Exam Details
Exam Code
:NS0-159Exam Name
:NetApp Certified Data Administrator, ONTAPCertification
:NetApp CertificationsVendor
:NetAppTotal Questions
:89 Q&AsLast Updated
:Jul 12, 2025
NetApp NetApp Certifications NS0-159 Questions & Answers
-
Question 11:
You want to create a FlexGroup volume that contains four aggregates with eight constituents each. In this scenario, what is the value of the aggregate list multiplier?
A. 2
B. 32
C. 8
D. 4
-
Question 12:
You use the Automated Workload Analyzer (AWA) to identify workloads that would benefit from which feature?
A. Flash Pool aggregates
B. Advances Disk Partitioning
C. storage efficiency
D. FabricPool capacity tier
-
Question 13:
Your company requires storage administrators to use a second authentication method when accessing OnCommand System Manager and OnCommand Unified Manager. After entering their user name and password, administrators must enter a Personal Identity Verification (PIV) code from a smart card or a mobile device.
With which resource would you accomplish this objective?
A. an Active Directory server
B. a third-party key manager
C. a third-party identity provider
D. the ONTAP onboard key manager
-
Question 14:
A storage administrator is not receiving performance alerts on an OnCommand Unified Manager policy that was created for a NAS volume.
Which additional task Is required to solve this problem?
A. You should assign a tiering policy.
B. You should assign the performance threshold policy.
C. You should clear the performance threshold policy.
D. You should search for volume datA.
-
Question 15:
You want to asynchronously replicate an SVM's volumes and configuration to another NetApp cluster. Which data protection technology accomplishes this task?
A. MetroCluster
B. SnapVault
C. SVM disaster recovery
D. SnapMirror
-
Question 16:
The vsadmin account for SVM vs1 is unlocked and configured with a password.
Which two statements are true about login methods for the vsadmin account? (Choose two.)
A. You access SSH.
B. You access ONTAP API
C. You access Onommand System Manager.
D. You access Onommand Unified Manager.
-
Question 17:
Click the Exhibit button.
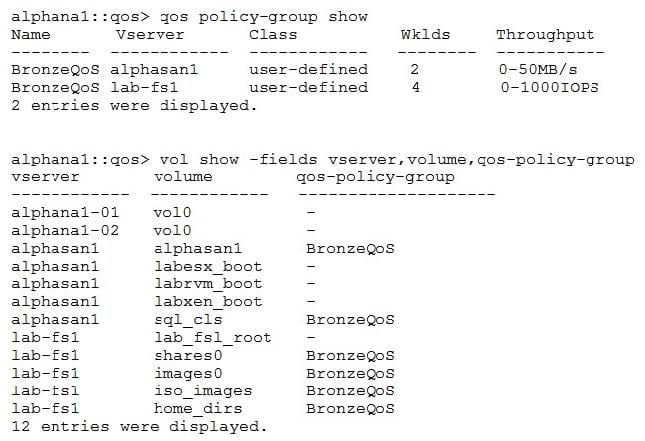
Referring to the exhibit, what is the throughput limit for the shares0 volume?
A. 250 IOPS
B. 25 MB/s
C. 50 MB/s
D. 1000 IOPS
-
Question 18:
A user cannot delete the files in a volume's Snapshot copy. In this scenario, what is the problem?
A. A retention period was configured for the Snapshot copy.
B. Snapshot copies are read only.
C. The files are being used by another user.
D. The user does not have the required permission.
-
Question 19:
Click the Exhibit button.

A volume is only 25% full; however, the snapshot reserve is almost full. Referring to the exhibit, what occurs after the volume's snapshot reserve is full?
A. The creation of new Snapshot copies fails.
B. User-created Snapshot copies are deleted, beginning with the oldest, until the snapshot reserve has 20% free space.
C. Snapshot copies start consuming the volume's free space.
D. Scheduled Snapshot copies are deleted, beginning with the oldest, until the snapshot reserve has 20% free space.
-
Question 20:
You have a 4-node cluster and want to ensure that a new NAS LIF can fail over to any node. In this scenario, which two actions are required to configure the LIF? (Choose two.)
A. Add ports from all nodes to the LIF's broadcast domain.
B. Configure the failover policy tobroadcast-domain-wide.
C. Add ports from all nodes to the LIF's home port list.
D. Configure the failover policy tosystem-defined.
Related Exams:
NS0-002
NetApp Certified Technology Associate - NCSA - HCNS0-003
NetApp Certified Technology AssociateNS0-004
NetApp Certified Technology Solutions ProfessionalNS0-093
NetApp Accredited Hardware Support EngineerNS0-101
NetApp Accredited Sales ProfessionalNS0-111
Network Appliance Storage AssociateNS0-120
Data ONTAP AdvancedNS0-121
Network Appliance Data ONTAP Advanced Exam 7GNS0-130
Storage Professional Data ProtectionNS0-131
Network Appliance Data Protection Exam 7G
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only NetApp exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your NS0-159 exam preparations and NetApp certification application, do not hesitate to visit our Vcedump.com to find your solutions here.