Exam Details
Exam Code
:210-250Exam Name
:Cisco Cybersecurity FundamentalsCertification
:Cisco CertificationsVendor
:CiscoTotal Questions
:1157 Q&AsLast Updated
:Nov 03, 2022
Cisco Cisco Certifications 210-250 Questions & Answers
-
Question 1131:
Which of the following are examples of vulnerabilities?
A. SQL injection
B. Command injection
C. Cross-site scripting (XSS)
D. Cross-site request forgery (CSRF)
-
Question 1132:
Match the NGFW requirement to its description.
Select and Place:

-
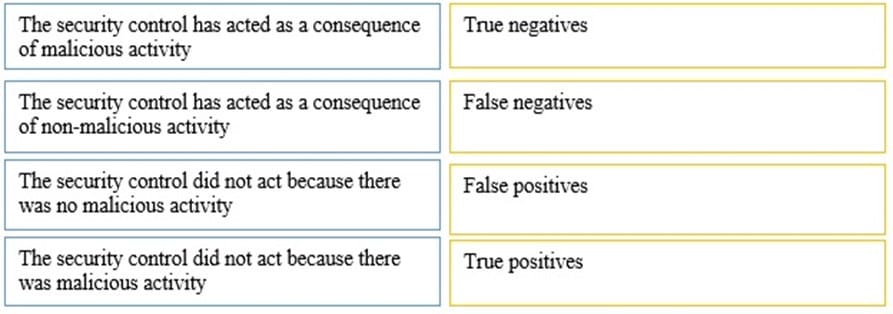
Question 1133:
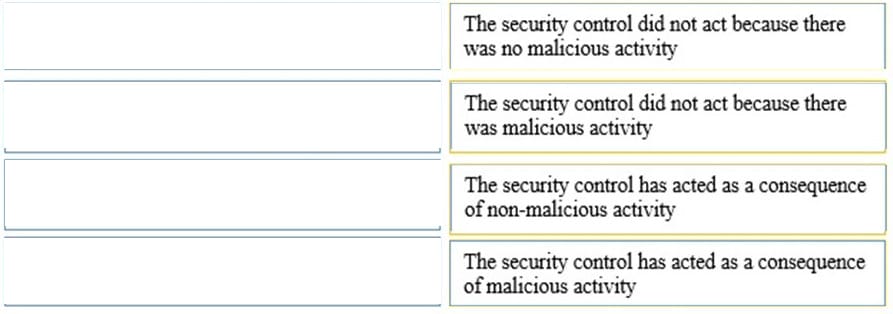
Match the security control term with its description.
Select and Place:
-
Question 1134:
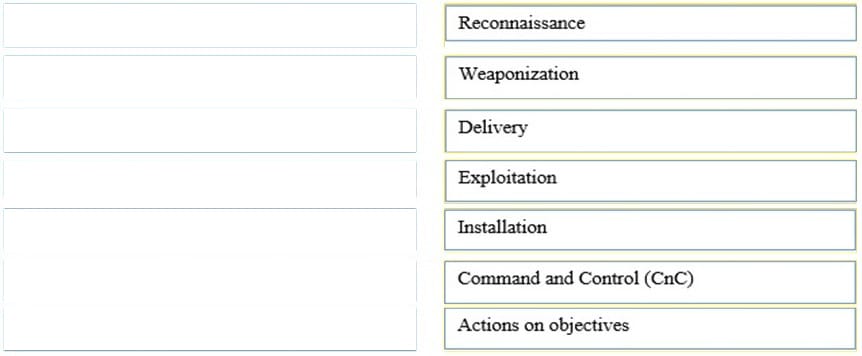
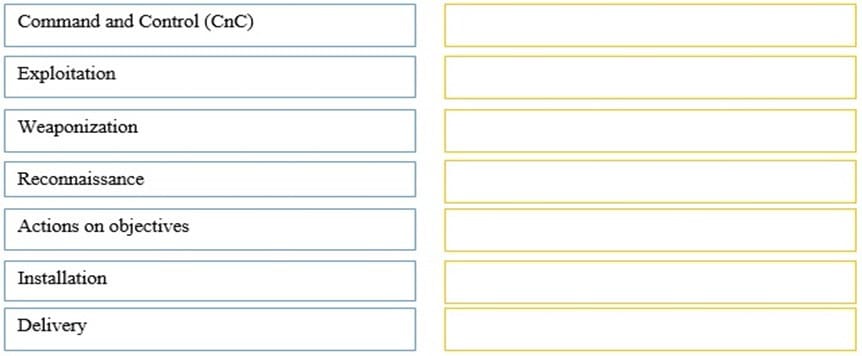
Arrange the seven stages of the cyber kill chain in order.
