Exam Details
Exam Code
:210-255Exam Name
:Cisco Cybersecurity OperationsCertification
:Cisco CertificationsVendor
:CiscoTotal Questions
:224 Q&AsLast Updated
:Nov 03, 2022
Cisco Cisco Certifications 210-255 Questions & Answers
-
Question 51:
What are two security goals of data normalization? (Choose two.)
A. purge redundant data
B. reduce size of data on disk
C. increase data exposure
D. maintain data integrity
E. create data for abstraction
-
Question 52:
Which statement about the collected evidence data when performing digital forensics is true?
A. It must be preserved and its integrity verified.
B. It must be copied to external storage media and immediately distributed to the CISO.
C. It must be deleted as soon as possible due to PCI compliance.
D. It must be stored in a forensics lab only by the data custodian.
-
Question 53:
Which incident handling phase is focused on minimizing the impact of the incident?
A. reporting
B. remediation
C. containment
D. scoping
-
Question 54:
Refer to the exhibit.
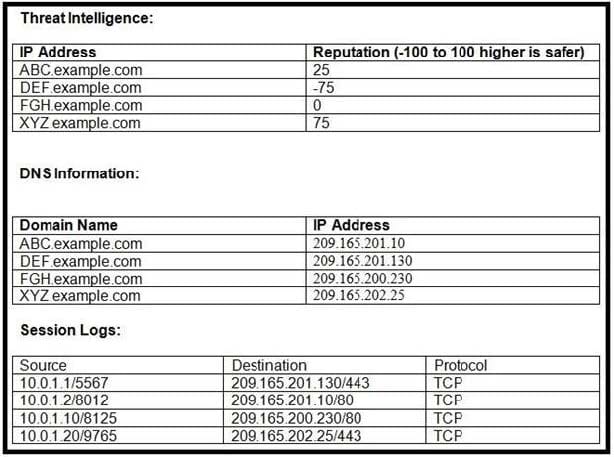
Which host is likely connecting to a malicious site?
A. 10.0.1.10
B. 10.0.1.1
C. 10.0.1.2
D. 10.0.1.20
-
Question 55:
Which file system has 32 bits assigned to the address clusters of the allocation table?
A. FAT32
B. NTFS
C. EXT4
D. FAT16
-
Question 56:
Which Cyber Kill Chain Model category does attacking a vulnerability belong to?
A. Exploitation
B. Action on Objectives
C. Installation
D. Delivery
-
Question 57:
According to NIST SP800-86, which action describes volatile data collection?
A. collection of data before a system reboot
B. collection of data that contains malware
C. collection of data during a system reboot
D. collection of data after a system reboot
-
Question 58:
What are the metric values for confidentiality impact in the CVSS v3.0 framework?
A. high, low
B. high, low, none
C. high, medium, none
D. open, closed, obsolete
-
Question 59:
You have a video of a suspect entering a data center that was captured on the same day that files in the same data center were transferred to a competitor. Which type of evidence is this?
A. indirect evidence
B. prima facie evidence
C. best evidence
D. physical evidence
-
Question 60:
What information is unnecessary for determining the appropriate containment strategy according to NIST SP800-61 r2?
A. attack vector used to compromise the system
B. effectiveness of the strategy
C. time and resources needed to implement the strategy
D. need for evidence preservation
Related Exams:
300-915
Developing Solutions using Cisco IoT and Edge Platforms (DEVIOT)300-920
Developing Applications for Cisco Webex and Webex Devices (DEVWBX)352-011
Cisco Certified Design Expert Practical500-052
Cisco Unified Contact Center Express500-173
Designing the FlexPod Solution (FPDESIGN)500-174
Implementing and Administering the FlexPod Solution (FPIMPADM)500-201
Deploying Cisco Service Provider Mobile Backhaul Solutions500-210
SP Optical Technology Field Engineer Representative500-220
Cisco Meraki Solutions Specialist500-230
Cisco Service Provider Routing Field Engineer
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Cisco exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 210-255 exam preparations and Cisco certification application, do not hesitate to visit our Vcedump.com to find your solutions here.