Exam Details
Exam Code
:JN0-1331Exam Name
:Security Design, Specialist (JNCDS-SEC)Certification
:Juniper CertificationsVendor
:JuniperTotal Questions
:65 Q&AsLast Updated
:Jun 27, 2025
Juniper Juniper Certifications JN0-1331 Questions & Answers
-
Question 21:
Which two steps should be included in your security design process? (Choose two.)
A. Identify external attackers
B. Define safety requirements for the customer's organization
C. Identify the firewall enforcement points
D. Define overall security policies
-
Question 22:
Which two protocols are supported natively by the Junos automation stack? (Choose two.)
A. NETCONF
B. PyEZ
C. Jenkins
D. CIP
-
Question 23:
You are implementing Routing Engine protection, and packets are processed in a specific order. In this scenario, which function processed a received packet last?
A. loopback interface input policer
B. loopback interface input firewall filter
C. physical interface input firewall filters
D. physical interface input policer
-
Question 24:
Which statement about IPsec tunnels is true?
A. They are used to provide in-depth packet inspection for traffic leaving your network
B. They are used to prevent routing loops in a Layer 2 environment
C. They are used to secure and encrypt traffic between tunnel endpoints
D. They are used to combine multiple interfaces into a single bundle
-
Question 25:
Click the Exhibit button.
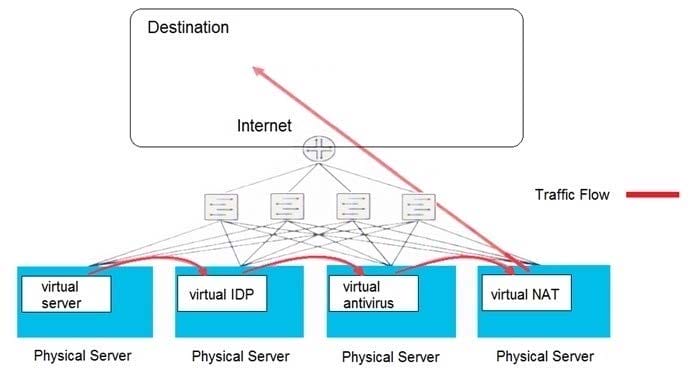
Which type of security solution is shown in this exhibit?
A. service chain model
B. centralized model
C. inline security model
D. de-centralized model
-
Question 26:
You are creating a data center security design. Virtual security functions must be performed on east-west traffic. Security functions must be commissioned and decommissioned frequently, and the least resource-intensive architecture must be used.
In this scenario, what will accomplish this task?
A. all-in-one NFV security devices with device templates
B. service chaining with container-based security functions
C. a security appliance segmented into logical systems
D. filter-based forwarding to direct traffic to the required security devices
-
Question 27:
What are two benefits of the vSRX in a virtualized private or public cloud multitenant environment? (Choose two.)
A. full logical systems capabilities
B. stateful firewall protection at the tenant edge
C. 100GbE interface support
D. OSPFv3 capabilities
-
Question 28:
You are working on a network design that will use EX Series devices as Layer 2 access switches in a campus environment. You must include Junos Space in your design. You want to take advantage of security features supported on the devices.
Which two security features would satisfy this requirement? (Choose two.)
A. SDSN
B. Stateful Firewall
C. Access Control
D. ALG
-
Question 29:
You have a site that has two Internet connections but no switch on the outside of the firewall. You want to use ISP-A over ISP-B during normal operations.
Which type of chassis cluster design would you propose to satisfy this requirement?
A. Propose active/active cluster deployment with separate redundancy groups
B. Propose active/passive cluster deployment with separate redundancy groups
C. Propose active/active cluster deployment without separate redundancy groups
D. Propose active/passive cluster deployment without separate redundancy groups
-
Question 30:
You are designing an SDSN security solution for a new campus network. The network will consist of Juniper Networks Policy Enforcer, Juniper Networks switches, third-party switches, and SRX Series devices. The switches and the SRX Series devices will be used as security enforcement points.
Which component supports the SRX Series devices in this scenario?
A. Security Director
B. RADIUS server
C. certificate server
D. DHCP server
Related Exams:
JN0-102
Internet Associate, Junos(JNCIA-Junos)JN0-104
Junos, Associate (JNCIA-Junos)JN0-105
Junos, Associate (JNCIA-Junos)JN0-1101
Juniper Networks Certified Design Associate (JNCDA)JN0-1103
Design, Associate (JNCIA-Design)JN0-130
Juniper networks Certified internet specialist.e(jncis-e)JN0-1301
Data Center Design, Specialist (JNCDS-DC)JN0-1302
Data Center Design Specialist (JNCDS-DC)JN0-1331
Security Design, Specialist (JNCDS-SEC)JN0-1332
Security Design, Specialist (JNCDS-SEC)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Juniper exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your JN0-1331 exam preparations and Juniper certification application, do not hesitate to visit our Vcedump.com to find your solutions here.