Exam Details
Exam Code
:JN0-541Exam Name
:IDP, Associate(JNCIA-IDP)Certification
:Juniper CertificationsVendor
:JuniperTotal Questions
:120 Q&AsLast Updated
:Aug 24, 2025
Juniper Juniper Certifications JN0-541 Questions & Answers
-
Question 111:
Which statement is true about log suppression?
A. Log suppression is not supported inNetScreen-IDP.
B. Log suppression suppresses alerting on specific logs.
C. Log suppression suppresses recurring log messages into a single log entry.
D. Log suppression preventsa IDP Sensor from sending logs to the IDP Management Server.
-
Question 112:
You have a false positive in the Log Viewer that you want to exclude from further detection. What should you do?
A. right-click on that event, selectExempt
B. go to the Exempt rules and add that Attack Object
C. right-click on that event, choose Filter - Not this Value
D. create a policy in the top of the rulebase that ignores that event and make it a Terminal rule
-
Question 113:
Which two statements about Log Viewer filters are true? (Choose two)
A. Logs can be filtered based on time.
B. Fitters once applied cannot be cleared.
C. Fitters created and saved as view are visible to all users.
D. Fitters applied to a current view are seen at the bottom of the User Interface screen.
-
Question 114:
When Address Resolution is enabled in the Log Viewer, which machine is responsible for performing the DNS Lookups?
A. IDP Sensor
B. WHOIS Servers
C. IDP User Interface
D. IDP Management Server
-
Question 115:
Which sensor utility will replay pcap files?
A. scio pcap
B. scio ccap
C. tcpdump
D. netstat
-
Question 116:
In a packet, which three must match an IDP rule before an action is performed on that packet or connection? (Choose three.)
A. service
B. source/destination address
C. terminate match
D. source/destinationnetmask
E. attack object
-
Question 117:
You have a rule in your IDP policy that detects all HTTP signatures that are targeted towards your Web server. You notice a log message is generated each time a Web user accesses the SQL database with the default passwords. Your Webmaster does not want to reprogram the Web page to use more secure SQL passwords. How do you disable alerts on this false positive?
A. Create a rule in the Exempt rule base; specify target address of your Web server; include only the specific HTTP SQL default password signature.
B. Create a rule at the top of the Exempt rule base; specify target address of your Web server; include all HTTP signatures.
C. Create a rule at the top of the IDP rule base for any traffic destined to your Web server; specify action of Exempt.
D. Create a rule at the top of the Exempt rule base; specify target address of your Web server; include all HTTP signatures; make this a terminal rule.
-
Question 118:
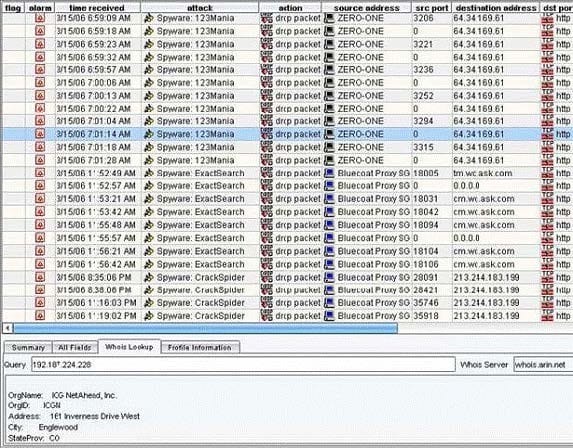
Exhibit:
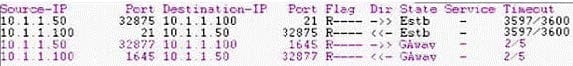
You work as an administrator at Certkiller .com. Study the exhibit carefully. In the exhibit, which sensor command would have produced this display?
A. scio subs qmodules s0
B. sctop "t" option
C. sctop "s" option
D. scio policy list s0
-
Question 119:
Which three actions should be taken on a rule in the IDP rule base when the sensor is in transparent mode? (Choose three.)
A. Drop packet.
B. Close client and server.
C. Drop connection.
D. Drop stream.
-
Question 120:
What two statements are true about the attack object database update process? (Choose two.)
A. Attack objects are downloaded from the Juniper web site over TCP port 443 and are stored on Security Manager.
B. Attack object database update can be scheduled using the commands guiSvrCli.sh and cron.
C. Attack object database update can be scheduled using the two commands idpSvrCli.sh andcron.
D. The administrator is given the choice of which static groups to update.
Related Exams:
JN0-102
Internet Associate, Junos(JNCIA-Junos)JN0-104
Junos, Associate (JNCIA-Junos)JN0-105
Junos, Associate (JNCIA-Junos)JN0-1101
Juniper Networks Certified Design Associate (JNCDA)JN0-1103
Design, Associate (JNCIA-Design)JN0-130
Juniper networks Certified internet specialist.e(jncis-e)JN0-1301
Data Center Design, Specialist (JNCDS-DC)JN0-1302
Data Center Design Specialist (JNCDS-DC)JN0-1331
Security Design, Specialist (JNCDS-SEC)JN0-1332
Security Design, Specialist (JNCDS-SEC)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Juniper exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your JN0-541 exam preparations and Juniper certification application, do not hesitate to visit our Vcedump.com to find your solutions here.