SY0-501 Exam Details
-
Exam Code
:SY0-501 -
Exam Name
:CompTIA Security+ -
Certification
:CompTIA Certifications -
Vendor
:CompTIA -
Total Questions
:1423 Q&As -
Last Updated
:Sep 04, 2023
CompTIA SY0-501 Online Questions & Answers
-
Question 591:
A director of IR is reviewing a report regarding several recent breaches. The director compiles the following statistic's -Initial IR engagement time frame -Length of time before an executive management notice went out -Average IR phase completion The director wants to use the data to shorten the response time. Which of the following would accomplish this?
A. CSIRT
B. Containment phase
C. Escalation notifications
D. Tabletop exercise -
Question 592:
Which of the following attack types BEST describes a client-side attack that is used to manipulate an HTML iframe with JavaScript code via a web browser?
A. Buffer overflow
B. MITM
C. XSS
D. SQLi -
Question 593:
Which of the following scenarios would make a DNS sinkhole effective in thwarting an attack?
A. An attacker is sniffing traffic to port 53, and the server is managed using unencrypted usernames and passwords.
B. An organization is experiencing excessive traffic on port 53 and suspects an attacker is trying to DoS the domain name server.
C. Malware is trying to resolve an unregistered domain name to determine if it is running in an isolated sandbox.
D. DNS routing tables have been compromised, and an attacker is rerouting traffic to malicious websites. -
Question 594:
A security team wants to establish an Incident Response plan. The team has never experienced an incident. Which of the following would BEST help them establish plans and procedures?
A. Table top exercises
B. Lessons learned
C. Escalation procedures
D. Recovery procedures -
Question 595:
An organization with very high security needs wants to implement a biometric system. It is required to minimize unauthorized access by ensuring authorized personnel are not denied access. Which of the following solutions will work?
