CIPT Exam Details
-
Exam Code
:CIPT -
Exam Name
:Certified Information Privacy Technologist (CIPT) -
Certification
:IAPP Certifications -
Vendor
:IAPP -
Total Questions
:274 Q&As -
Last Updated
:May 28, 2026
IAPP CIPT Online Questions & Answers
-
Question 161:
Which of the following most embodies the principle of Data Protection by Default?
A. A messaging app for high school students that uses HTTPS to communicate with the server.
B. An electronic teddy bear with built-in voice recognition that only responds to its owner's voice.
C. An internet forum for victims of domestic violence that allows anonymous posts without registration.
D. A website that has an opt-in form for marketing emails when registering to download a whitepaper. -
Question 162:
SCENARIO
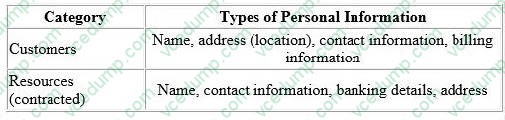
Clean-Q is a company that offers house-hold and office cleaning services. The company receives requests from consumers via their website and telephone, to book cleaning services. Based on the type and size of service, Clean-Q then contracts individuals that are registered on its resource database - currently managed in-house by Clean-Q IT Support. Because of Clean-Q's business model, resources are contracted as needed instead of permanently employed. The table below indicates some of the personal information Clean-Q requires as part of its business operations:
Clean-Q has an internal employee base of about 30 people. A recent privacy compliance exercise has been conducted to align employee data management and human resource functions with applicable data protection regulation. Therefore,
the Clean-Q permanent employee base is not included as part of this scenario.
With an increase in construction work and housing developments, Clean-Q has had an influx of requests for cleaning services. The demand has overwhelmed Clean-Q's traditional supply and demand system that has caused some
overlapping bookings.
Ina business strategy session held by senior management recently, Clear-Q invited vendors to present potential solutions to their current operational issues. These vendors included Application developers and Cloud-Q's solution providers,
presenting their proposed solutions and platforms.
The Managing Director opted to initiate the process to integrate Clean-Q's operations with a cloud solution (LeadOps) that will provide the following solution one single online platform: A web interface that Clean-Q accesses for the purposes
of resource and customer management. This would entail uploading resource and customer information.
A customer facing web interface that enables customers to register, manage and submit cleaning service requests online.
A resource facing web interface that enables resources to apply and manage their assigned jobs.
An online payment facility for customers to pay for services.
What is a key consideration for assessing external service providers like LeadOps, which will conduct personal information processing operations on Clean-Q's behalf?
A. Understanding LeadOps' costing model.
B. Establishing a relationship with the Managing Director of LeadOps.
C. Recognizing the value of LeadOps' website holding a verified security certificate.
D. Obtaining knowledge of LeadOps' information handling practices and information security environment. -
Question 163:
An organization's customers have suffered a number of data breaches through successful social engineering attacks. Which is the most effective preventative technical control to reduce the risk of future occurrences?
A. Audit and logging.
B. Training and awareness.
C. Data loss prevention (DLP).
D. Multi-factor authentication. -
Question 164:
An organization must terminate their cloud vendor agreement immediately. What is the most secure way to delete the encrypted data stored in the cloud?
A. Transfer the data to another location.
B. Invoke the appropriate deletion clause in the cloud terms and conditions.
C. Obtain a destruction certificate from the cloud vendor.
D. Destroy all encryption keys associated with the data. -
Question 165:
Which of the following is NOT relevant to a user exercising their data portability rights?
A. Notice and consent for the downloading of data.
B. Detection of phishing attacks against the portability interface.
C. Re-authentication of an account, including two-factor authentication as appropriate.
D. Validation of users with unauthenticated identifiers (e.g. IP address, physical address). -
Question 166:
All of the following topics should be included in a workplace surveillance policy EXCEPT?
A. Who can be tracked and when.
B. Who can access surveillance data.
C. What areas can be placed under surveillance.
D. Who benefits from collecting surveillance data. -
Question 167:
In order to prevent others from identifying an individual within a data set, privacy engineers use a cryptographically-secure hashing algorithm. Use of hashes in this way illustrates the privacy tactic known as what?
A. Isolation.
B. Obfuscation.
C. Perturbation.
D. Stripping. -
Question 168:
An organization is concerned that its aging IT infrastructure will lead to Increased security and privacy risks. Which of the following would help mitigate these risks?
A. Vulnerability management.
B. Data Loss Prevention.
C. Code audits.
D. Network Centricity. -
Question 169:
Which of the following would be the most appropriate solution for preventing privacy violations related to information exposure through an error message?
A. Handle exceptions internally by sending the error message to the privacy officer.
B. Create default error pages or error messages which do not include variable data
C. Log the session name and necessary parameters once the error occurs to enable troubleshooting
D. Use shorter error messages that indicate more information is available by clicking the "more information" button. -
Question 170:
What must be used in conjunction with disk encryption?
A. Increased CPU speed.
B. A strong password.
C. A digital signature.
D. Export controls.
Related Exams:
-
AIGP
Artificial Intelligence Governance Professional (AIGP) -
CIPM
Certified Information Privacy Manager (CIPM) -
CIPP-A
Certified Information Privacy Professional/Asia (CIPP/A) -
CIPP-C
Certified Information Privacy Professional/ Canada (CIPP/C) -
CIPP-E
Certified Information Privacy Professional/Europe (CIPP/E) -
CIPP-US
Certified Information Privacy Professional/United States (CIPP/US) -
CIPT
Certified Information Privacy Technologist (CIPT)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only IAPP exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CIPT exam preparations and IAPP certification application, do not hesitate to visit our Vcedump.com to find your solutions here.