350-701 Exam Details
-
Exam Code
:350-701 -
Exam Name
:Implementing and Operating Cisco Security Core Technologies (SCOR) -
Certification
:CCIE Security -
Vendor
:Cisco -
Total Questions
:784 Q&As -
Last Updated
:May 30, 2026
Cisco 350-701 Online Questions & Answers
-
Question 591:
Which open source tool does Cisco use to create graphical visualizations of network telemetry on Cisco IOS XE devices?
A. InfluxDB
B. Splunk
C. SNMP
D. Grafana -
Question 592:
What is the purpose of a NetFlow version 9 template record?
A. It specifies the data format of NetFlow processes.
B. It provides a standardized set of information about an IP flow.
C. lt defines the format of data records.
D. It serves as a unique identification number to distinguish individual data records -
Question 593:
Which two activities are performed using Cisco DNA Center? (Choose two.)
A. accounting
B. design
C. provision
D. DNS
E. DHCP -
Question 594:
Which VPN provides scalability for organizations with many remote sites?
A. DMVPN
B. SSLVPN
C. GRE over IPsec
D. site-to-site IPsec -
Question 595:
What is a description of microsegmentation?
A. Environments apply a zero-trust model and specify how applications on different servers or containers can communicate
B. Environments deploy a container orchestration platform, such as Kubernetes, to manage the application delivery
C. Environments implement private VLAN segmentation to group servers with similar applications.
D. Environments deploy centrally managed host-based firewall rules on each server or container -
Question 596:
Which solution for remote workers enables protection, detection, and response on the endpoint against known and unknown threats?
A. Cisco AMP for Endpoints
B. Cisco AnyConnect
C. Cisco Umbrella
D. Cisco Duo -
Question 597:
Which Cisco DNA Center Intent API action is used to retrieve the number of devices known to a DNA Center?
A. GET https://fqdnOrlPofDnaCenterPlatform/dna/intent/api/v1/network-device/count
B. GET https://fqdnOrlPofDnaCenterPlatform/dna/intent/api/v1/network-device
C. GET https://fqdnOrlPofDnaCenterPlatform/dna/intent/api/v1/networkdevice?parameter1=valueand parameter2=valueand....
D. GET https://fqdnOrlPofDnaCenterPlatform/dna/intent/api/v 1/networkdevice/startIndex/recordsToReturn -
Question 598:
Which RADIUS feature provides a mechanism to change the AAA attributes of a session after it is authenticated?
A. Authorization
B. Accounting
C. Authentication
D. CoA -
Question 599:
On which part of the IT environment does DevSecOps focus?
A. application development
B. wireless network
C. data center
D. perimeter network -
Question 600:
Refer to the exhibit.
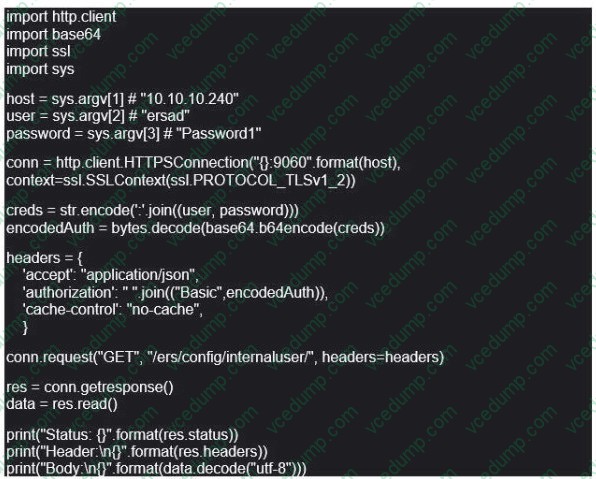
What does this Python script accomplish?
A. It allows authentication with TLSv1 SSL protocol
B. It authenticates to a Cisco ISE with an SSH connection.
C. lt authenticates to a Cisco ISE server using the username of ersad
D. It lists the LDAP users from the external identity store configured on Cisco ISE
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Cisco exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 350-701 exam preparations and Cisco certification application, do not hesitate to visit our Vcedump.com to find your solutions here.