Exam Details
Exam Code
:300-720Exam Name
:Securing Email with Cisco Email Security Appliance (SESA)Certification
:CCNP SecurityVendor
:CiscoTotal Questions
:148 Q&AsLast Updated
:Aug 06, 2025
Cisco CCNP Security 300-720 Questions & Answers
-
Question 131:
Which benefit does enabling external spam quarantine on Cisco SMA provide?
A. ability to back up spam quarantine from multiple Cisco ESAs to one central console
B. access to the spam quarantine interface on which a user can release, duplicate, or delete
C. ability to scan messages by using two engines to increase a catch rate
D. ability to consolidate spam quarantine data from multiple Cisco ESA to one central console
-
Question 132:
When email authentication is configured on Cisco ESA, which two key types should be selected on the signing profile? (Choose two.)
A. DKIM
B. Public Keys
C. Domain Keys
D. Symmetric Keys
E. Private Keys
-
Question 133:
Which feature utilizes sensor information obtained from Talos intelligence to filter email servers connecting into the Cisco ESA?
A. SenderBase Reputation Filtering
B. Connection Reputation Filtering
C. Talos Reputation Filtering
D. SpamCop Reputation Filtering
-
Question 134:
When the Spam Quarantine is configured on the Cisco ESA, what validates end-users via LDAP during login to the End-User Quarantine?
A. Enabling the End-User Safelist/Blocklist feature
B. Spam Quarantine External Authentication Query
C. Spam Quarantine End-User Authentication Query
D. Spam Quarantine Alias Consolidation Query
-
Question 135:
Which SMTP extension does Cisco ESA support for email security?
A. ETRN
B. UTF8SMTP
C. PIPELINING
D. STARTTLS
-
Question 136:
DRAG DROP
An administrator must ensure that emails sent from [email protected] are routed through an alternate virtual gateway. Drag and drop the snippet from the bottom onto the blank in the graphic to finish the message filter syntax. Not all snippets are used.
Select and Place:

-
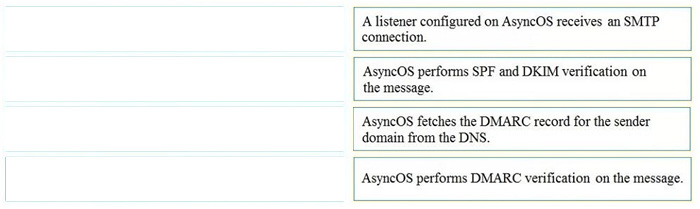
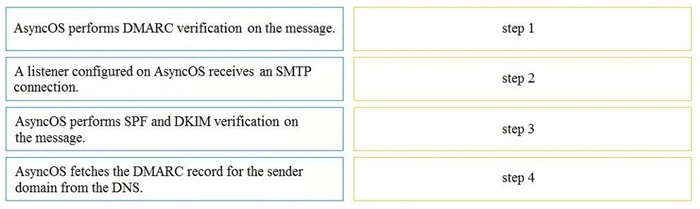
Question 137:
DRAG DROP
Drag and drop the AsyncOS methods for performing DMARC verification from the left into the correct order on the right.
Select and Place:
-
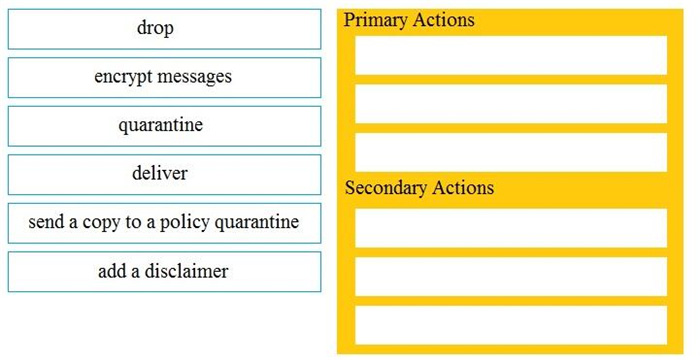
Question 138:
DRAG DROP
Drag and drop the Cisco ESA reactions to a possible DLP from the left onto the correct action types on the right.
Select and Place:
-
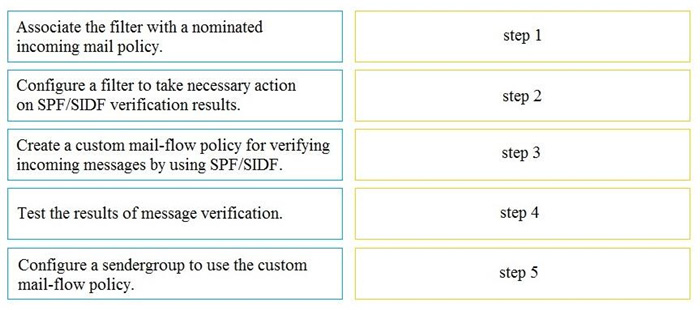
Question 139:
DRAG DROP
Drag and drop the steps to configure Cisco ESA to use SPF/SIDF verification from the left into the correct order on the right.
Select and Place:
-
Question 140:
DRAG DROP
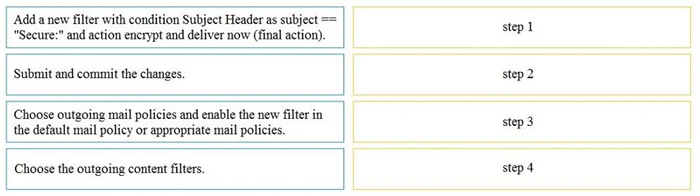
An Encryption Profile has been set up on the Cisco ESA.
Drag and drop the steps from the left for creating an outgoing content filter to encrypt emails that contains the subject "Secure:" into the correct order on the right.
Select and Place:
Related Exams:
300-710
Securing Networks with Cisco Firepower (SNCF)300-715
Implementing and Configuring Cisco Identity Services Engine (SISE)300-720
Securing Email with Cisco Email Security Appliance (SESA)300-725
Securing the Web with Cisco Web Security Appliance (SWSA)300-730
Implementing Secure Solutions with Virtual Private Networks (SVPN)300-735
Automating and Programming Cisco Security Solutions (SAUTO)350-701
Implementing and Operating Cisco Security Core Technologies (SCOR)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Cisco exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 300-720 exam preparations and Cisco certification application, do not hesitate to visit our Vcedump.com to find your solutions here.