Exam Details
Exam Code
:JK0-022Exam Name
:CompTIA Security+ CertificationCertification
:CompTIA Security+Vendor
:CompTIATotal Questions
:1149 Q&AsLast Updated
:Feb 05, 2025
CompTIA CompTIA Security+ JK0-022 Questions & Answers
-
Question 291:
Which of the following wireless security measures can an attacker defeat by spoofing certain properties of their network interface card?
A. WEP
B. MAC filtering
C. Disabled SSID broadcast
D. TKIP
Correct Answer: B
MAC filtering is typically used in wireless networks. In computer networking, MAC Filtering (or GUI filtering, or layer 2 address filtering) refers to a security access control method whereby the 48-bit address assigned to each network card is used to determine access to the network. MAC addresses are uniquely assigned to each card, so using MAC filtering on a network permits and denies network access to specific devices through the use of blacklists and whitelists. While the restriction of network access through the use of lists is straightforward, an individual person is not identified by a MAC address, rather a device only, so an authorized person will need to have a whitelist entry for each device that he or she would use to access the network. While giving a wireless network some additional protection, MAC filtering can be circumvented by scanning a valid MAC (via airodumping) and then spoofing one's own MAC into a validated one.
Incorrect Answers:
A: WEP short for Wired Equivalent Privacy is a security protocol for wireless local area networks (WLANs) defined in the 802.11b standard. WEP is an encryption method to secure the connection. WEP uses a 40-bit or 104-bit encryption key that must be manually entered on wireless access points and devices. Although WEP is considered to be a weak security protocol, it is not defeated by spoofing. Therefore, this answer is incorrect.
C: Disabling SSID broadcast is a security measure that makes the wireless network invisible to computers; it will not show up in the list of available wireless networks. To connect to the wireless network, you need to know the SSID of the network and manually enter it. Spoofing is not used to circumvent this security measure. Therefore, this answer is incorrect.
D: TKIP (Temporal Key Integrity Protocol) is an encryption protocol included as part of the IEEE 802.11i standard for wireless LANs (WLANs). It was designed to provide more secure encryption than the notoriously weak Wired Equivalent Privacy (WEP), the original WLAN security protocol. TKIP is the encryption method used in Wi-Fi Protected Access (WPA), which replaced WEP in WLAN products. TKIP is not defeated by spoofing. Therefore, this answer is incorrect. References: http://en.wikipedia.org/wiki/MAC_filtering http://searchmobilecomputing.techtarget.com/definition/TKIP
-
Question 292:
Which of the following will help prevent smurf attacks?
A. Allowing necessary UDP packets in and out of the network
B. Disabling directed broadcast on border routers
C. Disabling unused services on the gateway firewall
D. Flash the BIOS with the latest firmware
Correct Answer: B
A smurf attack involves sending PING requests to a broadcast address. Therefore, we can prevent smurf attacks by blocking broadcast packets on our external routers. A smurf attack is a type of network security breach in which a network connected to the Internet is swamped with replies to ICMP echo (PING) requests. A smurf attacker sends PING requests to an Internet broadcast address. These are special addresses that broadcast all received messages to the hosts connected to the subnet. Each broadcast address can support up to 255 hosts, so a single PING request can be multiplied 255 times. The return address of the request itself is spoofed to be the address of the attacker's victim. All the hosts receiving the PING request reply to this victim's address instead of the real sender's address. A single attacker sending hundreds or thousands of these PING messages per second can fill the victim's T-1 (or even T-3) line with ping replies, bring the entire Internet service to its knees. Smurfing falls under the general category of Denial of Service attacks -- security attacks that don't try to steal information, but instead attempt to disable a computer or network.
Incorrect Answers:
A: Allowing necessary UDP packets in and out of the network would not block the broadcast packets used in a smurf attack. This answer is therefore incorrect.
C: Disabling unused services on any device is a recommended security measure. However, a smurf attack doesn't use a service that you would disable. A smurf attack uses TCP/IP networking. This answer is therefore incorrect.
D: Flashing the BIOS with the latest firmware is a good idea. Smurf attacks do not attack a firmware vulnerability though, so updating the firmware would not prevent a smurf attack. This answer is therefore incorrect.
