AZ-305 Exam Details
-
Exam Code
:AZ-305 -
Exam Name
:Designing Microsoft Azure Infrastructure Solutions -
Certification
:Microsoft Certifications -
Vendor
:Microsoft -
Total Questions
:400 Q&As -
Last Updated
:Jan 05, 2026
Microsoft AZ-305 Online Questions & Answers
-
Question 1:
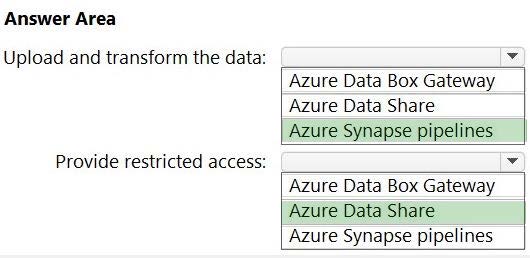
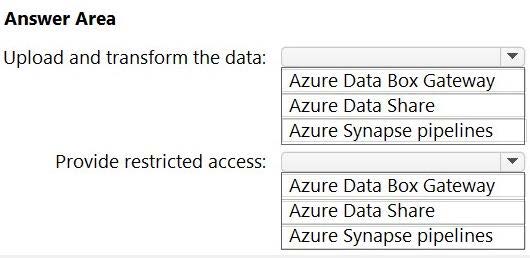
HOTSPOT Your company, named Contoso, Ltd., has an Azure subscription that contains the following resources: An Azure Synapse Analytics workspace named contosoworkspace1
An Azure Data Lake Storage account named contosolake1 An Azure SQL database named contososql1 The product data of Contoso is copied from contososql1 to contosolake1.
Contoso has a partner company named Fabrikam Inc. Fabrikam has an Azure subscription that contains the following resources: A virtual machine named FabrikamVM1 that runs Microsoft SQL Server 2019 An Azure Storage account named fabrikamsa1
Contoso plans to upload the research data on FabrikamVM1 to contosolake1. During the upload, the research data must be transformed to the data formats used by Contoso.
The data in contosolake1 will be analyzed by using contosoworkspace1.
You need to recommend a solution that meets the following requirements:
Upload and transform the FabrikamVM1 research data.
Provide Fabrikam with restricted access to snapshots of the data in contosoworkspace1.
What should you recommend for each requirement? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
-
Question 2:
What should you recommend to meet themonitoring requirements for App2?
A. Microsoft Sentinel
B. Azure Application Insights
C. Container insights
D. VM insights
-
Question 3:
You need to recommend a solution that meets the application development requirements. What should you include in the recommendation?
A. an Azure Container Registry instance
B. deployment slots
C. Continuous Integration/Continuous Deployment (CI/CD) sources
D. the Azure App Configuration service
-
Question 4:
What should you recommend lo meet the monitoring requirements for App2?
A. Azure Application Insights
B. Container insights
C. Microsoft Sentinel
D. VM insights
-
Question 5:
You need to recommend a solution to meet the database retention requirements. What should you recommend?
A. Configure a long-term retention policy for the database.
B. Configure Azure Site Recovery.
C. Use automatic Azure SQL Database backups.
D. Configure geo-replication of the database.
-
Question 6:
What should you include in the identity management strategy to support the planned changes?
A. Deploy domain controllers for corp.fabrikam.com to virtual networks in Azure.
B. Move all the domain controllers from corp.fabrikam.com to virtual networks in Azure.
C. Deploy a new Azure AD tenant for the authentication of new RandD projects.
D. Deploy domain controllers for the rd.fabrikam.com forest to virtual networks in Azure.
-
Question 7:
You need to recommend an App Service architecture that meets the requirements for App1.
The solution must minimize costs.
What should few recommend?
A. one App Service Environment (ASE) per availability zone
B. one App Service plan per availability zone
C. one App Service plan per region
D. one App Service Environment (ASE) per region
-
Question 8:
A company has an on-premises file server cbflserver that runs Windows Server 2019.
Windows Admin Center manages this server. The company owns an Azure subscription.
You need to provide an Azure solution to prevent data loss if the file server fails.
Solution: You decide to create an Azure Recovery Services vault. You then decide to install the Azure Backup agent and then schedule the backup.
Would this meet the requirement?
A. Yes
B. No
-
Question 9:
You need to recommend a solution that meets the data requirements for App1.
What should you recommend deploying to each availability zone that contains an instance of App1?
A. an Azure Cosmos DB that uses multi-region writes
B. an Azure Data Lake store that uses geo-zone-redundant storage (GZRS)
C. an Azure SQL database that uses active geo-replication
D. an Azure Storage account that uses geo-zone-redundant storage (GZRS)
-
Question 10:
You plan to migrate App1 to Azure. The solution must meet the authentication and authorization requirements. Which type of endpoint should App1 use to obtain an access token?
A. Azure Instance Metadata Service (IMDS)
B. Azure AD
C. Azure Service Management
D. Microsoft identity platform
Related Exams:
-
62-193
Technology Literacy for Educators -
70-243
Administering and Deploying System Center 2012 Configuration Manager -
70-355
Universal Windows Platform – App Data, Services, and Coding Patterns -
77-420
Excel 2013 -
77-427
Excel 2013 Expert Part One -
77-725
Word 2016 Core Document Creation, Collaboration and Communication -
77-726
Word 2016 Expert Creating Documents for Effective Communication -
77-727
Excel 2016 Core Data Analysis, Manipulation, and Presentation -
77-728
Excel 2016 Expert: Interpreting Data for Insights -
77-731
Outlook 2016 Core Communication, Collaboration and Email Skills
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Microsoft exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your AZ-305 exam preparations and Microsoft certification application, do not hesitate to visit our Vcedump.com to find your solutions here.