Exam Details
Exam Code
:250-437Exam Name
:Administration of Symantec CloudSOC - version 1Certification
:Symantec CertificationsVendor
:SymantecTotal Questions
:75 Q&AsLast Updated
:Dec 16, 2024
Symantec Symantec Certifications 250-437 Questions & Answers
-
Question 61:
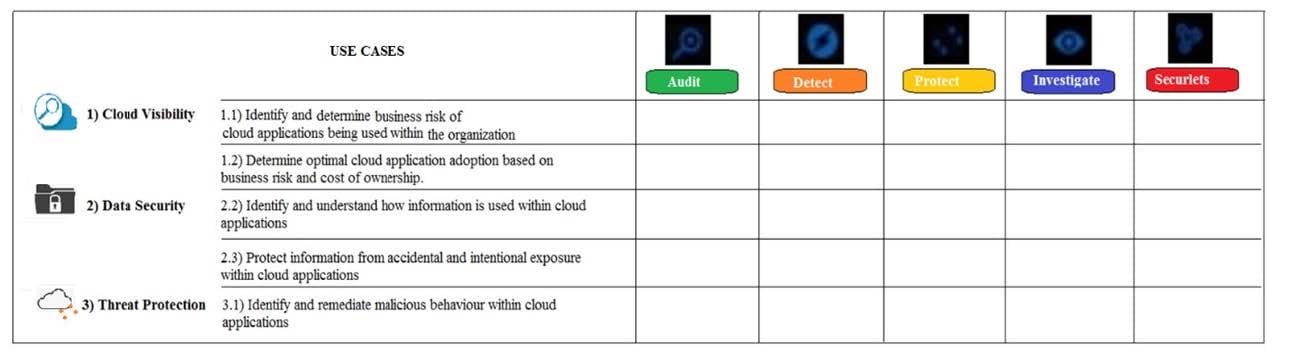
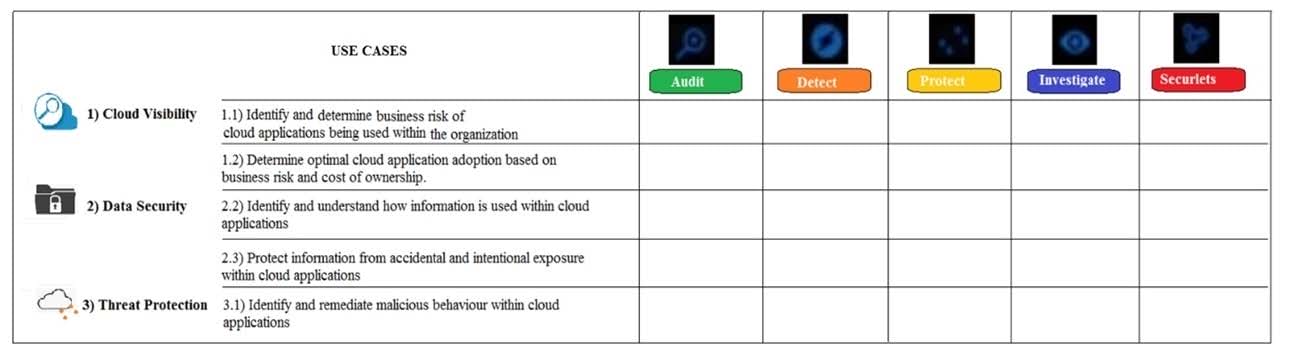
What modules are used in the use case "Identify and remediate malicious behavior within cloud applications"?
A. Detect, Protect, and Investigate
B. Detect and Investigate
C. Detect
D. Detect and Securlets
-
Question 62:
What compensatory control should an administrator implement if password quality rules of a cloud application has a low rating?
A. Single Sign On (SSO)
B. Block the application
C. Role based access
D. Biometric access
-
Question 63:
What module should an administrator use to create policies that restrict users from sharing data in unsafe ways?
A. Securlets
B. Audit
C. Protect
D. Detect
-
Question 64:
Which CloudSOC module is similar to a Data Loss Prevention (DLP) system?
A. Detect
B. Investigate
C. Audit
D. Protect
-
Question 65:
What data source types does Audit support?
A. SSH, FTP, Remote desktop
B. Web upload, SFTP, S3
C. PDF, DOC, XLS
D. APIs
-
Question 66:
Refer to the exhibit. Which modules are used in the use case "Determine optimal cloud application adoption based on business risk and cost of ownership"?
A. Audit and Protect
B. Audit
C. Detect, Protect, and Investigate
D. Protect, Investigate, and Securlets
-
Question 67:
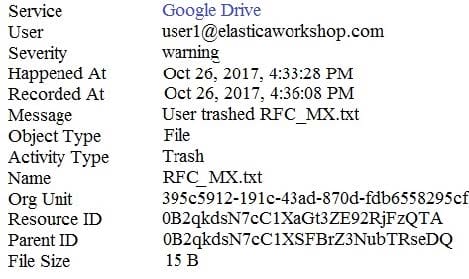
Refer to the exhibit. An administrator found this incident in the Investigate module.
What type of policy should an administrator create to get email notifications if the incident happens again?
A. File sharing policy
B. File transfer policy
C. Access monitoring policy
D. Data exposure policy
-
Question 68:
What is the objective of File Sharing policies?
A. To restrict the direct sharing of documents from cloud applications based both on their content and the characteristics of the user.
B. To prevent users from sharing documents, either publicly, externally, or internally.
C. To notify an administrator when activities, such as objects being modified, are performed in a cloud application.
D. To restrict the uploading and downloading of documents from the user's computer to the cloud application, based both on the content of the documents, and the characteristics of the user.
-
Question 69:
What type of policy should an administrator use to prevent a user that is behaving in anomalous ways from sharing public links while you monitor them?
A. Access monitoring
B. File transfer
C. Data exposure
D. Access enforcement
-
Question 70:
Refer to the exhibit. What modules are used in the use case "Protect information from accidental and intentional exposure within cloud applications"?
A. Protect and Investigate
B. Protect, Investigate, and Securlets
C. Protect and Audit
D. Protect and Securlets
Related Exams:
250-428
Administration of Symantec Endpoint Protection 14250-438
Administration of Symantec Data Loss Prevention 15250-440
Administration of Symantec PacketShaper 11.9.1250-441
Administration of Symantec Advanced Threat Protection 3.0250-445
Administration of Symantec Email Security.cloud (v1)250-447
Administration of Symantec Client Management Suite 8.5250-513
Administration of Symantec Data Loss Prevention 12250-556
Administration of Symantec ProxySG 6.7250-561
Endpoint Security Complete - Administration R1250-580
Endpoint Security Complete - R2 Technical Specialist
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Symantec exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 250-437 exam preparations and Symantec certification application, do not hesitate to visit our Vcedump.com to find your solutions here.