References: http://www.webopedia.com/TERM/S/smurf.html
-
Question 293:
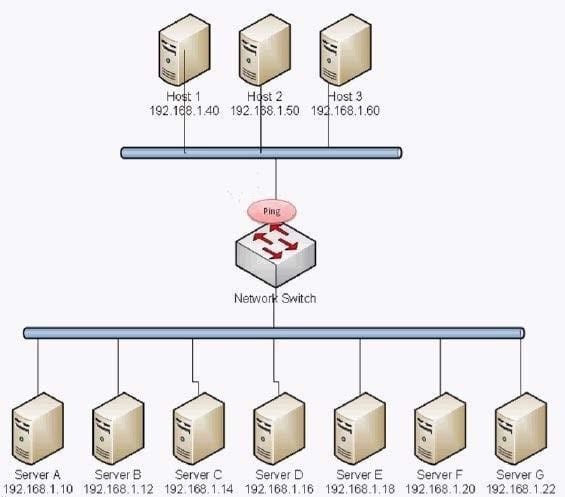
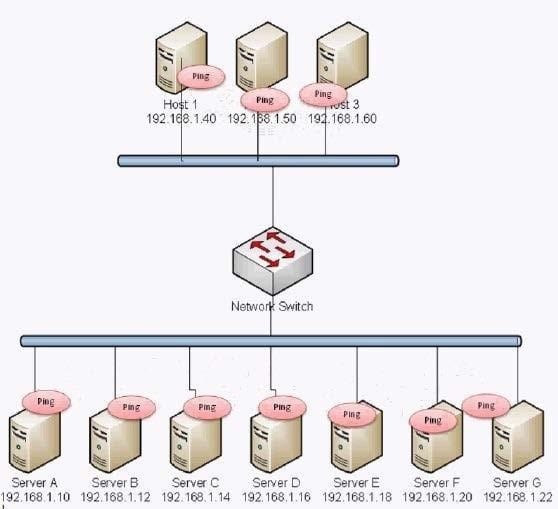
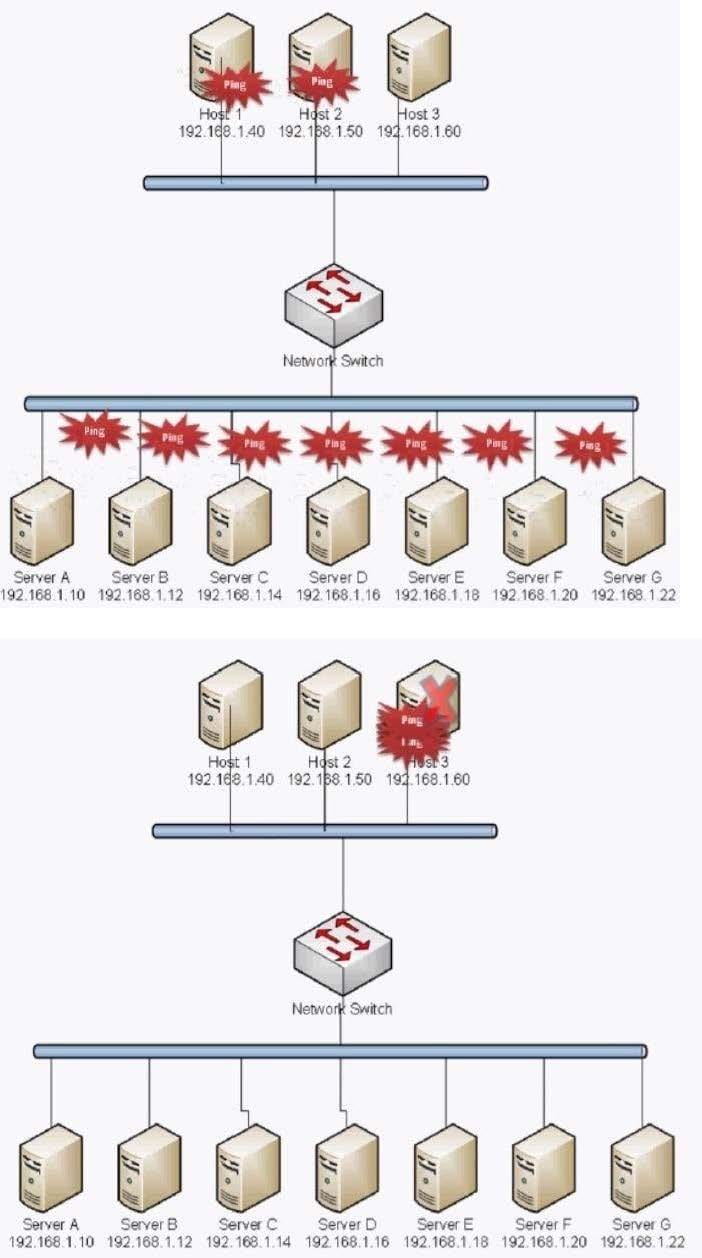
Which of the following BEST describes the type of attack that is occurring?
A. Smurf Attack
B. Man in the middle
C. Backdoor
D. Replay
E. Spear Phishing
F. Xmas Attack
G. Blue Jacking
H. Ping of Death
Correct Answer: A
The exhibit shows that all the computers on the network are being `pinged'. This indicates that the ping request was sent to the network broadcast address. We can also see that all the replies were received by one (probably with a spoofed address) host on the network. This is typical of a smurf attack.
A smurf attack is a type of network security breach in which a network connected to the Internet is swamped with replies to ICMP echo (PING) requests. A smurf attacker sends PING requests to an Internet broadcast address. These are special addresses that broadcast all received messages to the hosts connected to the subnet. Each broadcast address can support up to 255 hosts, so a single PING request can be multiplied 255 times. The return address of the request itself is spoofed to be the address of the attacker's victim. All the hosts receiving the PING request reply to this victim's address instead of the real sender's address. A single attacker sending hundreds or thousands of these PING messages per second can fill the victim's T-1 (or even T-3) line with ping replies, bring the entire Internet service to its knees. Smurfing falls under the general category of Denial of Service attacks -- security attacks that don't try to steal information, but instead attempt to disable a computer or network.
