SY0-501 Exam Details
-
Exam Code
:SY0-501 -
Exam Name
:CompTIA Security+ -
Certification
:CompTIA Certifications -
Vendor
:CompTIA -
Total Questions
:1423 Q&As -
Last Updated
:Sep 04, 2023
CompTIA SY0-501 Online Questions & Answers
-
Question 181:
A system uses an application server and database server. Employing the principle of least privilege, only database administrators are given administrative privileges on the database server, and only application team members are given administrative privileges on the application server. Audit and log file reviews are performed by the business unit (a separate group from the database and application teams).
The organization wants to optimize operational efficiency when application or database changes are needed, but it also wants to enforce least privilege, prevent modification of log files, and facilitate the audit and log review performed by the business unit.
Which of the following approaches would BEST meet the organization's goals?
A. Restrict privileges on the log file directory to "read only" and use a service account to send a copy of these files to the business unit.
B. Switch administrative privileges for the database and application servers. Give the application team administrative privileges on the database servers and the database team administrative privileges on the application servers.
C. Remove administrative privileges from both the database and application servers, and give the business unit "read only" privileges on the directories where the log files are kept.
D. Give the business unit administrative privileges on both the database and application servers so they can independently monitor server activity. -
Question 182:
While troubleshooting a client application connecting to the network, the security administrator notices the following error: Certificate is not valid. Which of the following is the BEST way to check if the digital certificate is valid?
A. PKI
B. CRL
C. CSR
D. IPSec -
Question 183:
A security technician has been receiving alerts from several servers that indicate load balancers have had a significant increase in traffic. The technician initiates a system scan. The scan results illustrate that the disk space on several servers has reached capacity. The scan also indicates that incoming internet traffic to the servers has increased. Which of the following is the MOST likely cause of the decreased disk space?
A. Misconfigured devices
B. Logs and events anomalies
C. Authentication issues
D. Unauthorized software -
Question 184:
Refer to the following code:
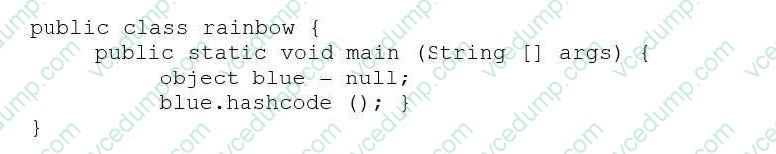
Which of the following vulnerabilities would occur if this is executed?
A. Page exception
B. Pointer deference
C. NullPointerException
D. Missing null check -
Question 185:
A security administrator is implementing a new WAF solution and has placed some of the web servers behind the WAF, with the WAF set to audit mode. When reviewing the audit logs of external requests and posts to the web servers, the administrator finds the following entry:

Based on this data, which of the following actions should the administrator take?
A. Alert the web server administrators to a misconfiguration.
B. Create a blocking policy based on the parameter values.
C. Change the parameter name `Account_Name' identified in the log.
D. Create an alert to generate emails for abnormally high activity. -
Question 186:
Joe a new employee, discovered a thumb drive with the company's logo on it while walking in the parking lot Joe was curious as to the contents of the drive and placed it into his work computer. Shortly after accessing the contents, he noticed the machine was running slower, started to reboot, and displayed new icons on the screen. Which of the following types of attacks occurred?
A. Social engineering
B. Brute force attack
C. MITM
D. DoS -
Question 187:
A security administrator is investigating many recent incident of credential theft for users accessing the company's website, despite the hosting web server requiring HTTPS for access. The server's logs show the website leverages the HTTO POST method for carrying user authentication details. Which of the following is the MOST likely reason for compromise?
A. The HTTP POST method is not protected by HTTPS.
B. The web server is running a vulnerable SSL configuration.
C. The company does not support DNSSEC.
D. The HTTP response is susceptible to sniffing. -
Question 188:
To reduce costs and overhead, an organization wants to move from an on-premises email solution to a cloud-based email solution. At this time, no other services will be moving. Which of the following cloud models would BEST meet the needs of the organization?
A. MaaS
B. IaaS
C. SaaS
D. PaaS -
Question 189:
Which of the following generates reports that show the number of systems that are associated with POODLE, 3DES, and SMBv1 listings?
A. A protocol analyzer
B. A UTM appliance
C. A vulnerability scanner
D. A honeypot -
Question 190:
After successfully breaking into several networks and infecting multiple machines with malware. hackers contact the network owners, demanding payment to remove the infection and decrypt files. The hackers threaten to publicly release information about the breach if they are not paid. Which of the following BEST describes these attackers?
A. Gray hat hackers
B. Organized crime
C. Insiders
D. Hacktivists
Related Exams:
-
220-1001
CompTIA A+ Certification: Core 1 -
220-1002
CompTIA A+ Certification: Core 2 -
220-1101
CompTIA A+ Certification: Core 1 -
220-1102
CompTIA A+ Certification: Core 2 -
220-1201
CompTIA A+ Certification: Core 1 -
220-1202
CompTIA A+ Core 2 (2026) -
220-902
CompTIA A+ Certification -
CAS-004
CompTIA Advanced Security Practitioner (CASP+) -
CAS-005
CompTIA SecurityX -
CLO-001
CompTIA Cloud Essentials+
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your SY0-501 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.