Exam Details
Exam Code
:250-437Exam Name
:Administration of Symantec CloudSOC - version 1Certification
:Symantec CertificationsVendor
:SymantecTotal Questions
:75 Q&AsLast Updated
:Dec 16, 2024
Symantec Symantec Certifications 250-437 Questions & Answers
-
Question 31:
What module should an administrator utilize to identify inherent risk in cloud applications?
A. Investigate
B. Audit
C. Detect
D. Protect
-
Question 32:
Where should an administrator locate unshared content within the Securlet module that contains risky information?
A. Exposed content
B. Activities
C. Other Risks
D. Apps
-
Question 33:
What type of connection should an administrator use when the network is sensitive to the bandwidth consumed by log traffic transfer to CloudSOC?
A. SCP
B. SpanVA
C. AWS S3 Bucket
D. APIs
-
Question 34:
What CloudSOC module should an administrator use to prevent the accidental and intentional exposure of information within cloud applications?
A. Detect
B. Audit
C. Protect
D. Investigate
-
Question 35:
What Rule Type in ContentIQ profiles do FERPA, GLBA, HIPAA, PCI AND PII belong to?
A. Regular expressions
B. Content types
C. Risk types
D. Keywords
-
Question 36:
Refer to the exhibit. Which module(s) are utilized in the use case "Identify and understand how information is used within cloud applications"?

A. Investigate
B. Securlets
C. Protect, Investigate, and Securlets
D. Detect, Protect, and Investigate
-
Question 37:
Refer to the exhibit from the Investigate module. What type of policy should an administrator utilize to
prevent users from accessing files using an unmanaged device?
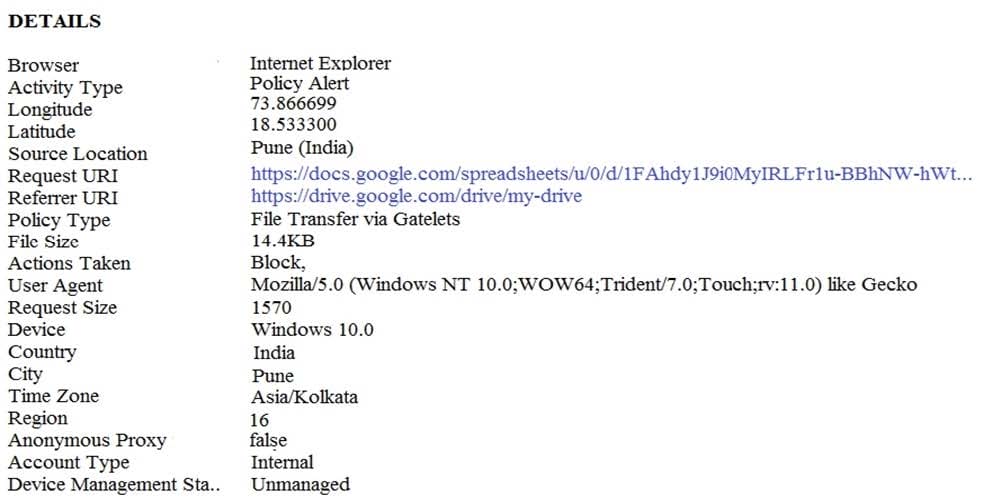
A. Access enforcement
B. File sharing
C. File transfer
D. Device enforcement
-
Question 38:
What step should an administrator complete immediately before being able to classify a cloud application using the cloud application adoption workflow?
A. Discover Shadow IT
B. Ensure compliance
C. Analyze usage
D. Identify risky apps
-
Question 39:
Refer to the exhibit. What action should an administrator take if this incident was found in the Investigate module?
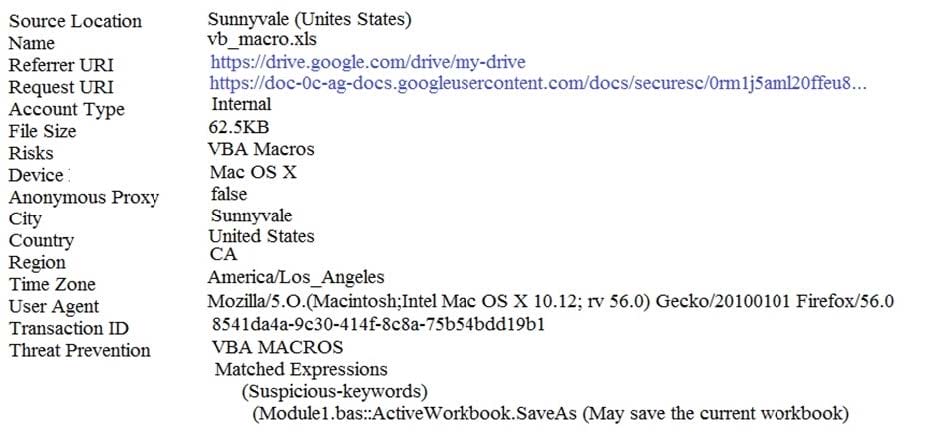
A. Create an access enforcement policy and block access to the file
B. Create a file transfer policy and block the download of the file
C. Create a file sharing policy and block the sharing of the file
D. Create an access monitoring policy and monitor the usage of the file
-
Question 40:
What is one of the security challenges generated by the proliferation of cloud applications?
A. Variety of endpoints
B. Cross-site scripting
C. Malware
D. Vulnerabilities
Related Exams:
250-428
Administration of Symantec Endpoint Protection 14250-438
Administration of Symantec Data Loss Prevention 15250-440
Administration of Symantec PacketShaper 11.9.1250-441
Administration of Symantec Advanced Threat Protection 3.0250-445
Administration of Symantec Email Security.cloud (v1)250-447
Administration of Symantec Client Management Suite 8.5250-513
Administration of Symantec Data Loss Prevention 12250-556
Administration of Symantec ProxySG 6.7250-561
Endpoint Security Complete - Administration R1250-580
Endpoint Security Complete - R2 Technical Specialist
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Symantec exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 250-437 exam preparations and Symantec certification application, do not hesitate to visit our Vcedump.com to find your solutions here.