Incorrect Answers:
B: In cryptography and computer security, a man-in-the-middle attack (often abbreviated to MITM, MitM, MIM, MiM or MITMA) is an attack where the attacker secretly relays and possibly alters the communication between two parties who
believe they are directly communicating with each other. One example is active eavesdropping, in which the attacker makes independent connections with the victims and relays messages between them to make them believe they are talking
directly to each other over a private connection, when in fact the entire conversation is controlled by the attacker. The attacker must be able to intercept all relevant messages passing between the two victims and inject new ones. This is
straightforward in many circumstances; for example, an attacker within reception range of an unencrypted Wi-Fi wireless access point, can insert himself as a man-in-the-middle. This is not the attack illustrated in this question. Therefore, this
answer is incorrect.
C: A backdoor in a computer system (or cryptosystem or algorithm) is a method of bypassing normal authentication, securing unauthorized remote access to a computer, obtaining access to plaintext, and so on, while attempting to remain
undetected. The backdoor may take the form of an installed program (e.g., Back Orifice) or may subvert the system through a rootkit. This is not the attack illustrated in this question. Therefore, this answer is incorrect.
D: A replay attack (also known as playback attack) is a form of network attack in which a valid data transmission is maliciously or fraudulently repeated or delayed. This is carried out either by the originator or by an adversary who intercepts
the data and retransmits it, possibly as part of a masquerade attack by IP packet substitution (such as stream cipher attack). For example: Suppose Alice wants to prove her identity to Bob. Bob requests her password as proof of identity,
which Alice dutifully provides (possibly after some transformation like a hash function); meanwhile, Eve is eavesdropping on the conversation and keeps the password (or the hash). After the interchange is over, Eve (posing as Alice) connects
to Bob; when asked for a proof of identity, Eve sends Alice's password (or hash) read from the last session, which Bob accepts thus granting access to Eve. This is not the attack illustrated in this question. Therefore, this answer is incorrect.
E: Spear phishing is an e-mail spoofing fraud attempt that targets a specific organization, seeking unauthorized access to confidential data. As with the e-mail messages used in regular phishing expeditions, spear phishing messages appear
to come from a trusted source. Phishing messages usually appear to come from a large and well-known company or Web site with a broad membership base, such as eBay or PayPal. In the case of spear phishing, however, the apparent
source of the e-mail is likely to be an individual within the recipient's own company and generally someone in a position of authority. This is not the attack illustrated in this question.
Therefore, this answer is incorrect.
F: In information technology, a Christmas tree packet is a packet with every single option set for whatever protocol is in use. The term derives from a fanciful image of each little option bit in a header being represented by a different-colored
light bulb, all turned on, as in, "the packet was lit up like a Christmas tree." It can also be known as a kamikaze packet, nastygram or a lamp test segment.
Christmas tree packets can be used as a method of divining the underlying nature of a TCP/IP stack by sending the packets and awaiting and analyzing the responses. When used as part of scanning a system, the TCP header of a Christmas
tree packets has the flags SYN, FIN, URG and PSH set. Many operating systems implement their compliance with the Internet Protocol standard (RFC 791) in varying or incomplete ways. By observing how a host responds to an odd packet,
such as a Christmas tree packet, assumptions can be made regarding the host's operating system. Versions of Microsoft Windows, BSD/OS, HP-UX, Cisco IOS, MVS, and IRIX display behaviors that differ from the RFC standard when
queried with said packets. A large number of Christmas tree packets can also be used to conduct a DoS attack by exploiting the fact that Christmas tree packets require much more processing by routers and end-hosts than the 'usual' packets
do.
Christmas tree packets can be easily detected by intrusion-detection systems or more advanced firewalls. From a network security point of view, Christmas tree packets are always suspicious and indicate a high probability of network
reconnaissance activities. This is not the attack illustrated in this question. Therefore, this answer is incorrect.
G: Bluejacking is the sending of unsolicited messages over Bluetooth to Bluetooth-enabled devices such as mobile phones, PDAs or laptop computers, sending a vCard which typically contains a message in the name field (i.e., for bluedating or bluechat) to another Bluetooth- enabled device via the OBEX protocol. Bluetooth has a very limited range, usually around 10 metres (32.8 ft) on mobile phones, but laptops can reach up to 100 metres (328 ft) with powerful (Class 1) transmitters. Bluejacking is usually harmless, but because bluejacked people generally don't know what has happened, they may think that their phone is malfunctioning. Usually, a bluejacker will only send a text message, but with modern phones it's possible to send images or sounds as well. Bluejacking has been used in guerrilla marketing campaigns to promote advergames. This is not the attack illustrated in this question. Therefore, this answer is incorrect.
