Exam Details
Exam Code
:PCCETExam Name
:Palo Alto Networks Certified Cybersecurity Entry-level Technician (PCCET)Certification
:Palo Alto Networks CertificationsVendor
:Palo Alto NetworksTotal Questions
:200 Q&AsLast Updated
:Aug 15, 2025
Palo Alto Networks Palo Alto Networks Certifications PCCET Questions & Answers
-
Question 11:
Which option describes the "selective network security virtualization" phase of incrementally transforming data centers?
A. during the selective network security virtualization phase, all intra-host communication paths are strictly controlled
B. during the selective network security virtualization phase, all intra-host traffic is forwarded to a Web proxy server
C. during the selective network security virtualization phase, all intra-host traffic is encapsulated and encrypted using the IPSEC protocol
D. during the selective network security virtualization phase, all intra-host traffic is load balanced
-
Question 12:
Which tool supercharges security operations center (SOC) efficiency with the world's most comprehensive operating platform for enterprise security?
A. Prisma SAAS
B. WildFire
C. Cortex XDR
D. Cortex XSOAR
-
Question 13:
Which network device breaks networks into separate broadcast domains?
A. Hub
B. Layer 2 switch
C. Router
D. Wireless access point
-
Question 14:
In which step of the cyber-attack lifecycle do hackers embed intruder code within seemingly innocuous files?
A. weaponization
B. reconnaissance
C. exploitation
D. delivery
-
Question 15:
Which core component is used to implement a Zero Trust architecture?
A. VPN Concentrator
B. Content Identification
C. Segmentation Platform
D. Web Application Zone
-
Question 16:
On an endpoint, which method should you use to secure applications against exploits?
A. endpoint-based firewall
B. strong user passwords
C. full-disk encryption
D. software patches
-
Question 17:
What is a characteristic of the National Institute Standards and Technology (NIST) defined cloud computing model?
A. requires the use of only one cloud service provider
B. enables on-demand network services
C. requires the use of two or more cloud service providers
D. defines any network service
-
Question 18:
In the attached network diagram, which device is the switch?
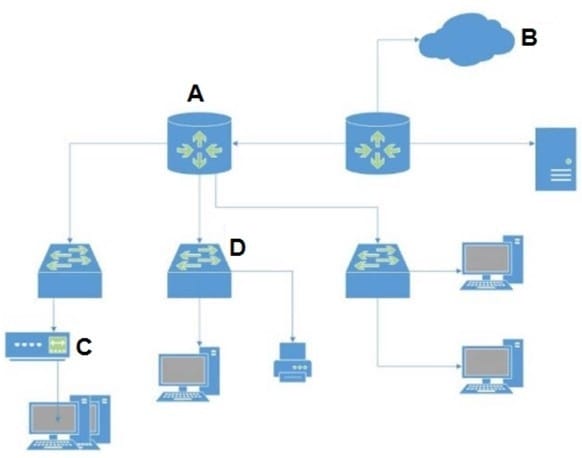
A. A
B. B
C. C
D. D
-
Question 19:
Which three layers of the OSI model correspond to the Application Layer (L4) of the TCP/IP model?
A. Session, Transport, Network
B. Application, Presentation, and Session
C. Physical, Data Link, Network
D. Data Link, Session, Transport
-
Question 20:
Which product from Palo Alto Networks enables organizations to prevent successful cyberattacks as well as simplify and strengthen security processes?
A. Expedition
B. AutoFocus
C. MineMeld
D. Cortex XDR
Related Exams:
PAN-NGFE
Palo Alto Networks Network Next-Generation Firewall EngineerPAN-NSG
Palo Alto Networks Network Security GeneralistPAN-NSP
Palo Alto Networks Network Security ProfessionalPAN-SSEE
Palo Alto Networks Security Service Edge EngineerPAN-XDRE
Palo Alto Networks XDR EngineerPCCET
Palo Alto Networks Certified Cybersecurity Entry-level Technician (PCCET)PCCSA
Palo Alto Networks Certified Cybersecurity Associate (PCCSA)PCCSE
Prisma Certified Cloud Security Engineer (PCCSE)PCDRA
Palo Alto Networks Certified Detection and Remediation Analyst (PCDRA)PCNSA
Palo Alto Networks Certified Network Security Administrator (PCNSA)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Palo Alto Networks exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your PCCET exam preparations and Palo Alto Networks certification application, do not hesitate to visit our Vcedump.com to find your solutions here.