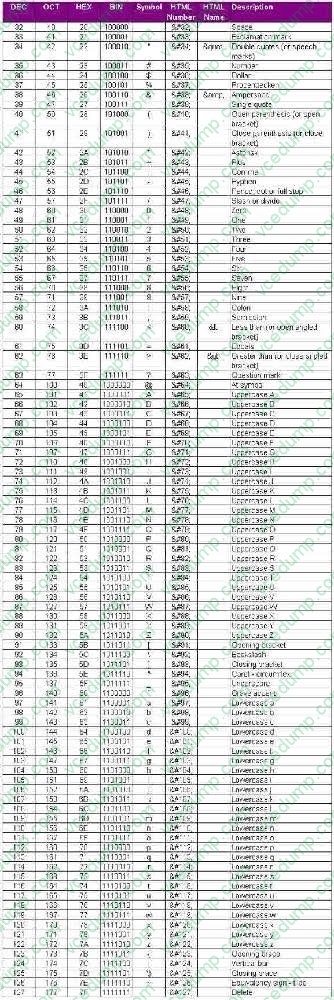
You want to guess the DBO username juggyboy (8 characters) using Blind SQL Injection technique. What is the correct syntax?
A. Option A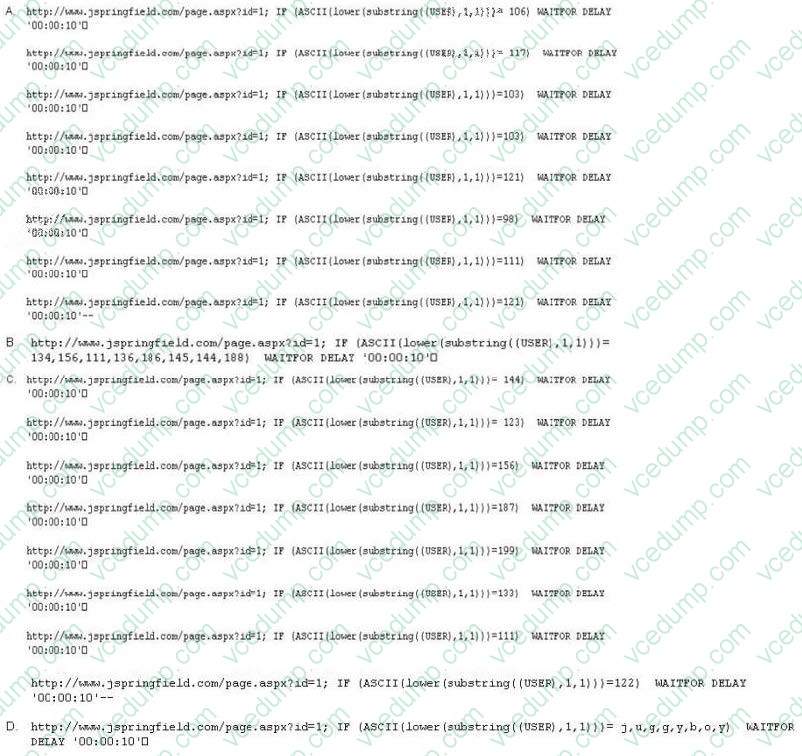
B. Option B
C. Option C
D. Option D -
Question 366:
Which of the following are well know password-cracking programs?(Choose all that apply.
A. L0phtcrack
B. NetCat
C. Jack the Ripper
D. Netbus
E. John the Ripper -
Question 367:
If you come across a sheepdip machaine at your client site, what would you infer?
A. A sheepdip computer is used only for virus checking.
B. A sheepdip computer is another name for honeypop.
C. A sheepdip coordinates several honeypots.
D. A sheepdip computer defers a denial of service attack. -
Question 368:
Which system consists of a publicly available set of databases that contain domain name registration contact information?
A. WHOIS
B. IANA
C. CAPTCHA
D. IETF -
Question 369:
Null sessions are un-authenticated connections (not using a username or password.) to an NT or 2000 system. Which TCP and UDP ports must you filter to check null sessions on your network?
A. 137 and 139
B. 137 and 443
C. 139 and 443
D. 139 and 445 -
Question 370:
StackGuard (as used by Immunix), ssp/ProPolice (as used by OpenBSD), and Microsoft's /GS option use _____ defense against buffer overflow attacks.
A. Canary
B. Hex editing
C. Format checking
D. Non-executing stack
Related Exams:
-
APM-001
Certified Associate in Project Management (APM) -
BMP-001
Certified Business Management Professional (BMP) -
BPM-001
Certified Business Process Manager (BPM) -
CAMT-001
IMTQN Certified Advanced Mobile Tester (CAMT) -
CBAF-001
Certified Business Analyst - Foundation -
CBCP-002
Certified Business Continuity Professional (CBCP) -
CCCP-001
Certified Cloud Computing Professional (CCCP) -
CDCP-001
Certified Data Centre Professional (CDCP) -
CEH-001
Certified Ethical Hacker (CEH) -
CFA-001
Certified Forensic Analyst (CFA)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only GAQM exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CEH-001 exam preparations and GAQM certification application, do not hesitate to visit our Vcedump.com to find your solutions here.