156-215.81.20 Exam Details
-
Exam Code
:156-215.81.20 -
Exam Name
:Check Point Certified Security Administrator - R81.20 (CCSA) -
Certification
:Checkpoint Certifications -
Vendor
:CheckPoint -
Total Questions
:677 Q&As -
Last Updated
:May 26, 2026
CheckPoint 156-215.81.20 Online Questions & Answers
-
Question 371:
Which Check Point feature enables application scanning and the detection?
A. Application Dictionary
B. AppWiki
C. Application Library
D. CPApp -
Question 372:
What is the default shell of Gaia CLI?
A. Monitor
B. CLI.sh
C. Read-only
D. Bash -
Question 373:
Which type of Check Point license is tied to the IP address of a specific Security Gateway and cannot be transferred to a gateway that has a different IP address?
A. Formal
B. Central
C. Local
D. Corporate -
Question 374:
Examine the sample Rule Base.
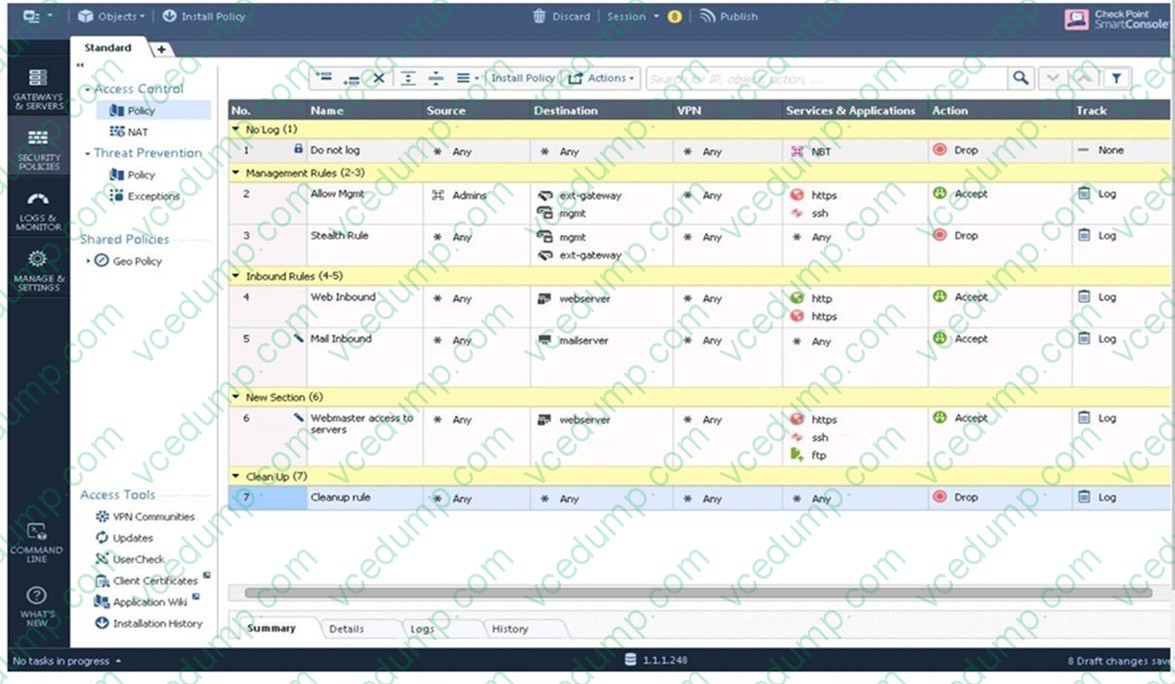
What will be the result of a verification of the policy from SmartConsole?
A. No errors or Warnings
B. Verification Error. Empty Source-List in Rule 5 (Mail Inbound) C. Verification Error. Rule 4 (Web Inbound) hides Rule 6 (Webmaster access)
D. Verification Error. Rule 7 (Clean-Up Rule) hides Implicit Clean-up Rule -
Question 375:
Fill in the blank: The R80 utility fw monitor is used to troubleshoot _____________
A. User data base corruption
B. LDAP conflicts
C. Traffic issues
D. Phase two key negotiation -
Question 376:
In SmartConsole, objects are used to represent physical and virtual network components and also some logical components. These objects are divided into several categories. Which of the following is NOT an objects category?
A. Limit
B. Resource
C. Custom Application / Site
D. Network Object -
Question 377:
In SmartEvent, what are the different types of automatic reactions that the administrator can configure?
A. Mail, Block Source, Block Event Activity, External Script, SNMP Trap
B. Mail, Block Source, Block Destination, Block Services, SNMP Trap
C. Mail, Block Source, Block Destination, External Script, SNMP Trap
D. Mail, Block Source, Block Event Activity, Packet Capture, SNMP Trap -
Question 378:
Which authentication scheme requires a user to possess a token?
A. TACACS
B. SecurID
C. Check Point password
D. RADIUS -
Question 379:
What happens if the identity of a user is known?
A. If the user credentials do not match an Access Role, the system displays the Captive Portal.
B. If the user credentials do not match an Access Role, the system displays a sandbox.
C. If the user credentials do not match an Access Role, the traffic is automatically dropped.
D. If the user credentials match an Access Role, the rule is applied and traffic is accepted or dropped based on the defined action. -
Question 380:
Where is the "Hit Count" feature enabled or disabled in SmartConsole?
A. In Global Properties.
B. On each Security Gateway.
C. On the Policy layer.
D. On the Policy Package.
Related Exams:
-
156-110
Check Point Certified Security Principles Associate (CCSPA) -
156-115.80
Check Point Certified Security Master - R80 -
156-215
Check Point Security Administration NGX -
156-215.1
Check Point Certified Security Administrator NGX -
156-215.70
Check Point Certified Security Administrator R70 -
156-215.71
Check Point Certified Security Administrator R71 -
156-215.75
Check Point Certified Security Administrator -
156-215.80
Check Point Certified Security Administrator (CCSA) -
156-215.81
Check Point Certified Security Administrator - R81 (CCSA) -
156-215.81.20
Check Point Certified Security Administrator - R81.20 (CCSA)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CheckPoint exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 156-215.81.20 exam preparations and CheckPoint certification application, do not hesitate to visit our Vcedump.com to find your solutions here.