RC0-501 Exam Details
-
Exam Code
:RC0-501 -
Exam Name
:CompTIA Security+ Recertification Exam -
Certification
:CompTIA Security+ -
Vendor
:CompTIA -
Total Questions
:349 Q&As -
Last Updated
:May 24, 2026
CompTIA RC0-501 Online Questions & Answers
-
Question 231:
The Chief Technology Officer (CTO) of a company, Ann, is putting together a hardware budget for the next 10 years. She is asking for the average lifespan of each hardware device so that she is able to calculate when she will have to replace
each device.
Which of the following categories BEST describes what she is looking for?
A. ALE
B. MTTR
C. MTBF
D. MTTF -
Question 232:
A new security policy in an organization requires that all file transfers within the organization be completed using applications that provide secure transfer. Currently, the organization uses FTP and HTTP to transfer files. Which of the following should the organization implement in order to be compliant with the new policy?
A. Replace FTP with SFTP and replace HTTP with TLS
B. Replace FTP with FTPS and replaces HTTP with TFTP
C. Replace FTP with SFTP and replace HTTP with Telnet
D. Replace FTP with FTPS and replaces HTTP with IPSec -
Question 233:
A security analyst is reviewing the following packet capture of an attack directed at a company's server located in the DMZ:
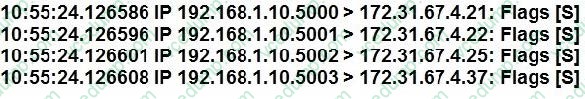
Which of the following ACLs provides the BEST protection against the above attack and any further attacks from the same IP, while minimizing service interruption?
A. DENY TCO From ANY to 172.31.64.4
B. Deny UDP from 192.168.1.0/24 to 172.31.67.0/24
C. Deny IP from 192.168.1.10/32 to 0.0.0.0/0
D. Deny TCP from 192.168.1.10 to 172.31.67.4 -
Question 234:
A network administrator wants to implement a method of securing internal routing. Which of the following should the administrator implement?
A. DMZ
B. NAT
C. VPN
D. PAT -
Question 235:
Which of the following types of cloud Infrastructures would allow several organizations with similar structures and interests to realize shared storage and resources?
A. Private
B. Hybrid
C. Public
D. Community -
Question 236:
Joe, a security administrator, needs to extend the organization's remote access functionality to be used by staff while travelling. Joe needs to maintain separate access control functionalities for internal, external, and VOIP services. Which of the following represents the BEST access technology for Joe to use?
A. RADIUS
B. TACACS+
C. Diameter
D. Kerberos -
Question 237:
Which of the following is the summary of loss for a given year?
A. MTBF
B. ALE
C. SLA
D. ARO -
Question 238:
During a recent audit, it was discovered that several user accounts belonging to former employees were still active and had valid VPN permissions. Which of the following would help reduce the amount of risk the organization incurs in this situation in the future?
A. Time-of-day restrictions
B. User access reviews
C. Group-based privileges
D. Change management policies -
Question 239:
A network operations manager has added a second row of server racks in the datacenter. These racks face the opposite direction of the first row of racks. Which of the following is the reason the manager installed the racks this way?
A. To lower energy consumption by sharing power outlets
B. To create environmental hot and cold isles
C. To eliminate the potential for electromagnetic interference
D. To maximize fire suppression capabilities -
Question 240:
A security administrator needs to implement a system that detects possible intrusions based upon a vendor provided list. Which of the following BEST describes this type of IDS?
A. Signature based
B. Heuristic
C. Anomaly-based
D. Behavior-based
Related Exams:
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CompTIA exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your RC0-501 exam preparations and CompTIA certification application, do not hesitate to visit our Vcedump.com to find your solutions here.