Exam Details
Exam Code
:SPLK-1002Exam Name
:Splunk Core Certified Power UserCertification
:Splunk CertificationsVendor
:SplunkTotal Questions
:278 Q&AsLast Updated
:Aug 20, 2025
Splunk Splunk Certifications SPLK-1002 Questions & Answers
-
Question 11:
What is the Splunk Common Information Model (CIM)?
A. The CIM is a prerequisite that any data source must meet to be successfully onboarded into Splunk.
B. The CIM provides a methodology to normalize data from different sources and source types.
C. The CIM defines an ecosystem of apps that can be fully supported by Splunk.
D. The CIM is a data exchange initiative between software vendors.
-
Question 12:
Which syntax will find events where the values for the 1 field match the values for the Renewal-MonthYear field?
A. | where 10yearAnnerversary=Renewal-MonthYear
B. | where `10yearAnnerversary=Renewal-MonthYear
C. | where 10yearAnnerversary='Renewal-MonthYear'
D. | where `10yearAnnerversary'='Renewal-MonthYear'
-
Question 13:
Which of the following are valid options to speed up reports? (Select all the apply.)
A. Edit permissions
B. Edit description
C. Edit acceleration
D. Edit schedule
-
Question 14:
Which search would limit an "alert" tag to the "host" field?
A. tag=alert
B. host::tag::alert
C. tag==alert
D. tag::host=alert
-
Question 15:
We can use the rename command to _____ (Select all that apply.)
A. Change indexed fields
B. Exclude fields from our search results
C. Extract new fields from our data using regular expressions
D. Give a field a new name at search time
-
Question 16:
Data models are composed of one or more of which of the following datasets? (select all that apply)
A. Transaction datasets
B. Events datasets
C. Search datasets
D. Any child of event, transaction, and search datasets
-
Question 17:
How many ways are there to access the Field Extractor Utility?
A. 3
B. 4
C. 1
D. 5
-
Question 18:
Which of the following statements describes the use of the Filed Extractor (FX)?
A. The Field Extractor automatically extracts all field at search time.
B. The Field Extractor uses PERL to extract field from the raw events.
C. Field extracted using the Extracted persist as knowledge objects.
D. Fields extracted using the Field Extractor do not persist and must be defined for each search.
-
Question 19:
Why would the following search produce multiple transactions instead of one?
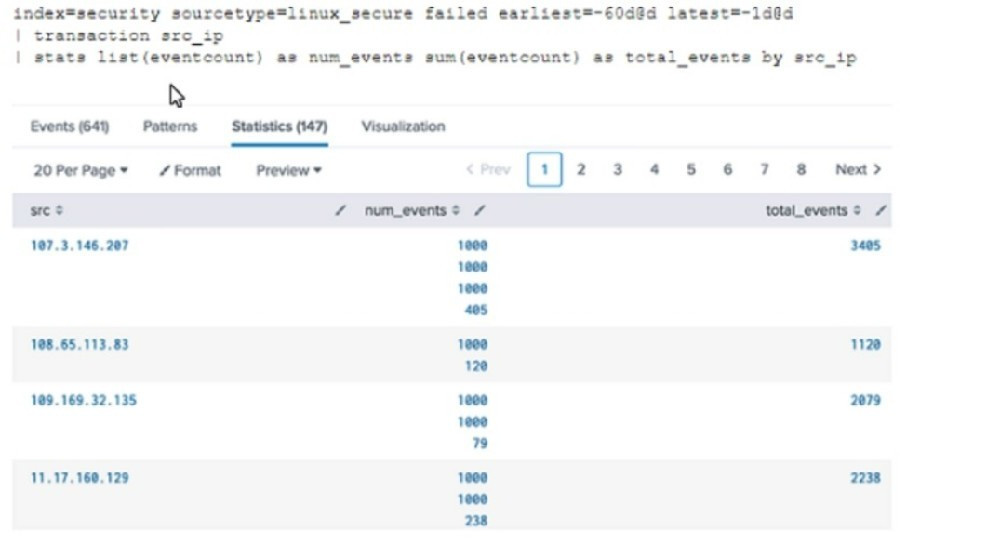
A. The maxspan option is not included.
B. The transaction command has a limit of 1000 events per transaction.
C. The transaction and commands cannot be used together.
D. The stats list () function is used.
-
Question 20:
Which of the following is true about data model attributes?
A. They cannot be created within the data model.
B. They can only be added into a root search dataset.
C. They cannot be edited if inherited from a parent dataset.
D. They can be added to a dataset from search time field extractions.
Related Exams:
SPLK-1001
Splunk Core Certified UserSPLK-1002
Splunk Core Certified Power UserSPLK-1003
Splunk Enterprise Certified AdminSPLK-1004
Splunk Core Certified Advanced Power UserSPLK-1005
Splunk Cloud Certified AdminSPLK-2001
Splunk Certified DeveloperSPLK-2002
Splunk Enterprise Certified ArchitectSPLK-2003
Splunk SOAR Certified Automation DeveloperSPLK-3001
Splunk Enterprise Security Certified AdminSPLK-3002
Splunk IT Service Intelligence Certified Admin
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Splunk exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your SPLK-1002 exam preparations and Splunk certification application, do not hesitate to visit our Vcedump.com to find your solutions here.