H: A ping of death is a type of attack on a computer that involves sending a malformed or otherwise malicious ping to a computer. A correctly formed ping message is typically 56 bytes in size, or 84 bytes when the Internet Protocol [IP] header is considered. Historically, many computer systems could not properly handle a ping packet larger than the maximum IPv4 packet size of 65535bytes. Larger packets could crash the target computer. In early implementations of TCP/IP, this bug was easy to exploit. This exploit affected a wide variety of systems, including Unix, Linux, Mac, Windows, printers, and routers. Generally, sending a 65,536-byte ping packet violates the Internet Protocol as documented in RFC 791, but a packet of such a size can be sent if it is fragmented; when the target computer reassembles the packet, a buffer overflow can occur, which often causes a system crash. Later a different kind of ping attack became widespread--ping flooding simply floods the victim with so much ping traffic that normal traffic fails to reach the system, a basic denial-of-service attack. The exhibit shows that all the computers on the network are being `pinged'. This indicates that the ping request was sent to the network broadcast address. This is more typical of a smurf attack than a ping of death attack. Therefore, this answer is incorrect.
References: http://www.webopedia.com/TERM/S/smurf.html http://en.wikipedia.org/wiki/Man-in-the-middle_attack http://en.wikipedia.org/wiki/Backdoor_%28computing%29 http://en.wikipedia.org/wiki/Replay_attack http://searchsecurity.techtarget.com/definition/spear-phishing http://en.wikipedia.org/wiki/Christmas_tree_packet http://en.wikipedia.org/wiki/Bluejacking http://en.wikipedia.org/wiki/Ping_of_death
-
Question 294:
Timestamps and sequence numbers act as countermeasures against which of the following types of attacks?
A. Smurf
B. DoS
C. Vishing
D. Replay
Correct Answer: D
A replay attack (also known as playback attack) is a form of network attack in which a valid data transmission is maliciously or fraudulently repeated or delayed. This is carried out either by the originator or by an adversary who intercepts the data and retransmits it, possibly as part of a masquerade attack by IP packet substitution (such as stream cipher attack).
For example: Suppose Alice wants to prove her identity to Bob. Bob requests her password as proof of identity, which Alice dutifully provides (possibly after some transformation like a hash function); meanwhile, Eve is eavesdropping on the conversation and keeps the password (or the hash). After the interchange is over, Eve (posing as Alice) connects to Bob; when asked for a proof of identity, Eve sends Alice's password (or hash) read from the last session, which Bob accepts thus granting access to Eve.
Countermeasures: A way to avoid replay attacks is by using session tokens: Bob sends a one- time token to Alice, which Alice uses to transform the password and send the result to Bob (e.g. computing a hash function of the session token appended to the password). On his side Bob performs the same computation; if and only if both values match, the login is successful. Now suppose Eve has captured this value and tries to use it on another session; Bob sends a different session token, and when Eve replies with the captured value it will be different from Bob's computation. Session tokens should be chosen by a (pseudo-) random process. Otherwise Eve may be able to pose as Bob, presenting some predicted future token, and convince Alice to use that token in her transformation. Eve can then replay her reply at a later time (when the previously predicted token is actually presented by Bob), and Bob will accept the authentication. Onetime passwords are similar to session tokens in that the password expires after it has been used or after a very short amount of time. They can be used to authenticate individual transactions in addition to sessions. The technique has been widely implemented in personal online banking systems. Bob can also send nonces but should then include a message authentication code (MAC), which Alice should check. Timestamping is another way of preventing a replay attack. Synchronization should be achieved using a secure protocol. For example Bob periodically broadcasts the time on his clock together with a MAC. When Alice wants to send Bob a message, she includes her best estimate of the time on his clock in her message, which is also authenticated. Bob only accepts messages for which the timestamp is within a reasonable tolerance. The advantage of this scheme is that Bob does not need to generate (pseudo-) random numbers, with the trade-off being that replay attacks, if they are performed quickly enough i.e. within that 'reasonable' limit, could succeed.
Incorrect Answers:
A: A smurf attack is a type of network security breach in which a network connected to the Internet is swamped with replies to ICMP echo (PING) requests. A smurf attacker sends PING requests to an Internet broadcast address. These are special addresses that broadcast all received messages to the hosts connected to the subnet. Each broadcast address can support up to 255 hosts, so a single PING request can be multiplied 255 times. The return address of the request itself is spoofed to be the address of the attacker's victim. All the hosts receiving the PING request reply to this victim's address instead of the real sender's address. A single attacker sending hundreds or thousands of these PING messages per second can fill the victim's T-1 (or even T-3) line with ping replies, bring the entire Internet service to its knees. Smurfing falls under the general category of Denial of Service attacks -- security attacks that don't try to steal information, but instead attempt to disable a computer or network. Timestamps are not used to defend against this type of attack. Therefore, this answer is incorrect.
B: DoS, short for denial-of-service attack, a type of attack on a network that is designed to bring the network to its knees by flooding it with useless traffic. Many DoS attacks, such as the Ping of Death and Teardrop attacks, exploit limitations in the TCP/IP protocols. For all known DoS attacks, there are software fixes that system administrators can install to limit the damage caused by the attacks. But, like viruses, new DoS attacks are constantly being dreamed up by hackers. Timestamps are not used to defend against this type of attack. Therefore, this answer is incorrect.
C: Vishing is the telephone equivalent of phishing. Vishing is the act of using the telephone in an attempt to scam the user into surrendering private information that will be used for identity theft. The scammer usually pretends to be a legitimate business, and fools the victim into thinking he or she will profit. Timestamps are not used to defend against this type of attack. Therefore, this answer is incorrect. References: http://en.wikipedia.org/wiki/Replay_attack http://www.webopedia.com/TERM/S/smurf.html http://www.webopedia.com/TERM/D/DoS_attack.html http://www.webopedia.com/TERM/V/vishing.html
-
Question 295:
A network analyst received a number of reports that impersonation was taking place on the network. Session tokens were deployed to mitigate this issue and defend against which of the following attacks?