Select and Place:
-
Question 1135:
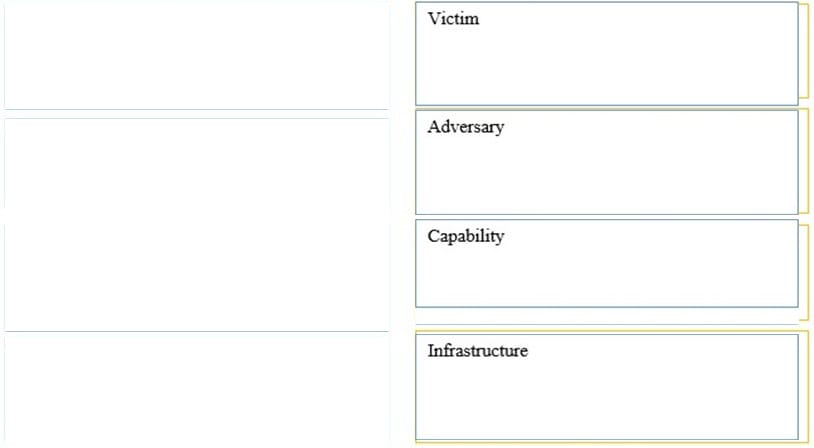
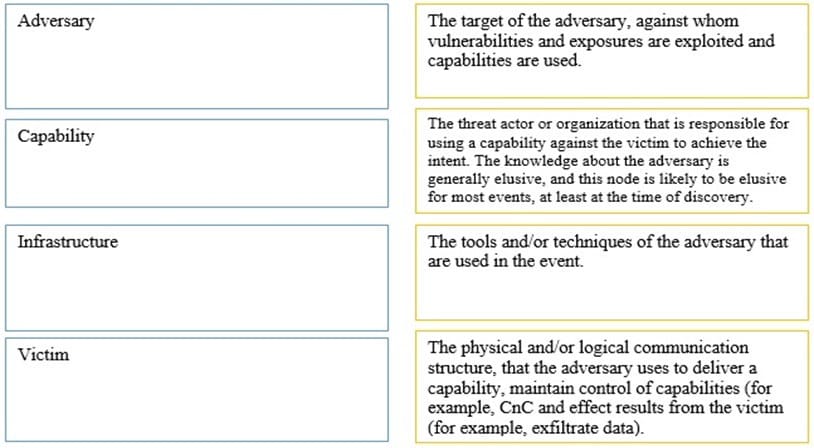
Match the four nodes of the diamond model for intrusion analysis with the proper description.
Select and Place:
-
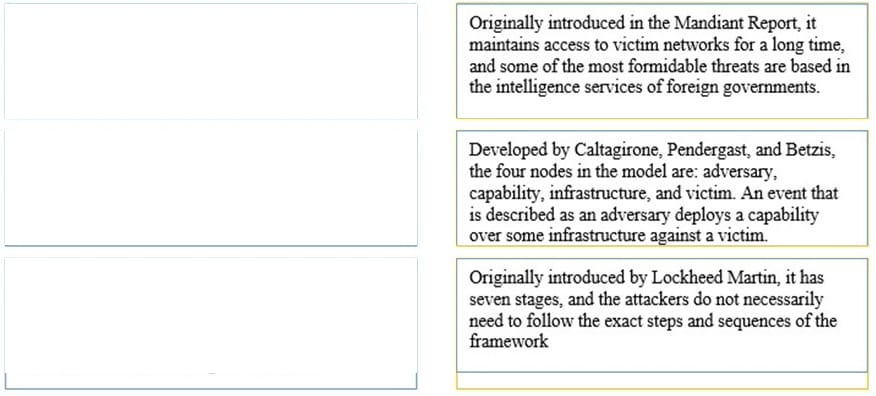
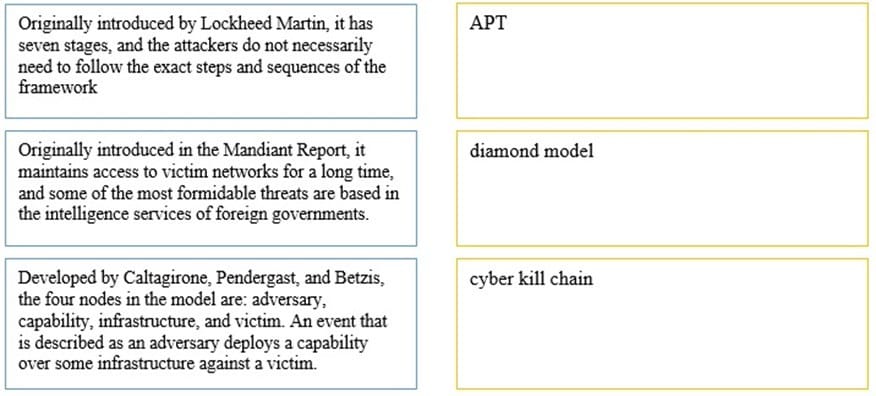
Question 1136:
Match the following characteristics with the appropriate threat model.
