Exam Details
Exam Code
:JN0-541Exam Name
:IDP, Associate(JNCIA-IDP)Certification
:Juniper CertificationsVendor
:JuniperTotal Questions
:120 Q&AsLast Updated
:Aug 24, 2025
Juniper Juniper Certifications JN0-541 Questions & Answers
-
Question 131:
If an IDP sensor finds that a packet matchesa particular IDP rule, and then finds a matching exempt rule, what does the sensor do?
A. Creates a log entry for the matching rule, performs the action in the IDP rule, and then examines the next IDP rule in the list.
B. Does not create a log entry, does not perform the action in the matching rule, and then examines the next IDP rule in the list.
C. Creates a log entry for the matching rule, does not perform the action in the IDP rule, and then examines the next IDP rule in the list.
D. Does not create a log entry or perform the action in the matching rule, and then stops examining the remainder of the IDP rules for that particular packet.
-
Question 132:
Exhibit:
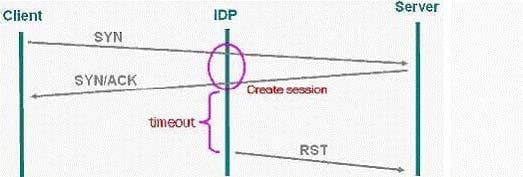
You work as an administrator at Certkiller .com. Study the exhibit carefully. In the exhibit, which SYN protector mode is the IDP using?
A. protective
B. passive
C. handshake
D. relay
-
Question 133:
You want Enterprise Security Profiler (ESP) to generate a message when a new host is detected on a network. Which two steps must you perform? (Choose two.)
A. Under the Violation Viewer tab, create a permitted object, select that object, and then click Apply.
B. Configure ESP to enable application profiling, and select the contexts to profile.
C. Start or restart the profiler process.
D. Configure ESP to enable alerts for new host detected.
-
Question 134:
Which two statements are true? (Choose two.)
A. In transparent mode, a virtual circuit maps one-to-one with a physical interface.
B. A virtual circuit is not a forwarding interface.
C. Virtual circuits on a sensor can be listed using the commandsctop vc list.
D. A virtual circuit is a communications path in and out of the sensor.
-
Question 135:
Exhibit: In order to obtain attack information so that you can create a new attack object definition, you must follow certain steps. Given the steps displayed in the exhibit, assume you have acquired a packet capture of the attack. What is the correct order for these steps?
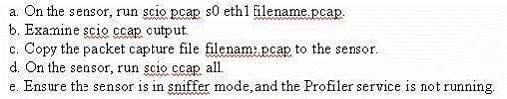
A. e, c, d, b, a
B. e, c, a, d, b
C. d, e, c, a, b
D. e, c, d, a, b
-
Question 136:
What is "a signature or protocol anomaly combined with context information"?
A. attack object
B. context
C. attack signature
D. protocol anomaly
-
Question 137:
What does the action "drop packet" instruct the sensor to do?
A. Drop the specific session containing the attack pattern.
B. Drop any packet matching this source IP, destination IP, and service.
C. Drop all packets from the attacker's IP address.
D. Drop only the specific packet matching the attack object.
-
Question 138:
What is "the location of an attack pattern protocol stream"?
A. context
B. attack signature
C. protocol anomaly
D. dynamic attack object group
-
Question 139:
Exhibit:
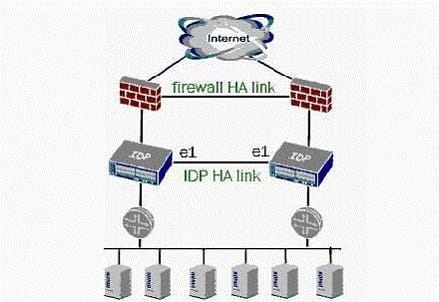
You work as an administrator at Certkiller .com. Study the exhibit carefully. In the exhibit both firewalls are active/active, which two statements are true for this scenario? (Choose two.)
A. Only one firewall is actively passing traffic.
B. Upon failure of a sensor, user traffic will be sent over the IDP HA link.
C. Routers are running a redundancy protocol.
D. Firewalls are running a redundancy protocol.
-
Question 140:
Assume that Enterprise Security Profiler (ESP) has already captured data for your network. You want to view traffic that does not match the following protocols: HTTP, HTTPS, DNS. Which steps must you perform?
A. Under the Violation Viewer tab, create a permitted object, select that object, and then click Apply.
B. Under the Violation Viewer tab, create a filter to show only tracked hosts.
C. Under the Violation Viewer tab, create a violation object, select that object, and then click Apply.
D. Under the Application View tab, create a permitted object, select that object, and then click Apply.
Related Exams:
JN0-102
Internet Associate, Junos(JNCIA-Junos)JN0-104
Junos, Associate (JNCIA-Junos)JN0-105
Junos, Associate (JNCIA-Junos)JN0-1101
Juniper Networks Certified Design Associate (JNCDA)JN0-1103
Design, Associate (JNCIA-Design)JN0-130
Juniper networks Certified internet specialist.e(jncis-e)JN0-1301
Data Center Design, Specialist (JNCDS-DC)JN0-1302
Data Center Design Specialist (JNCDS-DC)JN0-1331
Security Design, Specialist (JNCDS-SEC)JN0-1332
Security Design, Specialist (JNCDS-SEC)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Juniper exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your JN0-541 exam preparations and Juniper certification application, do not hesitate to visit our Vcedump.com to find your solutions here.