Exam Details
Exam Code
:1Z0-160Exam Name
:Oracle Database Cloud ServiceCertification
:Oracle DatabaseVendor
:OracleTotal Questions
:86 Q&AsLast Updated
:Apr 25, 2024
Oracle Oracle Database 1Z0-160 Questions & Answers
-
Question 31:
Which two must be true when you migrate an Oracle Database 12.1.0.2 non-CDB to a database that is running in a Database as a Service (DBaaS) instance on Oracle Cloud by using the Remote Cloning method?
A. The non-CDB may be opened in READ WRITE mode as long as ARCHIVELOG is enabled.
B. The database link owner must have the CREATE PDB system privilege.
C. The source platform must have the same endian format.
D. The non-CDB must be in archivelog mode.
E. The non-CDB must be opened in READ ONLY mode.
F. The database link owner must have the CREATE PLUGGABLE DBsystem privilege.
-
Question 32:
You want to control network traffic among your DBaaS instances.
Which two statements are true about network groups?
A. By default, the DBaaS instances in a network group are accessible from hosts outside the network group.
B. You can add a DBaaS instance to a network group, but this enables communication only within this network group.
C. You can add a DBaaS instance to a network group, thus enabling communication with all other DBaaS instances both inside and outside the network group.
D. You can create a network group to enable unrestricted communication among your DBaaS instances.
E. DBaaS prevents network groups from having unrestricted communication among DBaaS instances.
-
Question 33:
You use GUI tools on the Virtual Machine to create and administer the Database as a Service (DBaaS) databases.
You wish to use the Oracle Database Configuration Assistant (DBCA) to create a database instance. To run DBCA, you will need to use an SSH connection.
You need to perform several steps to establish this connection in DBCA and to create the database.
What are two of these steps?
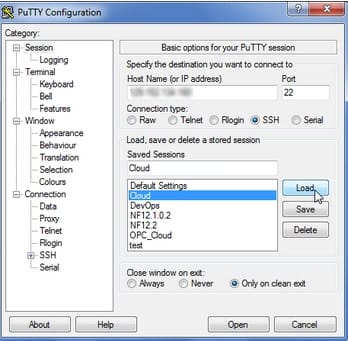
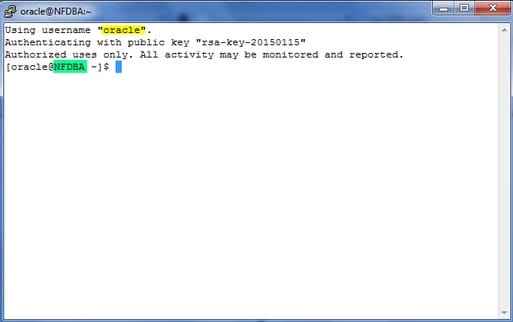
A. Connect to the DBaaS instance with the SSH terminal session as the oracle user.
B. Configure a PuTTY or SSH session to perform X11 forwarding.
C. Install an Xterminal program if required.
D. Update the tnsnames.ora file with the name of the service to which you want to connect.
-
Question 34:
You want to apply a patch to your Oracle Database Cloud - Database as a Service.
What command will you execute to patch your database instance?
A. dbaascli dbpatchm --run -config
B. dbaascli dbpatchm --run -setup
C. dbaascli dbpatchm --run -apply
D. dbaascli dbpatchm --run -patch
-
Question 35:
Which statement is true about Oracle Database Schema Service or Oracle Database Cloud Service (DBCS)?
A. Oracle Database Cloud Service does not require database administrators to administer the database.
B. Oracle Database Schema Service requires a database administrator to administer the schemas.
C. Oracle Database Cloud Service provides complete dedicated database instances with full administrative control for a subscriber.
D. Oracle Database Schema Service provides database schemas with full administrative control for a subscriber.
-
Question 36:
You created a Database Deployment and predefined security rules were generated.
Which two predefined security rules were generated when you created the Database Deployment?
A. The ora_p2_ssh security rule for the public-internet security IP list was created to communicate with the ora_dbpredefined network group over SSH.
B. The ora_db_public security rules to manage database access through the default port 1521 and the ora_db_admin security rules for SSH connection via SQL*Net through port 5500 were created.
C. The ora_access db security rule for SSH connection via PuTTY is created to configure network rules and ora_access_consolefor HTTPS access to Oracle Cloud Services Console.
D. No security rules are created by default and users must manually configure all access rules.
E. The ora_p2_dblistener security rule for the public-internet security IP list (any host on the Internet) was created to communicate with the ora_dbpredefined network group over SQL*Net.
-
Question 37:
How do you access “none default ports” on a Database Deployment's compute node?
A. Review a file called portlist.ini in your installation directory to acquire the list of “none default ports” that are assigned to your compute node.
B. File a service request with your Oracle Database Cloud Service support team to have the “none default ports” opened for use.
C. Create an SSH tunnel to the “none default port”.
D. All communication to Oracle Database Cloud Service must be configured only by using the default ports that are assigned to your compute node during the installation of your Database Deployments.
-
Question 38:
Which two problems indicate that you should consider scaling up your Database Deployment that hosts an Oracle Database 12c multitenant container database (CDB) with four pluggable databases (PDBs)?
A. shortage of CPU for two PDBs in the CDB
B. shortage of I/O bandwidth for the parallel queries that are issued by the CDB instance
C. shortage of memory for the Database Deployment
D. shortage of memory in the Shared Pool of the CDB
E. shortage of CPU for the Database Deployment
-
Question 39:
Which two steps would you perform to restore and recover a database from the most recent backup?
A. Disable the scheduled backup configuration.
B. Disable the scheduled recovery configuration.
C. Perform the restore with the dbaascli orec --args -latestcommand.
D. Perform the restore with the dbaascli orec --args -lastcommand.
E. Perform the restore with the dbaascli orec --args -stop -lastcommand.
F. Perform the restore with the dbaascli orec --args -close -lastcommand.
-
Question 40:
Which statement is true about security rules for Database Deployments?
A. They are used only for configuring external server access to Database Deployments and do not impact how security lists communicate.
B. They define a specific communication path, which consists of a source, destination, and protocol-port combination over which communication is allowed.
C. They are used to map an external user to a database user to allow the user to communicate with and access the database.
D. They are used to encrypt communication between Database Deployments.
Related Exams:
1Z0-909
MySQL 8.0 Database Developer1Z0-931
Oracle Autonomous Database Cloud 2019 Specialist1Z0-920
MySQL 2019 Implementation Essentials1Z0-908
MySQL 8.0 Database Administrator1Z0-817
Upgrade OCP Java 6, 7 & 8 to Java SE 11 Developer1Z0-116
Oracle Database Security Administration1Z0-083
Oracle Database Administration II1Z0-082
Oracle Database Administration I1Z0-750
Oracle Application Express 18: Developing Web Applications1Z0-073
Oracle Database 12cR2 Advanced Administration
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only Oracle exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 1Z0-160 exam preparations and Oracle certification application, do not hesitate to visit our Vcedump.com to find your solutions here.