CEH-001 Exam Details
-
Exam Code
:CEH-001 -
Exam Name
:Certified Ethical Hacker (CEH) -
Certification
:GAQM Certifications -
Vendor
:GAQM -
Total Questions
:878 Q&As -
Last Updated
:May 30, 2026
GAQM CEH-001 Online Questions & Answers
-
Question 771:
Which one of the following is defined as the process of distributing incorrect Internet Protocol (IP) addresses/names with the intent of diverting traffic?
A. Network aliasing
B. Domain Name Server (DNS) poisoning
C. Reverse Address Resolution Protocol (ARP)
D. Port scanning -
Question 772:
SNMP is a connectionless protocol that uses UDP instead of TCP packets (True or False)
A. true
B. false -
Question 773:
An attacker sniffs encrypted traffic from the network and is subsequently able to decrypt it. The attacker can now use which cryptanalytic technique to attempt to discover the encryption key?
A. Birthday attack
B. Plaintext attack
C. Meet in the middle attack
D. Chosen ciphertext attack -
Question 774:
If a competitor wants to cause damage to your organization, steal critical secrets, or put you out of business, they just have to find a job opening, prepare someone to pass the interview, have that person hired, and they will be in the organization.
How would you prevent such type of attacks?
A. It is impossible to block these attacks
B. Hire the people through third-party job agencies who will vet them for you
C. Conduct thorough background checks before you engage them
D. Investigate their social networking profiles -
Question 775:
Kevin sends an email invite to Chris to visit a forum for security professionals. Chris clicks on the link in the email message and is taken to a web based bulletin board. Unknown to Chris, certain functions are executed on his local system under his privileges, which allow Kevin access to information used on the BBS. However, no executables are downloaded and run on the local system. What would you term this attack?
A. Phishing
B. Denial of Service
C. Cross Site Scripting
D. Backdoor installation -
Question 776:
Least privilege is a security concept that requires that a user is
A. limited to those functions required to do the job.
B. given root or administrative privileges.
C. trusted to keep all data and access to that data under their sole control.
D. given privileges equal to everyone else in the department. -
Question 777:
Joel and her team have been going through tons of garbage, recycled paper, and other rubbish in order to find some information about the target they are attempting to penetrate. How would you call this type of activity?
A. Dumpster Diving
B. Scanning
C. CI Gathering
D. Garbage Scooping -
Question 778:
The following script shows a simple SQL injection. The script builds an SQL query by concatenating hard-coded strings together with a string entered by the user:

The user is prompted to enter the name of a city on a Web form. If she enters Chicago, the query assembled by the script looks similar to the following:
SELECT * FROM OrdersTable WHERE ShipCity = 'Chicago'
How will you delete the OrdersTable from the database using SQL Injection?
A. Chicago'; drop table OrdersTable -
B. Delete table'blah'; OrdersTable -
C. EXEC; SELECT * OrdersTable > DROP -
D. cmdshell'; 'del c:\sql\mydb\OrdersTable' // -
Question 779:
Where should a security tester be looking for information that could be used by an attacker against an organization? (Select all that apply)
A. CHAT rooms
B. WHOIS database
C. News groups
D. Web sites
E. Search engines
F. Organization's own web site -
Question 780:
The following is a sample of output from a penetration tester's machine targeting a machine with the IP address of 192.168.1.106:
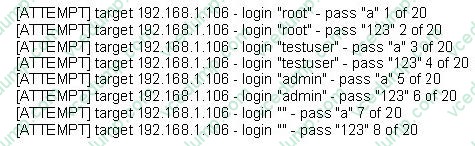
What is most likely taking place?
A. Ping sweep of the 192.168.1.106 network
B. Remote service brute force attempt
C. Port scan of 192.168.1.106
D. Denial of service attack on 192.168.1.106
Related Exams:
-
APM-001
Certified Associate in Project Management (APM) -
BMP-001
Certified Business Management Professional (BMP) -
BPM-001
Certified Business Process Manager (BPM) -
CAMT-001
IMTQN Certified Advanced Mobile Tester (CAMT) -
CBAF-001
Certified Business Analyst - Foundation -
CBCP-002
Certified Business Continuity Professional (CBCP) -
CCCP-001
Certified Cloud Computing Professional (CCCP) -
CDCP-001
Certified Data Centre Professional (CDCP) -
CEH-001
Certified Ethical Hacker (CEH) -
CFA-001
Certified Forensic Analyst (CFA)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only GAQM exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CEH-001 exam preparations and GAQM certification application, do not hesitate to visit our Vcedump.com to find your solutions here.