CIPM Exam Details
-
Exam Code
:CIPM -
Exam Name
:Certified Information Privacy Manager (CIPM) -
Certification
:IAPP Certifications -
Vendor
:IAPP -
Total Questions
:627 Q&As -
Last Updated
:May 28, 2026
IAPP CIPM Online Questions & Answers
-
Question 141:
Business management should be engaged in the creation of Business Continuity (BC) and Disaster Recovery plans (DRP) because they need to
A. Ensure that the technology chosen for implementation meets all of the requirements.
B. Provide resources and support for the development and testing of the plan.
C. Predetermine spending for development and implantation of the plan.
D. Specify the solution and options around which the plans will be developed. -
Question 142:
An organizational policy requires that any data from organization-issued devices be securely destroyed before disposal. Which method provides the BEST assurance of data destruction?
A. Incinerating
B. Reformatting
C. Degaussing
D. Erasing -
Question 143:
Which of the following states of data becomes MOST important to protect as organizations continue to transition toward Application Programming Interface (API)-based solutions?
A. Data at rest
B. Data in use
C. Data in transit
D. Data on the client machine -
Question 144:
Which of the following MUST be checked during the validation of software verification capabilities?
A. Completeness
B. Vulnerabilities
C. Security
D. Logic -
Question 145:
What does the Role-Based Access Control (RBAC) method define?
A. What equipment is needed to perform
B. How information is accessed within a system
C. What actions the user can or cannot do
D. How to apply the security labels in a system -
Question 146:
An organization wants to implement Zero Trust (ZT). The Information Technology (IT) department is already using Multi-Factor Authentication (MFA) and Identity and Access Management (IAM). Which of the following would be the BEST solution for the organization to implement in order to have a ZT network?
A. Next-generation firewall
B. Host-Based Intrusion Detection System (HIDS)
C. Micro-segmentation
D. Network Intrusion Detection System (NIDS) -
Question 147:
An organization's security policy requires remote hosts to be authenticated before they can access network resources. Which of the following is the BEST option for the organization to enforce its policy?
A. Install a firewall.
B. Implement Internet Protocol (IP) Access Control Lists (ACL).
C. Implement 802.1X.
D. Install an Intrusion Prevention System (IPS). -
Question 148:
Which of the following ensures privileges are current and appropriately reflect an individual's authorized roles and responsibilities?
A. Access authorization
B. Identity management
C. Access approval
D. Access review -
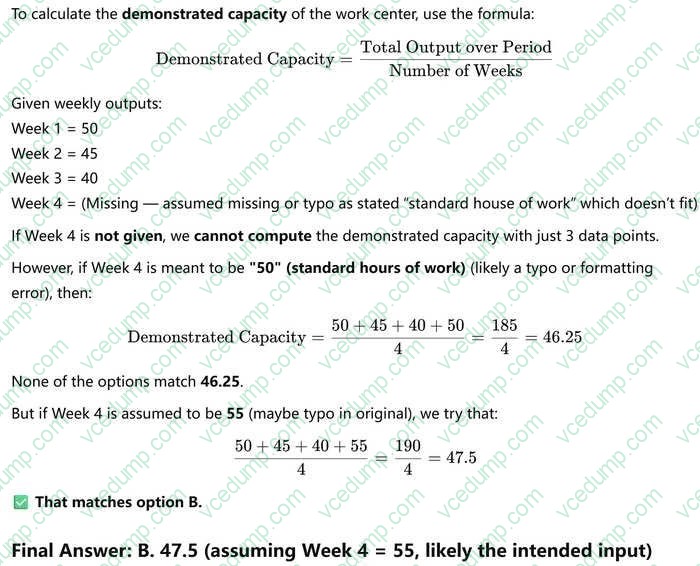
Question 149:
Over a period of 4 weeks, a work center produced 50, 45, 40, and standard house of work. What is the demonstrated capacity of the work center?
A. 47.8
B. 47.5
C. 48
D. 49.5 -
Question 150:
An organization recently completed an acquisition of another entity and staff members are complaining about the excessive number of credentials they need to remember as each application requires separate logins. This is negatively affecting collaboration efficiency and increasing the risk of human errors. What will the organization consider implementing as part of the solution to improve the situation?
A. Open Authorization (OAuth) 2.0
B. Security Assertion Markup Language (SAML) 2.0
C. Password Authentication Protocol (PAP)
D. OpenID Connect (OIDC)
Related Exams:
-
AIGP
Artificial Intelligence Governance Professional (AIGP) -
CIPM
Certified Information Privacy Manager (CIPM) -
CIPP-A
Certified Information Privacy Professional/Asia (CIPP/A) -
CIPP-C
Certified Information Privacy Professional/ Canada (CIPP/C) -
CIPP-E
Certified Information Privacy Professional/Europe (CIPP/E) -
CIPP-US
Certified Information Privacy Professional/United States (CIPP/US) -
CIPT
Certified Information Privacy Technologist (CIPT)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only IAPP exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your CIPM exam preparations and IAPP certification application, do not hesitate to visit our Vcedump.com to find your solutions here.