A. Replay
B. DDoS
C. Smurf
D. Ping of Death
Correct Answer: A
A replay attack (also known as playback attack) is a form of network attack in which a valid data transmission is maliciously or fraudulently repeated or delayed. This is carried out either by the originator or by an adversary who intercepts the data and retransmits it, possibly as part of a masquerade attack by IP packet substitution (such as stream cipher attack).
For example: Suppose Alice wants to prove her identity to Bob. Bob requests her password as proof of identity, which Alice dutifully provides (possibly after some transformation like a hash function); meanwhile, Eve is eavesdropping on the conversation and keeps the password (or the hash). After the interchange is over, Eve (posing as Alice) connects to Bob; when asked for a proof of identity, Eve sends Alice's password (or hash) read from the last session, which Bob accepts thus granting access to Eve.
Countermeasures: A way to avoid replay attacks is by using session tokens: Bob sends a one- time token to Alice, which Alice uses to transform the password and send the result to Bob (e.g. computing a hash function of the session token appended to the password). On his side Bob performs the same computation; if and only if both values match, the login is successful. Now suppose Eve has captured this value and tries to use it on another session; Bob sends a different session token, and when Eve replies with the captured value it will be different from Bob's computation. Session tokens should be chosen by a (pseudo-) random process. Otherwise Eve may be able to pose as Bob, presenting some predicted future token, and convince Alice to use that token in her transformation. Eve can then replay her reply at a later time (when the previously predicted token is actually presented by Bob), and Bob will accept the authentication. Onetime passwords are similar to session tokens in that the password expires after it has been used or after a very short amount of time. They can be used to authenticate individual transactions in addition to sessions. The technique has been widely implemented in personal online banking systems. Bob can also send nonces but should then include a message authentication code (MAC), which Alice should check. Timestamping is another way of preventing a replay attack. Synchronization should be achieved using a secure protocol. For example Bob periodically broadcasts the time on his clock together with a MAC. When Alice wants to send Bob a message, she includes her best estimate of the time on his clock in her message, which is also authenticated. Bob only accepts messages for which the timestamp is within a reasonable tolerance. The advantage of this scheme is that Bob does not need to generate (pseudo-) random numbers, with the trade-off being that replay attacks, if they are performed quickly enough i.e. within that 'reasonable' limit, could succeed.
Incorrect Answers:
B: A Distributed Denial of Service (DDoS) attack is an attack from several different computers targeting a single computer. One common method of attack involves saturating the target machine with external communications requests, so much so that it cannot respond to legitimate traffic, or responds so slowly as to be rendered essentially unavailable. Such attacks usually lead to a server overload.
A distributed denial-of-service (DDoS) attack occurs when multiple systems flood the bandwidth or resources of a targeted system, usually one or more web servers. Such an attack is often the result of multiple compromised systems (for example a botnet) flooding the targeted system with traffic. When a server is overloaded with connections, new connections can no longer be accepted. Session tokens are not used to defend against this type of attack. Therefore, this answer is incorrect.
C: A smurf attack is a type of network security breach in which a network connected to the Internet is swamped with replies to ICMP echo (PING) requests. A smurf attacker sends PING requests to an Internet broadcast address. These are special addresses that broadcast all received messages to the hosts connected to the subnet. Each broadcast address can support up to 255 hosts, so a single PING request can be multiplied 255 times. The return address of the request itself is spoofed to be the address of the attacker's victim. All the hosts receiving the PING request reply to this victim's address instead of the real sender's address. A single attacker sending hundreds or thousands of these PING messages per second can fill the victim's T-1 (or even T-3) line with ping replies, bring the entire Internet service to its knees. Smurfing falls under the general category of Denial of Service attacks -- security attacks that don't try to steal information, but instead attempt to disable a computer or network. Session tokens are not used to defend against this type of attack. Therefore, this answer is incorrect.
D: A ping of death is a type of attack on a computer that involves sending a malformed or otherwise malicious ping to a computer. A correctly formed ping message is typically 56 bytes in size, or 84 bytes when the Internet Protocol [IP] header is considered. Historically, many computer systems could not properly handle a ping packet larger than the maximum IPv4 packet size of 65535bytes. Larger packets could crash the target computer. In early implementations of TCP/IP, this bug was easy to exploit. This exploit affected a wide variety of systems, including Unix, Linux, Mac, Windows, printers, and routers. Generally, sending a 65,536-byte ping packet violates the Internet Protocol as documented in RFC 791, but a packet of such a size can be sent if it is fragmented; when the target computer reassembles the packet, a buffer overflow can occur, which often causes a system crash. Later a different kind of ping attack became widespread--ping flooding simply floods the victim with so much ping traffic that normal traffic fails to reach the system, a basic denial-of-service attack. Session tokens are not used to defend against this type of attack. Therefore, this answer is incorrect. References: http://en.wikipedia.org/wiki/Replay_attack http://www.webopedia.com/TERM/S/smurf.html http://en.wikipedia.org/wiki/Ping_of_death
-
Question 296:
Which of the following attacks could be used to initiate a subsequent man-in-the-middle attack?
