Exam Details
Exam Code
:JN0-541Exam Name
:IDP, Associate(JNCIA-IDP)Certification
:Juniper CertificationsVendor
:JuniperTotal Questions
:120 Q&AsLast Updated
:Aug 24, 2025
Juniper Juniper Certifications JN0-541 Questions & Answers
-
Question 171:
Which three actions should be taken on a rule in the IDP rule base when the sensor is in transparent mode? (Choose three.)
A. Close client and server.
B. Drop stream.
C. Drop connection.
D. Drop packet.
-
Question 172:
You implement Traffic Anomaly detection and you find numerous alerts of port scans from your security auditing team that you want to ignore. You create an address book entry for the security audit team specifying the IP addresses of those machines. What should you do next?
A. Create a rule at the top of the Traffic Anomaly rule base to ignore traffic from security audit team, and make this a terminal rule.
B. Create a rule at the top of the Traffic Anomalyrulebase to ignore traffic from security audit team.
C. Create a rule at the top of the IDPrulebase to ignore traffic from security audit team, and make this a terminal rule.
D. Create an exempt rule for the security audit team in the Exemptrulebase to ignore Traffic Anomalies.
-
Question 173:
If the power is lost to an IDP sensor, which feature allows the traffic to continue to flow through the device?
A. NIC bypass
B. peer port modulation
C. protocol anomaly detection
D. stateful inspection
-
Question 174:
Exhibit:
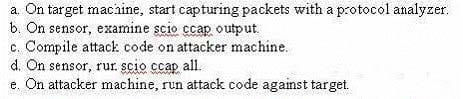
In order to obtain attack information so that you can create a new attack object definition, you must follow certain steps. Given the steps in the exhibit, assume you have acquired the attack source code. What is the correct order for these steps?
A. c, e, b, d, a
B. c, d, a, e, b
C. c, d, e, a, b
D. e, c, d, b, a
-
Question 175:
Which two statements describe action versus IP action? (Choose two.)
A. IP action responds to matching traffic by dropping or closing current attack packets or connection.
B. Action responds to matching traffic by dropping or closing current attacking packets or connection.
C. IP Action responds to future traffic based on a previous match by blocking or dropping future connections.
D. Action responds to future traffic based on a previous match by blocking or dropping future connections.
-
Question 176:
Which two statements are true? (Choose two.)
A. If the source IP, target IP, and service in a packet match a particular IDP rule, the rule's action will be performed.
B. All of the rules in the IDPrulebase are examined until either the end of the list is reached, or a matching rule has the Terminate Match button checked.
C. One packet can match on multiple IDP rules.
D. Once the IDP sensor stops comparing a packet against the list of IDP rules, it performs only the first action in the matching rules.
-
Question 177:
Within the SYN protector rule base, what is the function of relay action?
A. It will create a session with the server only if the client completes the three-step TCP handshake with the sensor.
B. It will monitor new connections to a protected server, but not prevent them.
C. It will relay all SYN connections to a fake IP.
D. It will not monitor incoming SYN requests.
-
Question 178:
Which sensor process handles policy installation?
A. idp
B. sciod
C. agent
D. profiler
E. idpLogReader
-
Question 179:
Which three are assigned as a result of running EasyConfig? (Choose three.)
A. sensor eth1 IP address
B. sensor default gateway
C. sensor HA configuration
D. sensor eth0 IP address
E. sensor deployment mode
-
Question 180:
Which sctop option will display current throughput rate for the sensor?
A. u
B. s
C. t
D. r
Related Exams:
JN0-102
Internet Associate, Junos(JNCIA-Junos)JN0-104
Junos, Associate (JNCIA-Junos)JN0-105
Junos, Associate (JNCIA-Junos)JN0-1101
Juniper Networks Certified Design Associate (JNCDA)JN0-1103
Design, Associate (JNCIA-Design)JN0-130
Juniper networks Certified internet specialist.e(jncis-e)JN0-1301
Data Center Design, Specialist (JNCDS-DC)JN0-1302
Data Center Design Specialist (JNCDS-DC)JN0-1331
Security Design, Specialist (JNCDS-SEC)JN0-1332
Security Design, Specialist (JNCDS-SEC)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Juniper exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your JN0-541 exam preparations and Juniper certification application, do not hesitate to visit our Vcedump.com to find your solutions here.