156-215.81.20 Exam Details
-
Exam Code
:156-215.81.20 -
Exam Name
:Check Point Certified Security Administrator - R81.20 (CCSA) -
Certification
:Checkpoint Certifications -
Vendor
:CheckPoint -
Total Questions
:677 Q&As -
Last Updated
:May 26, 2026
CheckPoint 156-215.81.20 Online Questions & Answers
-
Question 401:
From the Gaia web interface, which of the following operations CANNOT be performed on a Security Management Server?
A. Verify a Security Policy
B. Open a terminal shell
C. Add a static route
D. View Security Management GUI Clients -
Question 402:
Which of the following is a valid deployment option?
A. CloudSec deployment
B. Disliked deployment
C. Router only deployment
D. Standalone deployment -
Question 403:
The SIC Status "Unknown" means
A. There is connection between the gateway and Security Management Server but it is not trusted.
B. The secure communication is established.
C. There is no connection between the gateway and Security Management Server.
D. The Security Management Server can contact the gateway, but cannot establish SIC. -
Question 404:
When attempting to start a VPN tunnel, in the logs the error 'no proposal chosen' is seen numerous times. No other VPN-related log entries are present. Which phase of the VPN negotiations has failed?
A. IKE Phase 1
B. IPSEC Phase 2
C. IPSEC Phase 1
D. IKE Phase 2 -
Question 405:
Which one of the following is the preferred licensing model? Select the Best answer.
A. Local licensing because it ties the package license to the IP-address of the gateway and has no dependency of the Security Management Server.
B. Central licensing because it ties the package license to the IP-address of the Security Management Server and has no dependency of the gateway.
C. Local licensing because it ties the package license to the MAC-address of the gateway management interface and has no Security Management Server dependency.
D. Central licensing because it ties the package license to the MAC-address of the Security Management Server Mgmt-interface and has no dependency of the gateway. -
Question 406:
Which one of the following is TRUE?
A. One policy can be either inline or ordered, but not both.
B. Inline layer can be defined as a rule action.
C. Ordered policy is a sub-policy within another policy.
D. Pre-R80 Gateways do not support ordered layers. -
Question 407:
What are the two types of NAT supported by the Security Gateway?
A. Destination and Hide
B. Source and Destination
C. Static and Source
D. Hide and Static -
Question 408:
What command from the CLI would be used to view current licensing?
A. cplic print
B. show license -s
C. fw ctl tab -t license -s
D. license view -
Question 409:
What is required for a site-to-site VPN tunnel that does not use certificates?
A. Unique Passwords
B. Pre-Shared Secret
C. SecureID
D. RSA Token -
Question 410:
Study the Rule base and Client Authentication Action properties screen.
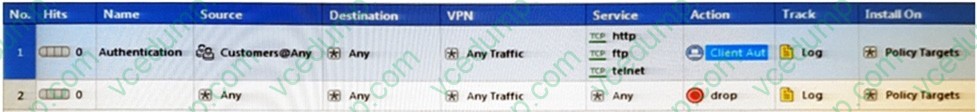
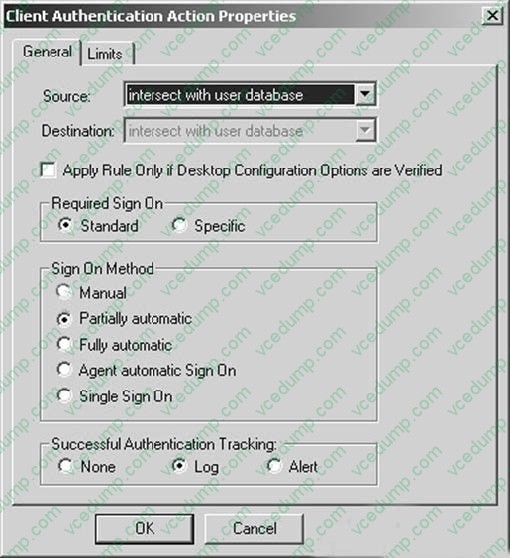
After being authenticated by the Security Gateways, a user starts a HTTP connection to a Web site. What happens when the user tries to FTP to another site using the command line? The:
A. user is prompted for authentication by the Security Gateways again.
B. FTP data connection is dropped after the user is authenticated successfully.
C. user is prompted to authenticate from that FTP site only, and does not need to enter his username and password for Client Authentication
D. FTP connection is dropped by Rule 2.
Related Exams:
-
156-110
Check Point Certified Security Principles Associate (CCSPA) -
156-115.80
Check Point Certified Security Master - R80 -
156-215
Check Point Security Administration NGX -
156-215.1
Check Point Certified Security Administrator NGX -
156-215.70
Check Point Certified Security Administrator R70 -
156-215.71
Check Point Certified Security Administrator R71 -
156-215.75
Check Point Certified Security Administrator -
156-215.80
Check Point Certified Security Administrator (CCSA) -
156-215.81
Check Point Certified Security Administrator - R81 (CCSA) -
156-215.81.20
Check Point Certified Security Administrator - R81.20 (CCSA)
Tips on How to Prepare for the Exams
Nowadays, the certification exams become more and more important and required by more and more enterprises when applying for a job. But how to prepare for the exam effectively? How to prepare for the exam in a short time with less efforts? How to get a ideal result and how to find the most reliable resources? Here on Vcedump.com, you will find all the answers. Vcedump.com provide not only CheckPoint exam questions, answers and explanations but also complete assistance on your exam preparation and certification application. If you are confused on your 156-215.81.20 exam preparations and CheckPoint certification application, do not hesitate to visit our Vcedump.com to find your solutions here.