312-50V7 Exam Details
-
Exam Code
:312-50V7 -
Exam Name
:Ethical Hacking and Countermeasures (CEHv7) -
Certification
:EC-COUNCIL Certifications -
Vendor
:EC-COUNCIL -
Total Questions
:514 Q&As -
Last Updated
:May 31, 2026
EC-COUNCIL 312-50V7 Online Questions & Answers
-
Question 431:
What is the outcome of the comm"nc -l -p 2222 | nc 10.1.0.43 1234"?
A. Netcat will listen on the 10.1.0.43 interface for 1234 seconds on port 2222.
B. Netcat will listen on port 2222 and output anything received to a remote connection on 10.1.0.43 port 1234.
C. Netcat will listen for a connection from 10.1.0.43 on port 1234 and output anything received to port 2222.
D. Netcat will listen on port 2222 and then output anything received to local interface 10.1.0.43. -
Question 432:
Bob has set up three web servers on Windows Server 2008 IIS 7.0. Bob has followed all the recommendations for securing the operating system and IIS. These servers are going to run numerous e-commerce websites that are projected to bring in thousands of dollars a day. Bob is still concerned about the security of these servers because of the potential for financial loss. Bob has asked his company's firewall administrator to set the firewall to inspect all incoming traffic on ports 80 and 443 to ensure that no malicious data is getting into the network.
Why will this not be possible?
A. Firewalls cannot inspect traffic coming through port 443
B. Firewalls can only inspect outbound traffic
C. Firewalls cannot inspect traffic at all, they can only block or allow certain ports
D. Firewalls cannot inspect traffic coming through port 80 -
Question 433:
Which of the following scanning tools is specifically designed to find potential exploits in Microsoft Windows products?
A. Microsoft Security Baseline Analyzer
B. Retina
C. Core Impact
D. Microsoft Baseline Security Analyzer -
Question 434:
SOAP services use which technology to format information?
A. SATA
B. PCI
C. XML
D. ISDN -
Question 435:
How can rainbow tables be defeated?
A. Password salting
B. Use of non-dictionary words
C. All uppercase character passwords
D. Lockout accounts under brute force password cracking attempts -
Question 436:
A company has publicly hosted web applications and an internal Intranet protected by a firewall. Which technique will help protect against enumeration?
A. Reject all invalid email received via SMTP.
B. Allow full DNS zone transfers.
C. Remove A records for internal hosts.
D. Enable null session pipes. -
Question 437:
What information should an IT system analysis provide to the risk assessor?
A. Management buy-in
B. Threat statement
C. Security architecture
D. Impact analysis -
Question 438:
At a Windows Server command prompt, which command could be used to list the running services?
A. Sc query type= running
B. Sc query \\servername
C. Sc query
D. Sc config -
Question 439:
Which definition below best describes a covert channel?
A. A server program using a port that is not well known
B. Making use of a protocol in a way it was not intended to be used
C. It is the multiplexing taking place on a communication link
D. It is one of the weak channels used by WEP that makes it insecure -
Question 440:
You establish a new Web browser connection to Google. Since a 3-way handshake is required for any TCP connection, the following actions will take place.
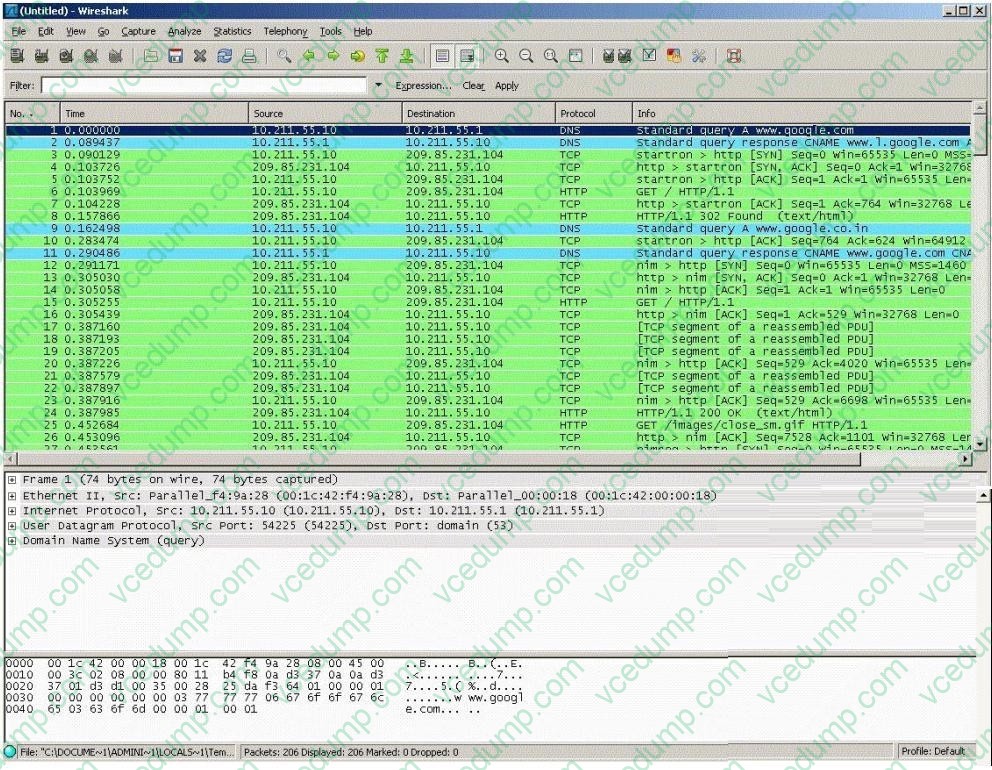
Which of the following packets represent completion of the 3-way handshake?
A. 4th packet
B. 3rdpacket
C. 6th packet
D. 5th packet
Related Exams:
-
112-51
EC-Council Certified Network Defense Essentials (NDE) -
212-055
Sun Certified Programmer for the Java 2 Platform.SE 5.0 -
212-77
EC-Council Certified Linux Security -
212-81
EC-Council Certified Encryption Specialist (ECES) -
212-82
EC-Council Certified Cybersecurity Technician (C|CT) -
212-89
EC Council Certified Incident Handler (ECIH v3) -
312-38
EC-Council Certified Network Defender (CND) -
312-39
EC-Council Certified SOC Analyst (CSA) -
312-40
EC-Council Certified Cloud Security Engineer (CCSE) -
312-49
ECCouncil Computer Hacking Forensic Investigator (V9)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 312-50V7 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.