A. ARP poisoning
B. DoS
C. Replay
D. Brute force
Correct Answer: C
A replay attack (also known as playback attack) is a form of network attack in which a valid data transmission is maliciously or fraudulently repeated or delayed. This is carried out either by the originator or by an adversary who intercepts the data and retransmits it, possibly as part of a masquerade attack by IP packet substitution (such as stream cipher attack).
For example: Suppose Alice wants to prove her identity to Bob. Bob requests her password as proof of identity, which Alice dutifully provides (possibly after some transformation like a hash function); meanwhile, Eve is eavesdropping on the conversation and keeps the password (or the hash). After the interchange is over, Eve (posing as Alice) connects to Bob; when asked for a proof of identity, Eve sends Alice's password (or hash) read from the last session, which Bob accepts thus granting access to Eve.
Countermeasures: A way to avoid replay attacks is by using session tokens: Bob sends a one- time token to Alice, which Alice uses to transform the password and send the result to Bob (e.g. computing a hash function of the session token appended to the password). On his side Bob performs the same computation; if and only if both values match, the login is successful. Now suppose Eve has captured this value and tries to use it on another session; Bob sends a different session token, and when Eve replies with the captured value it will be different from Bob's computation. Session tokens should be chosen by a (pseudo-) random process. Otherwise Eve may be able to pose as Bob, presenting some predicted future token, and convince Alice to use that token in her transformation. Eve can then replay her reply at a later time (when the previously predicted token is actually presented by Bob), and Bob will accept the authentication. Onetime passwords are similar to session tokens in that the password expires after it has been used or after a very short amount of time. They can be used to authenticate individual transactions in addition to sessions. The technique has been widely implemented in personal online banking systems. Bob can also send nonces but should then include a message authentication code (MAC), which Alice should check. Timestamping is another way of preventing a replay attack. Synchronization should be achieved using a secure protocol. For example Bob periodically broadcasts the time on his clock together with a MAC. When Alice wants to send Bob a message, she includes her best estimate of the time on his clock in her message, which is also authenticated. Bob only accepts messages for which the timestamp is within a reasonable tolerance. The advantage of this scheme is that Bob does not need to generate (pseudo-) random numbers, with the trade-off being that replay attacks, if they are performed quickly enough i.e. within that 'reasonable' limit, could succeed.
Incorrect Answers:
A: Address Resolution Protocol poisoning (ARP poisoning) is a form of attack in which an attacker changes the Media Access Control (MAC) address and attacks an Ethernet LAN by changing the target computer's ARP cache with a forged
ARP request and reply packets. This modifies the layer -Ethernet MAC address into the hacker's known MAC address to monitor it. Because the ARP replies are forged, the target computer unintentionally sends the frames to the hacker's
computer first instead of sending it to the original destination. As a result, both the user's data and privacy are compromised. An effective ARP poisoning attempt is undetectable to the user.
ARP poisoning is also known as ARP cache poisoning or ARP poison routing (APR). ARP poisoning would not be used to initiate a subsequent man-in-the-middle attack. Therefore, this answer is incorrect.
B: DoS, short for denial-of-service attack, a type of attack on a network that is designed to bring the network to its knees by flooding it with useless traffic. Many DoS attacks, such as the Ping of Death and Teardrop attacks, exploit limitations
in the TCP/IP protocols. For all known DoS attacks, there are software fixes that system administrators can install to limit the damage caused by the attacks. But, like viruses, new DoS attacks are constantly being dreamed up by hackers.
DoS would not be used to initiate a subsequent man-in-the-middle attack. Therefore, this answer is incorrect.
D: A brute force attack is a trial-and-error method used to obtain information such as a user password or personal identification number (PIN). In a brute force attack, automated software is used to generate a large number of consecutive
guesses as to the value of the desired data. Brute force attacks may be used by criminals to crack encrypted data, or by security analysts to test an organization's network security. A brute force attack may also be referred to as brute force
cracking. For example, a form of brute force attack known as a dictionary attack might try all the words in a dictionary. Other forms of brute force attack might try commonly-used passwords or combinations of letters and numbers. An attack of
this nature can be time- and resource-consuming. Hence the name "brute force attack;" success is usually based on computing power and the number of combinations tried rather than an ingenious algorithm. A brute force attack would not be
used to initiate a subsequent man-in-the-middle attack.
Therefore, this answer is incorrect.
References: http://en.wikipedia.org/wiki/Replay_attack http://www.techopedia.com/definition/27471/address-resolution-protocol-poisoning-arp- poisoning http://www.webopedia.com/TERM/D/DoS_attack.html http://www.techopedia.com/definition/18091/brute-force-attack
-
Question 297:
An administrator is assigned to monitor servers in a data center. A web server connected to the Internet suddenly experiences a large spike in CPU activity. Which of the following is the MOST likely cause?
A. Spyware
B. Trojan
C. Privilege escalation
D. DoS
Correct Answer: D
A Distributed Denial of Service (DDoS) attack is a DoS attack from multiple computers whereas a DoS attack is from a single computer. In terms of the actual method of attack, DDoS and DoS attacks are the same.
