Exam Details
Exam Code
:NS0-194Exam Name
:NetApp Certified Support EngineerCertification
:NetApp CertificationsVendor
:NetAppTotal Questions
:60 Q&AsLast Updated
:Aug 07, 2025
NetApp NetApp Certifications NS0-194 Questions & Answers
-
Question 51:
A disaster causes a FlexGroup volume to be unrecoverable, but it was protected by a SnapMirror relationship. You solve the issue, and the source is operational. Now, you want to return to serving the data from the original source.
In this scenario, what do you do next?
A. Initialize the SnapMirror relationship.
B. Restore data from a backup copy.
C. Perform a SnapMirror update.
D. Delete the SnapMirror relationship.
-
Question 52:
You are working on a fabric MetroCluster. After a site failure, the plex starts to resync automatically to the aggregate mirror of Aggr1. The plex now shows a status of resyncing. During this process, you experience a slow resync of the SyncMirror plex.
In this scenario, how do you solve the problem?
A. Add more disks to the aggregate to add more I/O capacity.
B. Destroy and re-create plex, then run a baseline sync.
C. Tune the resync speed by adding a QoS policy and limit the concurrent I/O to the aggregate.
D. Tune the resync speed using the storage raid-options command.
-
Question 53:
Which three techniques are used in ONTAP to improve storage efficiencies? (Choose three.)
A. compression
B. encryption
C. compaction
D. ADP
E. thin provisioning
-
Question 54:
You need to provide a customer an action plan to update an ONTAP system after a security bulletin has been issued.
In this scenario, how do you accomplish this task?
A. Use the Interoperability Matrix Tool.
B. Review the ONTAP 9 product page.
C. Download the target version and do a pre-check.
D. Use Upgrade Advisor on Active IQ.
-
Question 55:
What is the minimum number of compute nodes required to run the NetApp Deployment Engine for NetApp HCI?
A. 2
B. 1
C. 3
D. 4
-
Question 56:
Which NetApp technology enables you to perform block-based replication from NetApp Element software to Cloud Volumes ONTAP?
A. SyncMirror
B. SnapMirror
C. Cloud Sync
D. MetroCluster
-
Question 57:
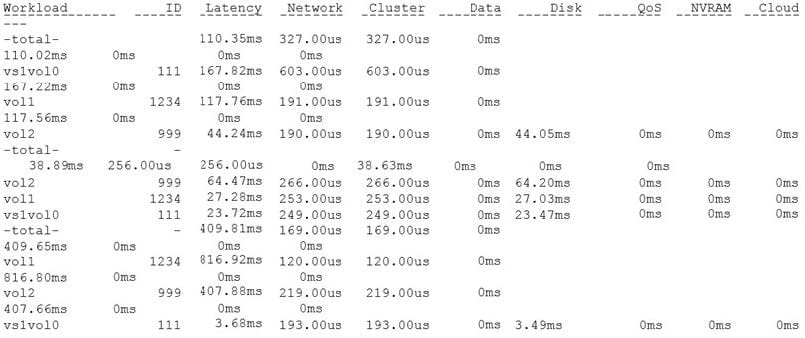
Referring to the exhibit, which two components should be examined? (Choose two.)
A. cluster switches
B. SAS adapter
C. network interface card
D. disk
-
Question 58:
What are two reasons to use VLANs in a NetApp storage solution? (Choose two.)
A. to isolate UDP traffic from TCP traffic
B. to isolate management traffic from other IP traffic
C. to isolate iSCSI traffic from NAS traffic
D. to isolate FC traffic from other IP traffic
-
Question 59:
Which CIFS server configuration determines the domain controllers that a CIFS server uses?
A. site membership
B. enabled SMB versions
C. trusted domains
D. discovery mode
-
Question 60:
For security reasons, you must track the access of files of a specific folder.
In this scenario, what should you do to accomplish this task from the storage side?
A. Implement a Vscan solution.
B. Use a cron job to save the audit log.
C. Use role-based access control to track access.
D. Implement an FPolicy solution.
Related Exams:
NS0-002
NetApp Certified Technology Associate - NCSA - HCNS0-003
NetApp Certified Technology AssociateNS0-004
NetApp Certified Technology Solutions ProfessionalNS0-093
NetApp Accredited Hardware Support EngineerNS0-101
NetApp Accredited Sales ProfessionalNS0-111
Network Appliance Storage AssociateNS0-120
Data ONTAP AdvancedNS0-121
Network Appliance Data ONTAP Advanced Exam 7GNS0-130
Storage Professional Data ProtectionNS0-131
Network Appliance Data Protection Exam 7G
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only NetApp exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your NS0-194 exam preparations and NetApp certification application, do not hesitate to visit our Vcedump.com to find your solutions here.