Exam Details
Exam Code
:312-50V7Exam Name
:Ethical Hacking and Countermeasures (CEHv7)Certification
:Certified Ethical HackerVendor
:EC-COUNCILTotal Questions
:514 Q&AsLast Updated
:May 28, 2025
EC-COUNCIL Certified Ethical Hacker 312-50V7 Questions & Answers
-
Question 461:
Shayla is an IT security consultant, specializing in social engineering and external penetration tests. Shayla has been hired on by Treks Avionics, a subcontractor for the Department of Defense. Shayla has been given authority to perform any and all tests necessary to audit the company's network security.
No employees for the company, other than the IT director, know about Shayla's work she will be doing. Shayla's first step is to obtain a list of employees through company website contact pages. Then she befriends a female employee of the company through an online chat website. After meeting with the female employee numerous times, Shayla is able to gain her trust and they become friends. One day, Shayla steals the employee's access badge and uses it to gain unauthorized access to the Treks Avionics offices.
What type of insider threat would Shayla be considered?
A. She would be considered an Insider Affiliate
B. Because she does not have any legal access herself, Shayla would be considered an Outside Affiliate
C. Shayla is an Insider Associate since she has befriended an actual employee
D. Since Shayla obtained access with a legitimate company badge; she would be considered a Pure Insider
-
Question 462:
Which type of hacker represents the highest risk to your network?
A. black hat hackers
B. grey hat hackers
C. disgruntled employees
D. script kiddies
-
Question 463:
In the context of Trojans, what is the definition of a Wrapper?
A. An encryption tool to protect the Trojan
B. A tool used to bind the Trojan with a legitimate file
C. A tool used to calculate bandwidth and CPU cycles wasted by the Trojan
D. A tool used to encapsulate packets within a new header and footer
-
Question 464:
Your computer is infected by E-mail tracking and spying Trojan. This Trojan infects the computer with a single file - emos.sys
Which step would you perform to detect this type of Trojan?
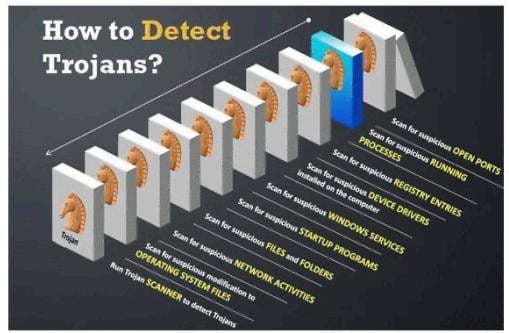
A. Scan for suspicious startup programs using msconfig
B. Scan for suspicious network activities using Wireshark
C. Scan for suspicious device drivers in c:\windows\system32\drivers
D. Scan for suspicious open ports using netstat
-
Question 465:
You just purchased the latest DELL computer, which comes pre-installed with Windows 7, McAfee antivirus software and a host of other applications. You want to connect Ethernet wire to your cable modem and start using the computer immediately. Windows is dangerously insecure when unpacked from the box, and there are a few things that you must do before you use it.
A. New installation of Windows should be patched by installing the latest service packs and hotfixes
B. Key applications such as Adobe Acrobat, Macromedia Flash, Java, Winzip etc., must have the latest security patches installed
C. Install a personal firewall and lock down unused ports from connecting to your computer
D. Install the latest signatures for Antivirus software
E. Configure "Windows Update" to automatic
F. Create a non-admin user with a complex password and logon to this account
G. You can start using your computer as vendors such as DELL, HP and IBM would have already installed the latest service packs.
-
Question 466:
You want to hide a secret.txt document inside c:\windows\system32\tcpip.dll kernel library using ADS streams. How will you accomplish this?
A. copy secret.txt c:\windows\system32\tcpip.dll kernel>secret.txt
B. copy secret.txt c:\windows\system32\tcpip.dll:secret.txt
C. copy secret.txt c:\windows\system32\tcpip.dll |secret.txt
D. copy secret.txt >< c:\windows\system32\tcpip.dll kernel secret.txt
-
Question 467:
In which part of OSI layer, ARP Poisoning occurs?
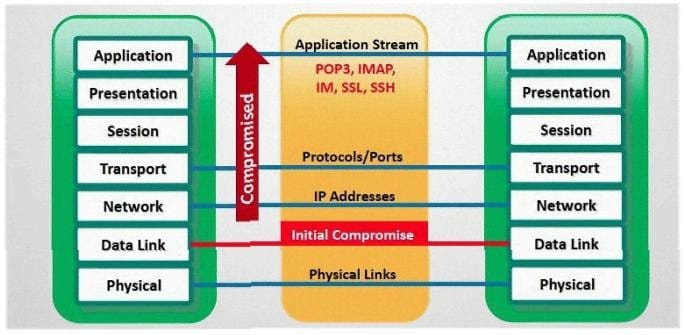
A. Transport Layer
B. Datalink Layer
C. Physical Layer
D. Application layer
-
Question 468:
SNMP is a connectionless protocol that uses UDP instead of TCP packets (True or False)
A. true
B. false
-
Question 469:
TCP/IP Session Hijacking is carried out in which OSI layer?
A. Datalink layer
B. Transport layer
C. Network layer
D. Physical layer
-
Question 470:
What is the correct command to run Netcat on a server using port 56 that spawns command shell when connected?
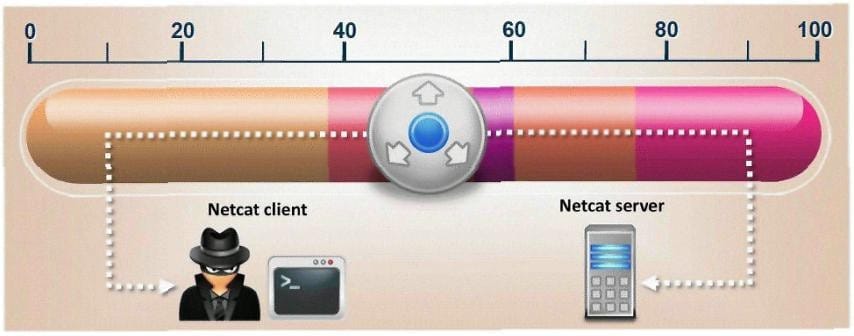
A. nc -port 56 -s cmd.exe
B. nc -p 56 -p -e shell.exe
C. nc -r 56 -c cmd.exe
D. nc -L 56 -t -e cmd.exe
Related Exams:
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only EC-COUNCIL exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 312-50V7 exam preparations and EC-COUNCIL certification application, do not hesitate to visit our Vcedump.com to find your solutions here.