A. A device with a low false acceptance rate and a high false rejection rate
B. A device with a high false acceptance rate and a high false rejection rate
C. A device with a high false acceptance rate and a low false rejection rate
D. A device with a low false acceptance rate and a low false rejection rate -
Question 596:
Which of the following BEST describes why an air gap is a useful security control?
A. It physically isolates two or more networks, therefore helping prevent cross contamination or accidental data spillage.
B. It requires that files be transferred via USB instead of networks that are potentially vulnerable to hacking, therefore preventing virus infections.
C. It requires multiple systems administrators with different credentials, therefore providing separation of duties.
D. It provides physical space between two interlocking doors, therefore providing additional control from unauthorized entry. -
Question 597:
A systems administrator wants to provide balance between the security of a wireless network and usability. The administrator is concerned with wireless encryption compatibility of older devices used by some employees. Which of the following would provide strong security and backward compatibility when accessing the wireless network?
A. Open wireless network and SSL VPN
B. WPA using a preshared key
C. WPA2 using a RADIUS back-end for 802.1x authentication
D. WEP with a 40-bit key -
Question 598:
Fuzzing is used to reveal which of the following vulnerabilities in web applications?
A. Weak cipher suites
B. Improper input handling
C. DLL injection
D. Certificate signing flaws -
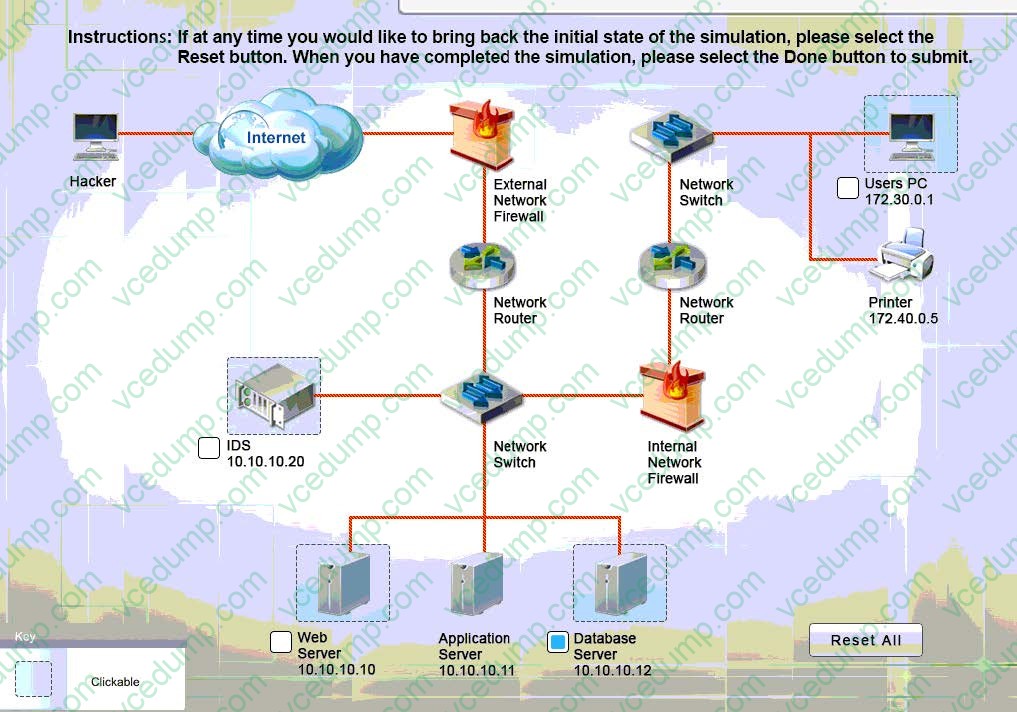
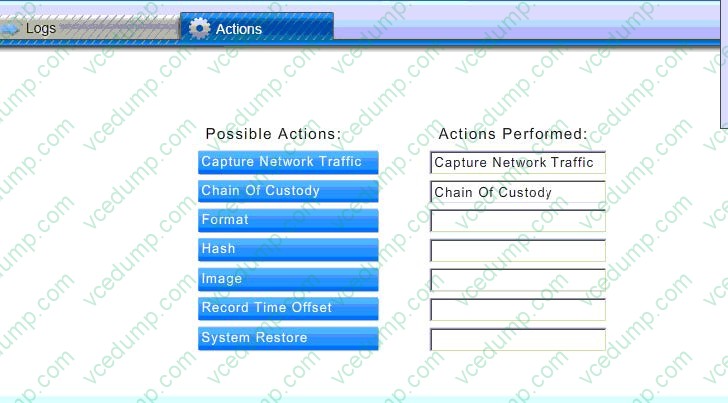
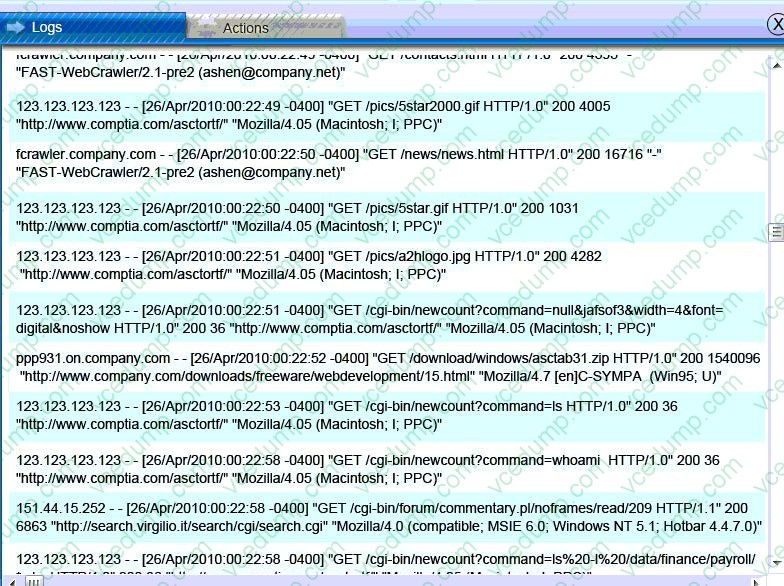
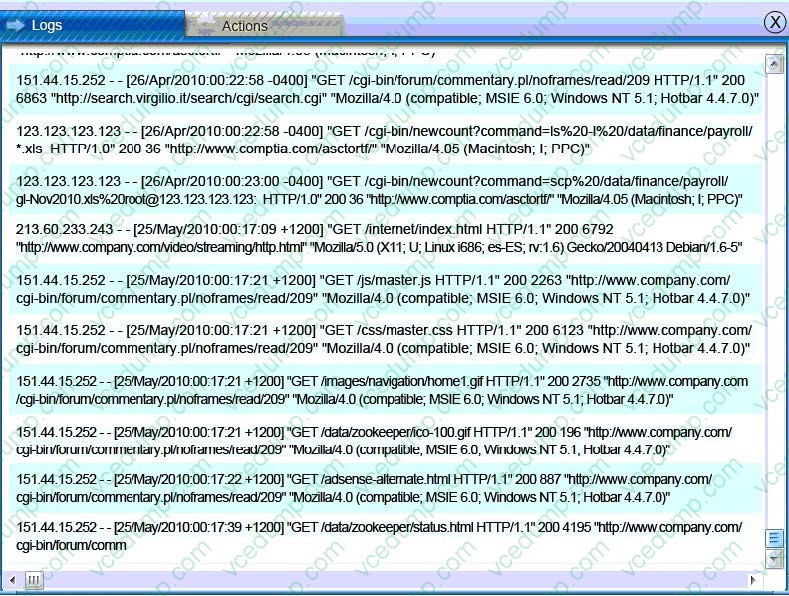
Question 599:
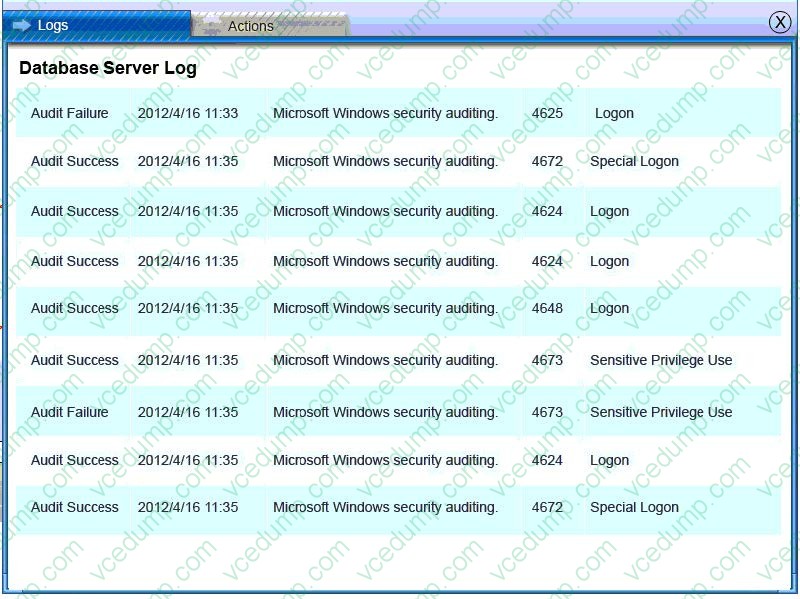
A security administrator discovers that an attack has been completed against a node on the corporate network. All available logs were collected and stored.