Select and Place:
-
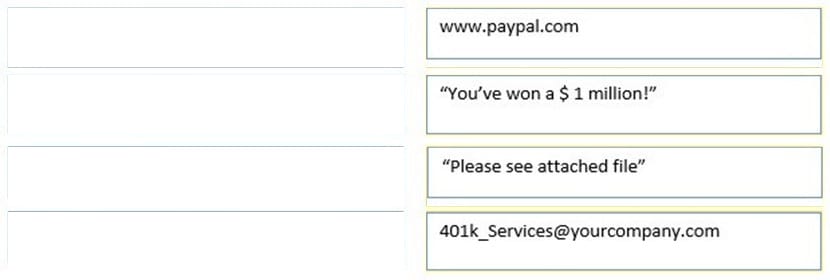
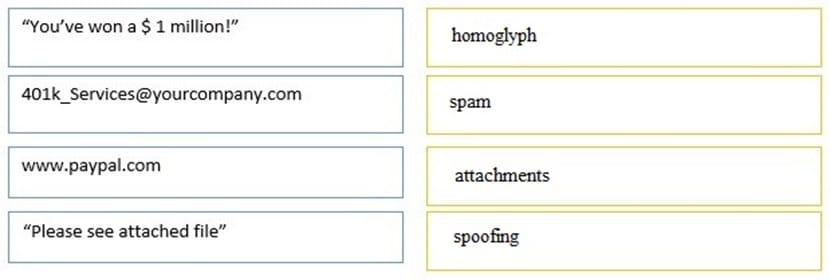
Question 1137:
Match the type of attack to its example.
Select and Place:
-
Question 1138:
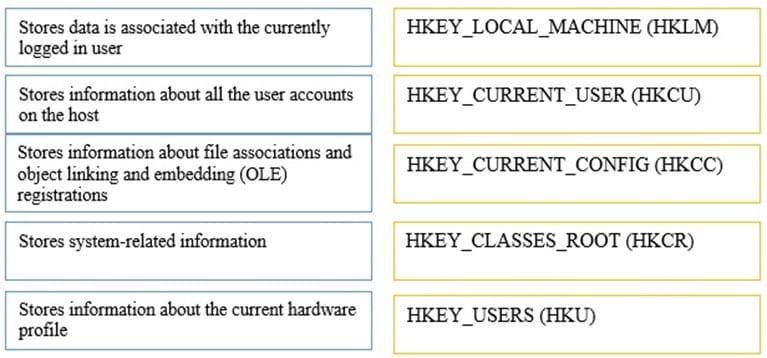
Match the following Windows registry hives to the correct descriptions.
Select and Place:
-
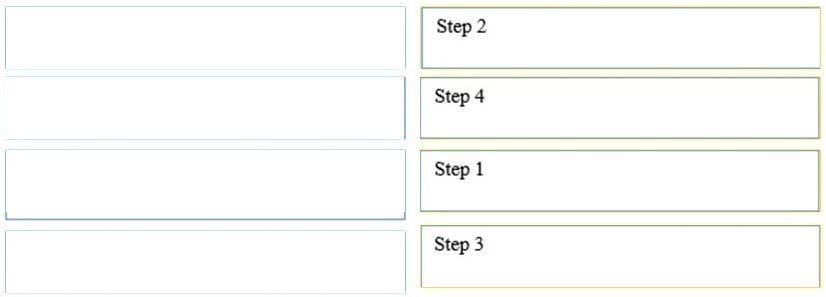
Question 1139:
Match the step number with the action when starting the Services Control Manager using the Windows Interface.
Select and Place:

-
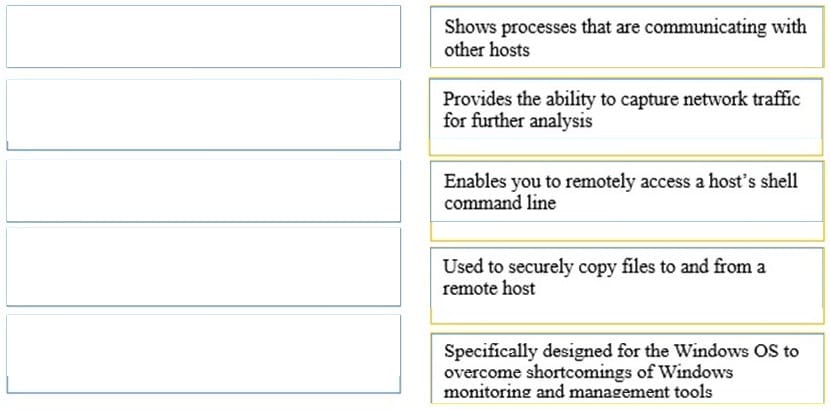
Question 1140:
Match each tool or application with its description.
Select and Place:

Related Exams:
300-915
Developing Solutions using Cisco IoT and Edge Platforms (DEVIOT)300-920
Developing Applications for Cisco Webex and Webex Devices (DEVWBX)352-011
Cisco Certified Design Expert Practical500-052
Cisco Unified Contact Center Express500-173
Designing the FlexPod Solution (FPDESIGN)500-174
Implementing and Administering the FlexPod Solution (FPIMPADM)500-201
Deploying Cisco Service Provider Mobile Backhaul Solutions500-210
SP Optical Technology Field Engineer Representative500-220
Cisco Meraki Solutions Specialist500-230
Cisco Service Provider Routing Field Engineer
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Cisco exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 210-250 exam preparations and Cisco certification application, do not hesitate to visit our Vcedump.com to find your solutions here.