Exam Details
Exam Code
:CIPTExam Name
:Certified Information Privacy Technologist (CIPT)Certification
:IAPP CertificationsVendor
:IAPPTotal Questions
:274 Q&AsLast Updated
:Jun 25, 2025
IAPP IAPP Certifications CIPT Questions & Answers
-
Question 31:
A user who owns a resource wants to give other individuals access to the resource. What control would apply?
A. Mandatory access control.
B. Role-based access controls.
C. Discretionary access control.
D. Context of authority controls.
-
Question 32:
What is a main benefit of data aggregation?
A. It is a good way to perform analysis without needing a statistician.
B. It applies two or more layers of protection to a single data record.
C. It allows one to draw valid conclusions from small data samples.
D. It is a good way to achieve de-identification and unlinkabilty.
-
Question 33:
Which of the following would be the best method of ensuring that Information Technology projects follow Privacy by Design (PbD) principles?
A. Develop a technical privacy framework that integrates with the development lifecycle.
B. Utilize Privacy Enhancing Technologies (PETs) as a part of product risk assessment and management.
C. Identify the privacy requirements as a part of the Privacy Impact Assessment (PIA) process during development and evaluation stages.
D. Develop training programs that aid the developers in understanding how to turn privacy requirements into actionable code and design level specifications.
-
Question 34:
How does browser fingerprinting compromise privacy?
A. By creating a security vulnerability.
B. By differentiating users based upon parameters.
C. By persuading users to provide personal information.
D. By customizing advertising based on the geographic location.
-
Question 35:
What must be used in conjunction with disk encryption?
A. Increased CPU speed.
B. A strong password.
C. A digital signature.
D. Export controls.
-
Question 36:
Which of the following would be an example of an "objective" privacy harm to an individual?
A. Receiving spam following the sale an of email address.
B. Negative feelings derived from government surveillance.
C. Social media profile views indicating unexpected interest in a person.
D. Inaccuracies in personal data.
-
Question 37:
What is a mistake organizations make when establishing privacy settings during the development of applications?
A. Providing a user with too many choices.
B. Failing to use "Do Not Track" technology.
C. Providing a user with too much third-party information.
D. Failing to get explicit consent from a user on the use of cookies.
-
Question 38:
SCENARIO
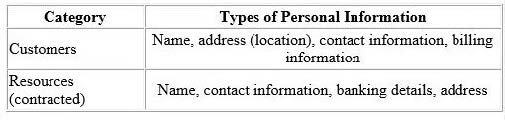
Clean-Q is a company that offers house-hold and office cleaning services. The company receives requests from consumers via their website and telephone, to book cleaning services. Based on the type and size of service, Clean-Q then contracts individuals that are registered on its resource database - currently managed in-house by Clean-Q IT Support. Because of Clean-Q's business model, resources are contracted as needed instead of permanently employed. The table below indicates some of the personal information Clean-Q requires as part of its business operations:
Clean-Q has an internal employee base of about 30 people. A recent privacy compliance exercise has been conducted to align employee data management and human resource functions with applicable data protection regulation. Therefore,
the Clean-Q permanent employee base is not included as part of this scenario.
With an increase in construction work and housing developments, Clean-Q has had an influx of requests for cleaning services. The demand has overwhelmed Clean-Q's traditional supply and demand system that has caused some
overlapping bookings.
Ina business strategy session held by senior management recently, Clear-Q invited vendors to present potential solutions to their current operational issues. These vendors included Application developers and Cloud-Q's solution providers,
presenting their proposed solutions and platforms.
The Managing Director opted to initiate the process to integrate Clean-Q's operations with a cloud solution (LeadOps) that will provide the following solution one single online platform: A web interface that Clean-Q accesses for the purposes
of resource and customer management. This would entail uploading resource and customer information.
A customer facing web interface that enables customers to register, manage and submit cleaning service requests online.
A resource facing web interface that enables resources to apply and manage their assigned jobs.
An online payment facility for customers to pay for services.
Considering that LeadOps will host/process personal information on behalf of Clean-Q remotely, what is an appropriate next step for Clean-Q senior management to assess LeadOps' appropriateness?
A. Nothing at this stage as the Managing Director has made a decision.
B. Determine if any Clean-Q competitors currently use LeadOps as a solution.
C. Obtain a legal opinion from an external law firm on contracts management.
D. Involve the Information Security team to understand in more detail the types of services and solutions LeadOps is proposing.
-
Question 39:
When designing a new system, which of the following is a privacy threat that the privacy technologist should consider?
A. Encryption.
B. Social distancing.
C. Social engineering.
D. Identity and Access Management.
-
Question 40:
What was the first privacy framework to be developed?
A. OECD Privacy Principles.
B. Generally Accepted Privacy Principles.
C. Code of Fair Information Practice Principles (FIPPs).
D. The Asia-Pacific Economic Cooperation (APEC) Privacy Framework.
Related Exams:
AIGP
Artificial Intelligence Governance Professional (AIGP)CIPM
Certified Information Privacy Manager (CIPM)CIPP-A
Certified Information Privacy Professional/Asia (CIPP/A)CIPP-C
Certified Information Privacy Professional/ Canada (CIPP/C)CIPP-E
Certified Information Privacy Professional/Europe (CIPP/E)CIPP-US
Certified Information Privacy Professional/United States (CIPP/US)CIPT
Certified Information Privacy Technologist (CIPT)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only IAPP exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CIPT exam preparations and IAPP certification application, do not hesitate to visit our Vcedump.com to find your solutions here.