SK0-005 Exam Details
-
Exam Code
:SK0-005 -
Exam Name
:CompTIA Server+ -
Certification
:CompTIA Certifications -
Vendor
:CompTIA -
Total Questions
:550 Q&As -
Last Updated
:May 26, 2026
CompTIA SK0-005 Online Questions & Answers
-
Question 361:
Following a recent power outage, a server in the data center has been constantly going offline and losing its configuration. Users have been experiencing access issues while using the application on the server. The server technician notices the date and time are incorrect when the server is online. All other servers are working. Which of the following would MOST likely cause this issue? (Choose two.)
A. The server has a faulty power supply.
B. The server has a CMOS battery failure.
C. The server requires OS updates.
D. The server has a malfunctioning LED panel.
E. The servers have NTP configured.
F. CPU frequency scaling is set too high. -
Question 362:
A human resources analyst is attempting to email the records for new employees to an outside payroll company. Each time the analyst sends an email containing employee records, the email is rejected with an error message. Other emails outside the company are sent correctly. Which of the following is most likely generating the error?
A. DHCP configuration
B. Firewall rules
C. DLP software
D. Intrusion detection system -
Question 363:
A technician is decommissioning a server from a production environment. The technician removes the server from the rack but then decides to repurpose the system as a lab server instead of decommissioning it. Which of the following is the most appropriate NEXT step to recycle and reuse the system drives?
A. Reinstall the OS.
B. Wipe the drives.
C. Degauss the drives.
D. Update the IP schema. -
Question 364:
A newly hired systems administrator is concerned about fileshare access at the company. The administrator turns on DLP for the fileshare and lets it propagate for a week. Which of the following can the administrator perform now?
A. Manage the fileshare from an RDP session.
B. Audit the permissions of the fileshare.
C. Audit the access to the physical fileshare.
D. Manage the permissions from the fileshare. -
Question 365:
A snapshot is a feature that can be used in hypervisors to:
A. roll back firmware updates.
B. restore to a previous version.
C. roll back application drivers.
D. perform a backup restore. -
Question 366:
An administrator is tasked with building an environment consisting of four servers that can each serve the same website. Which of the following concepts is described?
A. Load balancing
B. Direct access
C. Overprovisioning
D. Network teaming -
Question 367:
A server administrator needs to create a new folder on a file server that only specific users can access. Which of the following BEST describes how the server administrator can accomplish this task?
A. Create a group that includes all users and assign it to an ACL.
B. Assign individual permissions on the folder to each user.
C. Create a group that includes all users and assign the proper permissions.
D. Assign ownership on the folder for each user. -
Question 368:
An administrator gave Ann modify permissions to a shared folder called DATA, which is located on the company server. Other users need read access to the files in this folder. The current configuration is as follows:
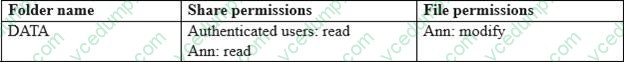
The administrator has determined Ann cannot write anything to the DATA folder using the network. Which of the following would be the best practice to set up Ann's permissions correctly, exposing only the minimum rights required?
A. Option A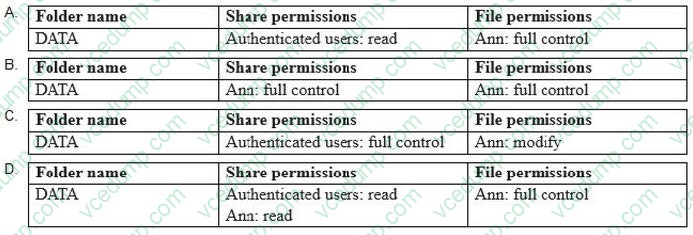
B. Option B
C. Option C
D. Option D -
Question 369:
An administrator is unable to get server updates from a WSUS server. However, the administrator was able to patch the server successfully last month.
Which of the following should the administrator check first?
A. The software firewall on the local server
B. Stopped services on the local server
C. The primary DNS IP address assigned to the server
D. The hosts file on the local server -
Question 370:
A technician has been asked to check on a SAN. Upon arrival, the technician notices the red LED indicator shows a disk has failed. Which of the following should the technician do NEXT, given the disk is hot swappable?
A. Stop sharing the volume
B. Replace the disk
C. Shut down the SAN
D. Stop all connections to the volume
Related Exams:
-
220-1001
CompTIA A+ Certification: Core 1 -
220-1002
CompTIA A+ Certification: Core 2 -
220-1101
CompTIA A+ Certification: Core 1 -
220-1102
CompTIA A+ Certification: Core 2 -
220-1201
CompTIA A+ Certification: Core 1 -
220-1202
CompTIA A+ Core 2 (2026) -
220-902
CompTIA A+ Certification -
CAS-004
CompTIA Advanced Security Practitioner (CASP+) -
CAS-005
CompTIA SecurityX -
CLO-001
CompTIA Cloud Essentials+
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your SK0-005 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.