You must review all network logs to discover the scope of the attack, check the box of the node(s) that have been compromised and drag and drop the appropriate actions to complete the incident response on the network. The environment is
a critical production environment; perform the LEAST disruptive actions on the network, while still performing the appropriate incident responses.
Instructions: The web server, database server, IDS, and User PC are clickable. Check the box of the node(s) that have been compromised and drag and drop the appropriate actions to complete the incident response on the network. Not all
actions may be used, and order is not important. If at anytime you would like to bring back the initial state of the simulation, please select the Reset button. When you have completed the simulation, please select the Done button to submit.
Once the simulation is submitted, please select the Next button to continue.
Correct Answer. Check the answer below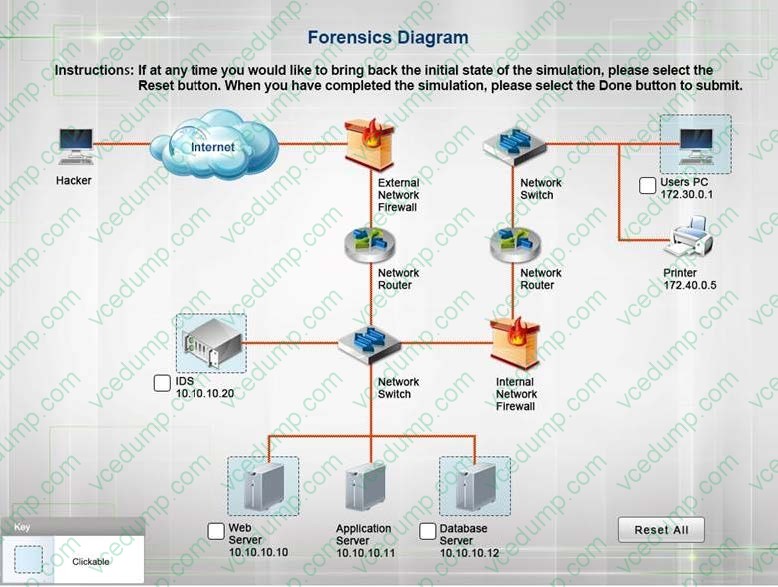
-
Question 600:
An administrator is implementing a secure web server and wants to ensure that if the web server application s compromised, the application does not have access to other parts of the server or network. Which of the following should the administrator implement? (Select TWO.)
A. Mandatory access control
B. Discretionary access control
C. Rule-based access control
D. Role-based access control
E. Attribute-based access control
Related Exams:
-
220-1001
CompTIA A+ Certification: Core 1 -
220-1002
CompTIA A+ Certification: Core 2 -
220-1101
CompTIA A+ Certification: Core 1 -
220-1102
CompTIA A+ Certification: Core 2 -
220-1201
CompTIA A+ Certification: Core 1 -
220-1202
CompTIA A+ Core 2 (2026) -
220-902
CompTIA A+ Certification -
CAS-004
CompTIA Advanced Security Practitioner (CASP+) -
CAS-005
CompTIA SecurityX -
CLO-001
CompTIA Cloud Essentials+
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your SY0-501 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.