One common method of attack involves saturating the target machine with external communications requests, so much so that it cannot respond to legitimate traffic, or responds so slowly as to be rendered essentially unavailable. Such
attacks usually lead to a server overload. A distributed denial-of-service (DDoS) attack occurs when multiple systems flood the bandwidth or resources of a targeted system, usually one or more web servers. Such an attack is often the result
of multiple compromised systems (for example a botnet) flooding the targeted system with traffic. When a server is overloaded with connections, new connections can no longer be accepted. The major advantages to an attacker of using a
distributed denial-of-service attack are that multiple machines can generate more attack traffic than one machine, multiple attack machines are harder to turn off than one attack machine, and that the behavior of each attack machine can be
stealthier, making it harder to track and shut down. These attacker advantages cause challenges for defense mechanisms. For example, merely purchasing more incoming bandwidth than the current volume of the attack might not help,
because the attacker might be able to simply add more attack machines. This after all will end up completely crashing a website for periods of time.
Malware can carry DDoS attack mechanisms; one of the better-known examples of this was MyDoom. Its DoS mechanism was triggered on a specific date and time. This type of DDoS involved hardcoding the target IP address prior to
release of the malware and no further interaction was necessary to launch the attack.
Incorrect Answers:
A: Spyware is software that aids in gathering information about a person or organization without their knowledge and that may send such information to another entity without the consumer's consent, or that asserts control over a computer without the consumer's knowledge. "Spyware" is mostly classified into four types: system monitors, trojans, adware, and tracking cookies. Spyware is mostly used for the purposes of tracking and storing Internet users' movements on the Web and serving up pop-up ads to Internet users. Whenever spyware is used for malicious purposes, its presence is typically hidden from the user and can be difficult to detect. Some spyware, such as keyloggers, may be installed by the owner of a shared, corporate, or public computer intentionally in order to monitor users. It's more likely that a DoS attack would cause a spike in CPU activity. Therefore, this answer is incorrect.
B: A Trojan horse is a program in which malicious or harmful code is contained inside apparently harmless programming or data in such a way that it can get control and do its chosen form of damage, such as ruining the file allocation table on your hard disk. In one celebrated case, a Trojan horse was a program that was supposed to find and destroy computer viruses. A Trojan horse may be widely redistributed as part of a computer virus. It's more likely that a DoS attack would cause a spike in CPU activity. Therefore, this answer is incorrect.
C: Privilege escalation is the act of exploiting a bug, design flaw or configuration oversight in an operating system or software application to gain elevated access to resources that are normally protected from an application or user. Privilege escalation would not cause a spike in CPU activity. Therefore, this answer is incorrect.
References: http://en.wikipedia.org/wiki/Denial-of-service_attack http://en.wikipedia.org/wiki/Spyware http://searchsecurity.techtarget.com/definition/Trojan-horse
-
Question 298:
A security technician at a small business is worried about the Layer 2 switches in the network suffering from a DoS style attack caused by staff incorrectly cabling network connections between switches.
Which of the following will BEST mitigate the risk if implemented on the switches?
A. Spanning tree
B. Flood guards
C. Access control lists
D. Syn flood
Correct Answer: A
Spanning Tree is designed to eliminate network `loops' from incorrect cabling between switches. Imagine two switches named switch 1 and switch 2 with two network cables connecting the switches. This would cause a network loop. A network loop between two switches can cause a `broadcast storm' where a broadcast packet is sent out of all ports on switch 1 which includes two links to switch 2. The broadcast packet is then sent out of all ports on switch 2 which includes links back to switch 1. The broadcast packet will be sent out of all ports on switch 1 again which includes two links to switch 2 and so on thus flooding the network with broadcast traffic. The Spanning-Tree Protocol (STP) was created to overcome the problems of transparent bridging in redundant networks. The purpose of STP is to avoid and eliminate loops in the network by negotiating a loop-free path through a root bridge. This is done by determining where there are loops in the network and blocking links that are redundant. Spanning-Tree Protocol executes an algorithm called the Spanning-Tree Algorithm (STA). In order to find redundant links, STA will choose a reference point called a Root Bridge, and then determines all the available paths to that reference point. If it finds a redundant path, it chooses for the best path to forward and for all other redundant paths to block. This effectively severs the redundant links within the network. All switches participating in STP gather information on other switches in the network through an exchange of data messages. These messages are referred to as Bridge Protocol Data Units (BPDUs). The exchange of BPDUs in a switched environment will result in the election of a root switch for the stable spanning-tree network topology, election of designated switch for every switched segment, and the removal of loops in the switched network by placing redundant switch ports in a backup state.
Incorrect Answers:
B: Flood guards are used to prevent network flooding attacks such as DoS, SYN floods, ping floods etc. However, this question states that a security technician at a small business is worried about the Layer 2 switches in the network suffering from a DoS style attack caused by staff incorrectly cabling network connections between switches. Spanning tree is a more appropriate answer is this scenario. Therefore, this answer is incorrect.
