NSE6_FNC-8.5 Exam Details
-
Exam Code
:NSE6_FNC-8.5 -
Exam Name
:Fortinet NSE 6 - FortiNAC 8.5 -
Certification
:Fortinet Certifications -
Vendor
:Fortinet -
Total Questions
:30 Q&As -
Last Updated
:Jan 13, 2026
Fortinet NSE6_FNC-8.5 Online Questions & Answers
-
Question 1:
What would occur if both an unknown (rogue) device and a known (trusted) device simultaneously appeared on a port that is a member of the Forced Registration port group?
A. The port would be provisioned to the registration network, and both hosts would be isolated.
B. The port would not be managed, and an event would be generated.
C. The port would be provisioned for the normal state host, and both hosts would have access to that VLAN.
D. The port would be administratively shut down. -
Question 2:
Where do you look to determine when and why the FortiNAC made an automated network access change?
A. The Admin Auditing view
B. The Event view
C. The Connections view
D. The Port Changes view -
Question 3:
In an isolation VLAN, which three services does FortiNAC supply? (Choose three.)
A. DNS
B. NTP
C. SMTP
D. DHCP
E. Web -
Question 4:
How are logical networks assigned to endpoints?
A. Through Layer 3 polling configurations
B. Through network access policies
C. Through FortiGate IPv4 policies
D. Through device profiling rules -
Question 5:
Where do you look to determine what network access policy, if any, is being applied to a particular host?
A. The network access policy configuration
B. The Port Properties view of the hosts port
C. The Policy Logs view
D. The Policy Details view for the host -
Question 6:
Refer to the exhibit.
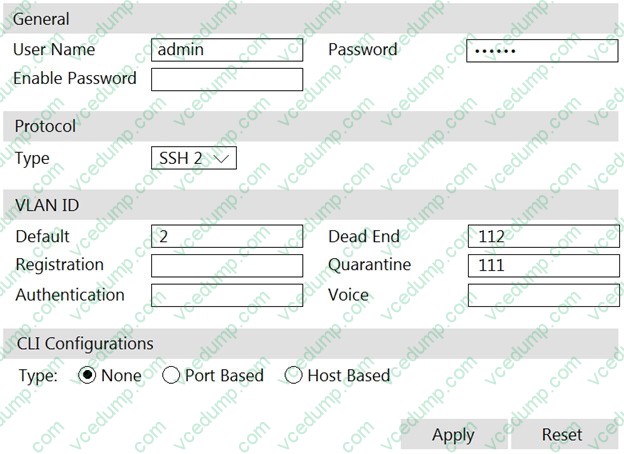
If you are forcing the registration of unknown (rogue) hosts, and an unknown (rogue) host connects to a port on the switch, what will occur?
A. No VLAN change is performed.
B. The host is disabled.
C. The host is moved to VLAN 111.
D. The host is moved to a default isolation VLAN. -
Question 7:
Which agent can receive and display messages from FortiNAC to the end user?
A. Persistent
B. Passive
C. MDM
D. Dissolvable -
Question 8:
What capability do logical networks provide?
A. VLAN-based inventory reporting
B. Interactive topology view diagrams
C. Application of different access values from a single access policy
D. Autopopulation of device groups based on point of connection -
Question 9:
Which three of the following are components of a security rule? (Choose three.)
A. Methods
B. User or host profile
C. Security String
D. Trigger
E. Action -
Question 10:
Which two methods can be used to gather a list of installed applications and application details from a host? (Choose two.)
A. Agent technology
B. MDM integration
C. Portal page on-boarding options
D. Application layer traffic inspection
Related Exams:
-
EMEA-ADVANCED-SUPPORT
Fortinet EMEA Advanced Support -
FCP_FAC_AD-6.5
FCP - FortiAuthenticator 6.5 Administrator -
FCP_FAZ_AD-7.4
FCP - FortiAnalyzer 7.4 Administrator -
FCP_FAZ_AN-7.4
FCP - FortiAnalyzer 7.4 Analyst -
FCP_FCT_AD-7.2
FCP - Forti Client EMS 7.2 Administrator -
FCP_FGT_AD-7.4
FCP - FortiGate 7.4 Administrator -
FCP_FGT_AD-7.6
FortiGate 7.6 Administrator FCP_FGT_AD-7.6 -
FCP_FMG_AD-7.4
FCP - FortiManager 7.4 Administrator -
FCP_FMG_AD-7.6
FortiManager 7.6 Administrator -
FCP_FML_AD-7.4
FCP - FortiMail 7.4 Administrator
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Fortinet exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your NSE6_FNC-8.5 exam preparations and Fortinet certification application, do not hesitate to visit our Vcedump.com to find your solutions here.