Exam Details
Exam Code
:200-201Exam Name
:Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)Certification
:CyberOps AssociateVendor
:CiscoTotal Questions
:438 Q&AsLast Updated
:Jul 12, 2025
Cisco CyberOps Associate 200-201 Questions & Answers
-
Question 31:
Refer to the exhibit.
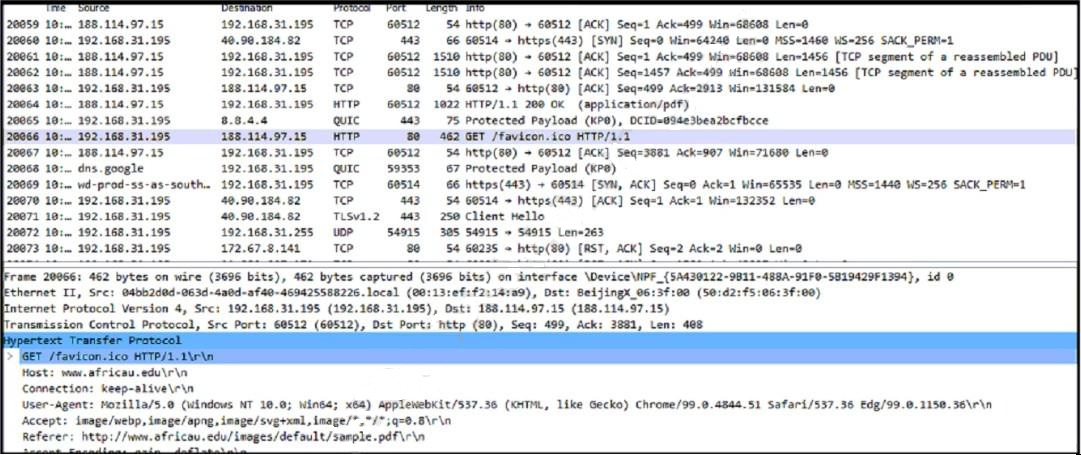
Which frame numbers contain a file that is extractable from Wireshark PCAP?
A. Frames No. 20064 and 20066
B. Frame No. 20064
C. Frame No. 20086
D. All Frames from No. 20061 to 20064
-
Question 32:
What is a scareware attack?
A. inserting malicious code that causes popup windows with flashing colors
B. overwhelming a targeted website with fake traffic
C. gaining access to your computer and encrypting data stored on it
D. using the spoofed email addresses to trick people into providing login credentials
-
Question 33:
What is sliding window anomaly detection?
A. Detect changes in operations and management processes.
B. Define response times for requests for owned applications.
C. Apply lowest privilege/permission level to software.
D. Identify uncommon patterns that do not fit usual behavior.
-
Question 34:
Which type of attack is a blank email with the subject "price deduction" that contains a malicious attachment?
A. integrity violation
B. smishing
C. phishing attack
D. man-in-the-middle attack
-
Question 35:
What is a difference between a threat and a risk?
A. A threat can be people, property, or information, and risk is a probability by which these threats may bring harm to the business.
B. A risk is a flaw or hole in security, and a threat is what is being used against that flaw.
C. A risk is an intersection between threat and vulnerabilities, and a threat is what a security engineer is trying to protect against.
D. A threat is a sum of risks, and a risk itself represents a specific danger toward the asset.
-
Question 36:
Which attack method is being used when an attacker tries to compromise a network with an authentication system that uses only 4-digit numeric passwords and no username?
A. replay
B. SQL injection
C. dictionary
D. cross-site scripting
-
Question 37:
Which process represents the application-level allow list?
A. allowing everything and denying specific executable files
B. allowing everything and denying specific applications protocols
C. allowing specific files and deny everything else
D. allowing specific format files and deny executable files
-
Question 38:
What does the Zero Trust security model signify?
A. Zero Trust security means that no one is trusted by default from inside or outside the network.
B. Zero Trust addresses access control and states that an individual should have only the minimum access privileges necessary to perform specific tasks.
C. Zero Trust states that no users should be given enough privileges to misuse the system on their own.
D. Zero Trust states that unless a subject is given explicit access to an object, it should be denied access to that object.
-
Question 39:
Which two measures are used by the defense-in-depth strategy? (Choose two.)
A. Bridge the single connection into multiple.
B. Divide the network into parts.
C. Split packets into pieces.
D. Implement the patch management process.
E. Reduce the load on network devices.
-
Question 40:
Which CVSS metric group identifies other components that are affected by a successful security attack?
A. scope
B. privileges required
C. integrity
D. attack vendor
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Cisco exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 200-201 exam preparations and Cisco certification application, do not hesitate to visit our Vcedump.com to find your solutions here.