Exam Details
Exam Code
:CV0-003Exam Name
:CompTIA Cloud+Certification
:CompTIA CertificationsVendor
:CompTIATotal Questions
:503 Q&AsLast Updated
:Aug 08, 2025
CompTIA CompTIA Certifications CV0-003 Questions & Answers
-
Question 1:
A cloud administrator received a request to provision a set of cloud resources in an effort to switch to infrastructure as code to automate and optimize operations. The administrator decides to try to run some tests with the following definition:
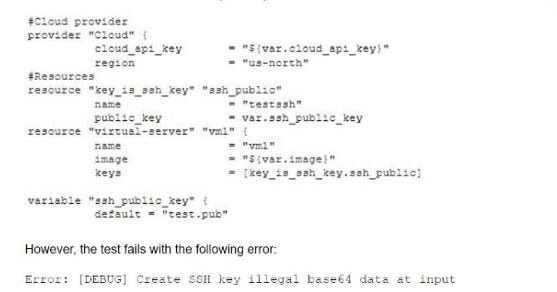
Which of the following is the most likely cause of the issue?
A. The cloud provider is expecting the private key.
B. The incorrect resource name was used.
C. The environment variable for the public key path has not been set.
D. An unexpected variable was provided.
-
Question 2:
A startup online gaming company is designing the optimal graphical user experience for multiplayer scenarios. However, online players have reported latency issues. Which of the following should the company configure as a remediation?
A. Additional GPU memory
B. Faster clock speed
C. Additional CPU cores
D. Dynamic allocations
-
Question 3:
Which of the following would be the BEST option for discussion of what individuals should do in an incident response or disaster recovery scenario?
A. A business continuity plan
B. Incident response/disaster recovery documentation
C. A tabletop exercise
D. A root cause analysis
-
Question 4:
A DevOps administrator is automating an existing software development workflow. The administrator wants to ensure that prior to any new code going into production, tests confirm the new code does not negatively impact existing automation activities.
Which of the following testing techniques would be BEST to use?
A. Usability testing
B. Regression testing
C. Vulnerability testing
D. Penetration testing
-
Question 5:
A systems administrator is implementing a new file storage service that has been deployed in the company's private cloud instance. The key requirement is fast read/write times for the targeted users, and the budget for this project is not a concern. Which of the following storage types should the administrator deploy?
A. Spinning disks
B. NVMe
C. SSD
D. Hybrid
-
Question 6:
A cloud engineer, who manages workloads in a public cloud environment, uses autoscaling to maintain availability of a critical application. During a recent burst in demands, the engineer received the following error alert:
LimitedInstanceCapacity
Which of the following is MOST likely cause of the error?
A. The cloud account has a misconfigured security group.
B. The cloud account has exhausted the number of instances quota.
C. The cloud account has had rights revoked to create instances.
D. The autoscaling feature does not have permissions to create instances.
-
Question 7:
A non-critical file on a database server was deleted and needs to be recovered. A cloud administrator must use the least disruptive restoration process to retrieve the file, as the database server cannot be stopped during the business day. Which of the following restoration methods would BEST accomplish this goal?
A. Alternate location
B. Restore from image
C. Revert to snapshot
D. In-place restoration
-
Question 8:
A company has entered into a business relationship with another organization and needs to provide access to internal resources through directory services. Which of the following should a systems administrator implement?
A. SSO
B. VPN
C. SSH
D. SAML
-
Question 9:
A company is planning its cloud architecture and wants to use a VPC for each of its three products per environment in two regions, totaling 18 VPCs. The products have interdependences, consuming services between VPCs. Which of the following should the cloud architect use to connect all the VPCs?
A. MPLS connections
B. VPC peering
C. Hub and spoke
D. VPN connections
-
Question 10:
A cloud administrator receives an email stating the following:
“Clients are receiving emails from our web application with non-encrypted links.”
The administrator notices that links generated from the web application are opening in http://. Which of the following should be configured to redirect the traffic to https://?
A. User account access
B. Programming code
C. Web server configuration
D. Load balancer setting
Related Exams:
220-1001
CompTIA A+ Certification: Core 1220-1002
CompTIA A+ Certification: Core 2220-1101
CompTIA A+ Certification: Core 1220-1102
CompTIA A+ Certification: Core 2220-1201
CompTIA A+ Certification: Core 1220-1202
CompTIA A+ Certification: Core 2220-902
CompTIA A+ CertificationCAS-004
CompTIA Advanced Security Practitioner (CASP+)CAS-005
CompTIA SecurityXCLO-001
CompTIA Cloud Essentials+
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CV0-003 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.