Exam Details
Exam Code
:JN0-334Exam Name
:Security, Specialist (JNCIS-SEC)Certification
:Juniper CertificationsVendor
:JuniperTotal Questions
:90 Q&AsLast Updated
:Aug 05, 2025
Juniper Juniper Certifications JN0-334 Questions & Answers
-
Question 31:
How many nodes are configurable in a chassis cluster using SRX Series devices?
A. 2
B. 4
C. 6
D. 8
-
Question 32:
Which two functions are performed by Juniper Identity Management Service (JIMS)? (Choose two.)
A. JIMS synchronizes Active Directory authentication information between a primary and secondary JIMS server.
B. JIMS forwards Active Directory authentication information to SRX Series client devices.
C. JIMS collects and maintains a database of authentication information from Active Directory domains.
D. JIMS replicates Active Directory authentication information to non-trusted Active Directory domain controllers.
-
Question 33:
Click the Exhibit button.

Referring to the exhibit, which statement is true?
A. IDP blocks root users.
B. IDP closes the connection on matched sessions.
C. IDP ignores the connection on matched sessions.
D. IDP blocks all users.
-
Question 34:
You want to use Sky ATP to protect your network; however, company policy does not allow you to send any files to the cloud.
Which Sky ATP feature should you use in this situation?
A. Only use on-premises local Sky ATP server anti-malware file scanning.
B. Only use cloud-based Sky ATP file hash lookups.
C. Only use on-box SRX anti-malware file scanning.
D. Only use cloud-based Sky ATP file blacklists.
-
Question 35:
Click the Exhibit button.
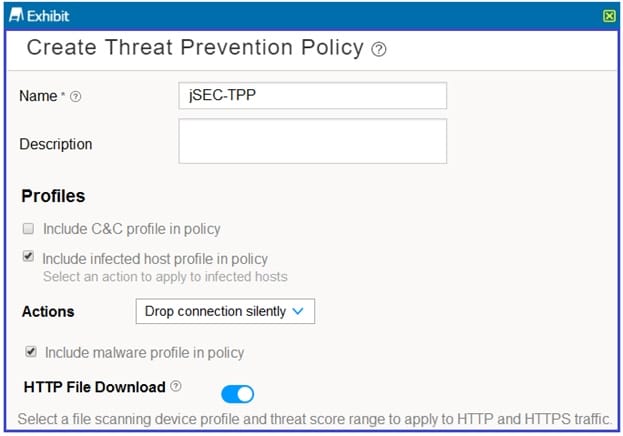
Referring to the exhibit, which statement is true?
A. Hosts are always able to communicate through the SRX Series device no matter the threat score assigned to them on the infected host feed.
B. Hosts are unable to communicate through the SRX Series device after being placed on the infected host feed with a high enough threat score.
C. Malicious HTTP file downloads are never blocked.
D. Malicious HTTP file downloads are always blocked.
-
Question 36:
Which two settings must be enabled on the hypervisor in a vSRX deployment to ensure proper chassis cluster operation? (Choose two.)
A. Control links must operate in promiscuous mode.
B. Control links must have an MTU of 9000.
C. Fabric links must operate in promiscuous mode.
D. Fabric links must have an MTU of 9000.
-
Question 37:
You have deployed JSA and you need to view events and network activity that match rule criteria. You must view this data using a single interface.
Which JSA feature should you use in this scenario?
A. Log Collector
B. Assets
C. Network Activity
D. Offense Manager
-
Question 38:
Which two statements describe JSA? (Choose two.)
A. Security Director must be used to view third-party events rom JSA flow collectors.
B. JSA supports events and flows from Junos devices, including third-party devices.
C. JSA events must be manually imported into Security Directory using an SSH connection.
D. JSA can be used as a log node with Security Director or as a standalone solution.
-
Question 39:
What is the maximum number of supported interfaces on a vSRX hosted in a VMware environment?
A. 4
B. 10
C. 3
D. 12
-
Question 40:
Which feature is used when you want to permit traffic on an SRX Series device only at specific times?
A. scheduler
B. pass-through authentication
C. ALGs
D. counters
Related Exams:
JN0-102
Internet Associate, Junos(JNCIA-Junos)JN0-104
Junos, Associate (JNCIA-Junos)JN0-105
Junos, Associate (JNCIA-Junos)JN0-1101
Juniper Networks Certified Design Associate (JNCDA)JN0-1103
Design, Associate (JNCIA-Design)JN0-130
Juniper networks Certified internet specialist.e(jncis-e)JN0-1301
Data Center Design, Specialist (JNCDS-DC)JN0-1302
Data Center Design Specialist (JNCDS-DC)JN0-1331
Security Design, Specialist (JNCDS-SEC)JN0-1332
Security Design, Specialist (JNCDS-SEC)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Juniper exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your JN0-334 exam preparations and Juniper certification application, do not hesitate to visit our Vcedump.com to find your solutions here.