Exam Details
Exam Code
:350-701Exam Name
:Implementing and Operating Cisco Security Core Technologies (SCOR)Certification
:CCNPVendor
:CiscoTotal Questions
:655 Q&AsLast Updated
:Apr 23, 2024
Cisco CCNP 350-701 Questions & Answers
-
Question 31:
An engineer is configuring device-hardening on a router in order to prevent credentials from being seen if the router configuration was compromised. Which command should be used?
A. service password-encryption
B. username
privilege 15 password C. service password-recovery
D. username < username> password
-
Question 32:
Which type of data exfiltration technique encodes data in outbound DNS requests to specific servers and can be stopped by Cisco Umbrella?
A. DNS tunneling
B. DNS flood attack
C. cache poisoning
D. DNS hijacking
-
Question 33:
Which two protocols must be configured to authenticate end users to the Web Security Appliance? (Choose two.)
A. NTLMSSP
B. Kerberos
C. CHAP
D. TACACS+
E. RADIUS
-
Question 34:
Which two functions does the Cisco Advanced Phishing Protection solution perform in trying to protect from phishing attacks? (Choose two.)
A. blocks malicious websites and adds them to a block list
B. does a real-time user web browsing behavior analysis
C. provides a defense for on-premises email deployments
D. uses a static algorithm to determine malicious
E. determines if the email messages are malicious
-
Question 35:
What is the purpose of the Cisco Endpoint loC feature?
A. It provides stealth threat prevention.
B. lt is a signature-based engine.
C. lt is an incident response tool
D. It provides precompromise detection.
-
Question 36:
Which attribute has the ability to change during the RADIUS CoA?
A. NTP
B. Authorization
C. Accessibility
D. Membership
-
Question 37:
Which two capabilities of Integration APIs are utilized with Cisco DNA center? (Choose two)
A. Automatically deploy new virtual routers
B. Upgrade software on switches and routers
C. Application monitors for power utilization of devices and IoT sensors
D. Connect to Information Technology Service Management Platforms
E. Create new SSIDs on a wireless LAN controller
-
Question 38:
What is a description of microsegmentation?
A. Environments apply a zero-trust model and specify how applications on different servers or containers can communicate
B. Environments deploy a container orchestration platform, such as Kubernetes, to manage the application delivery
C. Environments implement private VLAN segmentation to group servers with similar applications.
D. Environments deploy centrally managed host-based firewall rules on each server or container
-
Question 39:
Which method of attack is used by a hacker to send malicious code through a web application to an unsuspecting user to request that the victim's web browser executes the code?
A. buffer overflow
B. browser WGET
C. SQL injection
D. cross-site scripting
-
Question 40:
Refer to the exhibit.
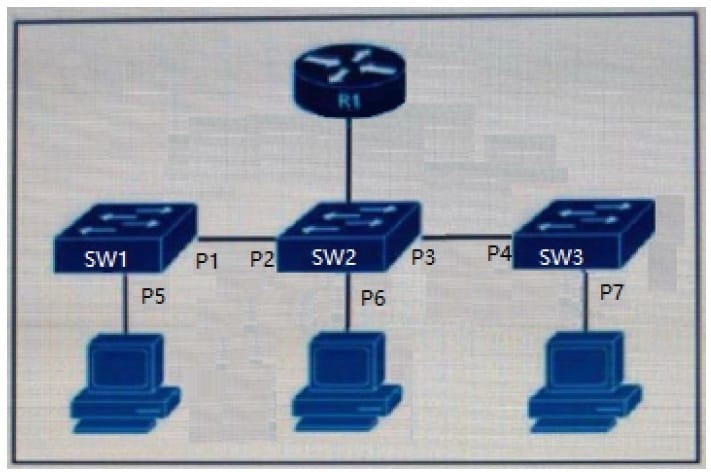
The DHCP snooping database resides on router R1, and dynamic ARP inspection is configured only on switch SW2. Which ports must be configured as untrusted so that dynamic ARP inspection operates normally?
A. P2 and P3 only
B. P5, P6, and P7 only
C. P1, P2, P3, and P4 only
D. P2, P3, and P6 only
Related Exams:
300-610
Designing Cisco Data Center Infrastructure (DCID)350-501
Implementing and Operating Cisco Service Provider Network Core Technologies (SPCOR)350-701
Implementing and Operating Cisco Security Core Technologies (SCOR)350-601
Implementing and Operating Cisco Data Center Core Technologies (DCCOR)350-801
Implementing and Operating Cisco Collaboration Core Technologies (CLCOR)350-401
Implementing and Operating Cisco Enterprise Network Core Technologies (ENCOR) & CCIE Enterprise Infrastructure & CCIE Enterprise Wireless300-535
Automating and Programming Cisco Service Provider Solutions (SPAUTO)300-515
Implementing Cisco Service Provider VPN Services (SVPI)300-510
Implementing Cisco Service Provider Advanced Routing Solutions (SPRI)300-735
Automating and Programming Cisco Security Solutions (SAUTO)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Cisco exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 350-701 exam preparations and Cisco certification application, do not hesitate to visit our Vcedump.com to find your solutions here.