C: Access control lists would not prevent a DoS style attack caused by staff incorrectly cabling network connections between switches. Switch traffic is not allowed or disallowed using Access control lists. Therefore, this answer is incorrect.
D: A SYN flood is a form of denial-of-service attack in which an attacker sends a succession of SYN requests to a target's system in an attempt to consume enough server resources to make the system unresponsive to legitimate traffic. It is not used to prevent a DoS style attack caused by staff incorrectly cabling network connections between switches. Therefore, this answer is incorrect.
References:
http://www.symantec.com/business/support/index?page=contentandid=HOWTO6019 https://www.google.co.uk/webhp?sourceid=chrome- instantandion=1andespv=2andie=UTF-8#q=syn %20flood
-
Question 299:
An administrator notices an unusual spike in network traffic from many sources. The administrator suspects that:
A. it is being caused by the presence of a rogue access point.
B. it is the beginning of a DDoS attack.
C. the IDS has been compromised.
D. the internal DNS tables have been poisoned.
Correct Answer: B
A Distributed Denial of Service (DDoS) attack is an attack from several different computers targeting a single computer. One common method of attack involves saturating the target machine with external communications requests, so much so that it cannot respond to legitimate traffic, or responds so slowly as to be rendered essentially unavailable. Such attacks usually lead to a server overload.
A distributed denial-of-service (DDoS) attack occurs when multiple systems flood the bandwidth or resources of a targeted system, usually one or more web servers. Such an attack is often the result of multiple compromised systems (for example a botnet) flooding the targeted system with traffic. When a server is overloaded with connections, new connections can no longer be accepted. The major advantages to an attacker of using a distributed denial-of-service attack are that multiple machines can generate more attack traffic than one machine, multiple attack machines are harder to turn off than one attack machine, and that the behavior of each attack machine can be stealthier, making it harder to track and shut down. These attacker advantages cause challenges for defense mechanisms. For example, merely purchasing more incoming bandwidth than the current volume of the attack might not help, because the attacker might be able to simply add more attack machines. This after all will end up completely crashing a website for periods of time. Malware can carry DDoS attack mechanisms; one of the better-known examples of this was MyDoom. Its DoS mechanism was triggered on a specific date and time. This type of DDoS involved hardcoding the target IP address prior to release of the malware and no further interaction was necessary to launch the attack.
Incorrect Answers:
A: A rogue access point would not cause a spike in network traffic from many sources unless many computers had connected to the rogue access point and started sending lots of traffic. Therefore, this answer is incorrect.
C: The question states that an administrator notices an unusual spike in network traffic from many sources. You would typically notice this on a firewall or an IDS system. It's unlikely the IDS has been compromised. A DDoS attack is far more common. Therefore, this answer is incorrect.
D: DNS poisoning is the process of inserting incorrect information into DNS records. This may cause a slight increase in broadcast traffic on the network (as computers try to locate each other) but it would not cause a serious spike in network traffic. Therefore, this answer is incorrect.
References: http://en.wikipedia.org/wiki/Denial-of-service_attack
-
Question 300:
A distributed denial of service attack can BEST be described as:
A. Invalid characters being entered into a field in a database application.
B. Users attempting to input random or invalid data into fields within a web browser application.
C. Multiple computers attacking a single target in an organized attempt to deplete its resources.
D. Multiple attackers attempting to gain elevated privileges on a target system.
Correct Answer: C
A Distributed Denial of Service (DDoS) attack is an attack from several different computers targeting a single computer. One common method of attack involves saturating the target machine with external communications requests, so much so that it cannot respond to legitimate traffic, or responds so slowly as to be rendered essentially unavailable. Such attacks usually lead to a server overload.
A distributed denial-of-service (DDoS) attack occurs when multiple systems flood the bandwidth or resources of a targeted system, usually one or more web servers. Such an attack is often the result of multiple compromised systems (for example a botnet) flooding the targeted system with traffic. When a server is overloaded with connections, new connections can no longer be accepted. The major advantages to an attacker of using a distributed denial-of-service attack are that multiple machines can generate more attack traffic than one machine, multiple attack machines are harder to turn off than one attack machine, and that the behavior of each attack machine can be stealthier, making it harder to track and shut down. These attacker advantages cause challenges for defense mechanisms. For example, merely purchasing more incoming bandwidth than the current volume of the attack might not help, because the attacker might be able to simply add more attack machines. This after all will end up completely crashing a website for periods of time. Malware can carry DDoS attack mechanisms; one of the better-known examples of this was MyDoom. Its DoS mechanism was triggered on a specific date and time. This type of DDoS involved hardcoding the target IP address prior to release of the malware and no further interaction was necessary to launch the attack.
Incorrect Answers:
A: Invalid characters being entered into a field in a database application does not describe a DDoS attack. Therefore, this answer is incorrect.
B: Users attempting to input random or invalid data into fields within a web browser application does not describe a DDoS attack. Therefore, this answer is incorrect.
D: Multiple attackers attempting to gain elevated privileges on a target system does not describe a DDoS attack. In "distributed denial-of-service", distributed means multiple computers, not multiple attackers. Therefore, this answer is
incorrect.
References:
http://en.wikipedia.org/wiki/Denial-of-service_attack
Related Exams:
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your JK0-022 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.